With DigitalXRAID’s CREST and CHECK certified penetration testing services, you’ll uncover vulnerabilities, strengthen your security posture, and meet compliance, all without disrupting your operations.
Penetration Testing Services from CREST and CHECK Certified Experts
Cyber threats don’t wait for your defences to be ready; they exploit what’s weak.
DigitalXRAID’s Penetration Testing Services uncover vulnerabilities that attackers target before they can be used against you. Our expert team conducts simulated attacks across your networks, applications, cloud environments, and users, delivering clear, actionable insights that help you prioritise and remediate risk fast.
Led by CREST and CHECK accredited security professionals, our tests are tailored to your infrastructure and compliance needs. Whether you’re securing a new launch, preparing for an audit, or validating existing controls, we provide deep technical assurance and real-world context to support your cyber resilience strategy.
Our Penetration Testing Services
Why Leading Organisations Choose DigitalXRAID for Pen Testing
When you need to be certain your defences will hold, you need a partner that brings credibility, clarity, and deep technical assurance.

CREST and CHECK Certified Security Specialists
Every assessment is delivered by CREST and CHECK accredited professionals with proven real-world expertise.
Aligned with methodologies from OWASP, OSINT, CREST and more
Our methodologies follow leading global standards from OWASP Top 10, OSINT and CREST, amongst others..
Threat Intelligence-Led Testing
We emulate real-world adversaries to give you actionable, relevant security insight.
Clear, Risk-Based Reporting
Prioritised findings, plain-language summaries, and remediation guidance you can act on.
Flexible, Client-Focused Delivery
No two infrastructures (or deadlines) are the same. We shape the scope, timing, and format of every test around what works for your business.
Trusted Across Regulated Sectors
From NHS trusts to fintech firms, we’ve helped organisations across regulated industries stay secure, audit-ready, and confident under pressure.
Penetration Testing Service Options
Essentials Penetration Test
- DigitalXRAID will scan your network, system, API or web application CVEs using CREST approved tools
- Our CREST accredited Security Testing team will then run manual tests to check for any false positives
- You will receive a pen test report of the scan and the manual checks, including advice for remediation, and a business risk score, all compiled by our testing experts
- We will protect your business efficiently and faster with a tool-driven methodology
Full CREST & CHECK Accredited Penetration Test
- DigitalXRAID will follow a full CREST methodology, fully testing your network, system or application, leaving no stone unturned
- CREST & CHECK accredited testers will utilise advanced techniques to simulate attack scenarios, uncover hidden vulnerabilities, and employ custom exploitation techniques
- You will receive a comprehensive pen test report, including in-depth consultancy for each issue identified via the OrbitalX portal
- Access to the full OrbitalX portal which enables advanced reporting with custom reports and remediation tracking
What's Included? Penetration Testing Service Options

Consultancy

Delivery

Reporting
Penetration Test
Essentials
Penetration Test
Full CREST & CHECK Accredited
How Our Pen Testing Service Works
We keep the process straightforward, no jargon, no friction. From first conversation to final retest, we move with you: clear, collaborative, and always aligned to what matters most.

What You Get with Our Penetration Testing Services
- Manual and automated testing using CREST accredited methodologies and real-world attack techniques
- Clear, risk-prioritised reporting with technical detail and executive summaries for fast action
- Step-by-step remediation guidance to help your team fix issues quickly and effectively
- Optional retesting to validate fixes and confirm you’ve closed critical gaps
What is penetration testing?
Penetration Testing Service
Pen testing examines and evaluates an organisation’s digital infrastructure – networks, systems and web applications – to identify potential threats to security systems. With the use of genuine ethical hacking techniques, our team of CREST penetration testing certified experts conduct a simulated attack and are able to identify vulnerabilities in your infrastructure and provide you with the knowledge you need to prevent future attacks. Our penetration testing methodology is closely aligned with the OWASP (Open Web Application Security Project®) Top 10.
We have never conducted a systems pen test that didn’t find at least one vulnerability..
Pen tests identify:
- Where a hacker might target you
- How they would attack your systems
- How your defences would cope
- The potential impact of a breach
Learn more on penetration testing as a service.

What Is Penetration Testing and Why It Matters
Want to see how penetration testing works and why it’s essential? In this short video, our security experts explain what’s involved, how it protects your business, and what to expect from a DigitalXRAID engagement.
A standard penetration testing process will look for a range of vulnerabilities within your IT system
Insecure setup or configuration of networks
Our security professionals will attempt to breach your systems by looking for weak passwords and exploit vulnerabilities to open ports, unpatched applications and incorrectly set user privileges.
Incorrect encryption and authentication
Article 32 of the UK GDPR includes encryption as an example of an appropriate technical measure to secure data. Are you encrypting data to a sufficient standard?
Code and command injection
We’ll check that your web forms are built to protect against SQL injection attacks, and find how they behave when someone tries to interfere with them.
Session management
Cookies and sessions tokens are used to make applications more user friendly, but they can be exploited for malicious purposes, making you vulnerable to attack.
30%
of all phishing emails are unwittingly opened by users
92%
of network perimeters are breached during penetration testing
16%
of penetration testing found evidence of previous breaches

A penetration of a network costs a business over £2M.
Can your business sustain such a significant spend?
Your clients stolen data may be sold on the dark web
Is your brand strong enough to withstand such a blow?
69% of customers said they would never return
Customers are less likely to buy from a breached organisation.
When should you invest in Penetration Testing?
IT and Security leaders don’t wait for a breach to test their defences; they validate them proactively. If any of these sound familiar, it’s time to act.

You Handle Sensitive or Regulated Data: If you store customer, financial, or health data, penetration testing isn’t optional; it’s expected.
You’re Preparing for Compliance or Audit: Pen testing helps meet standards like ISO 27001, PCI DSS, and Cyber Essentials and proves it.
You’re Launching a New App or Infrastructure: Pre-launch testing reduces reputational risk and keeps rollouts on schedule.
You’ve Never Had a Pen Test (or It’s Been a While): Threats evolve constantly, and annual testing is the minimum best practice advice – for most regulated industries this would need to be more frequent.
You’ve Made Major Changes: Migrations, updates, or vendor integrations can introduce unexpected vulnerabilities.
You Need Assurance for Stakeholders: Clear, independent testing builds trust with execs, clients, and investors.

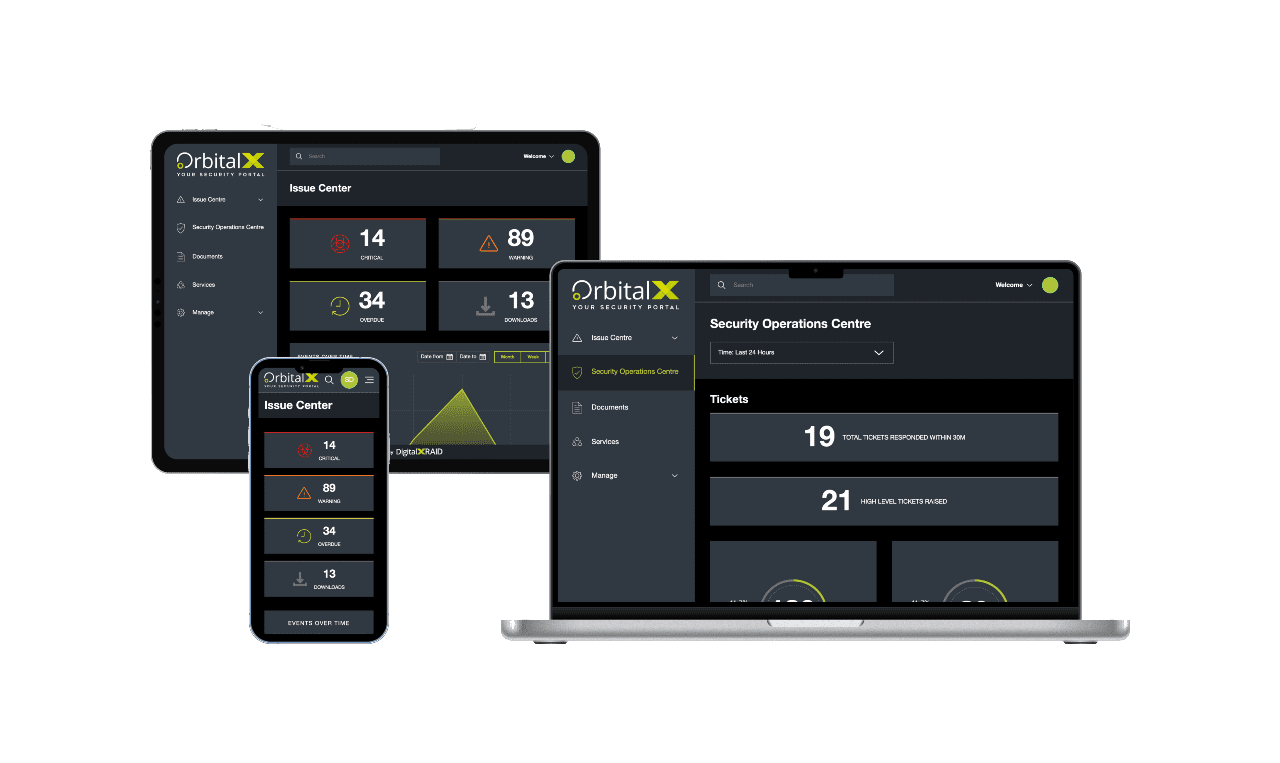
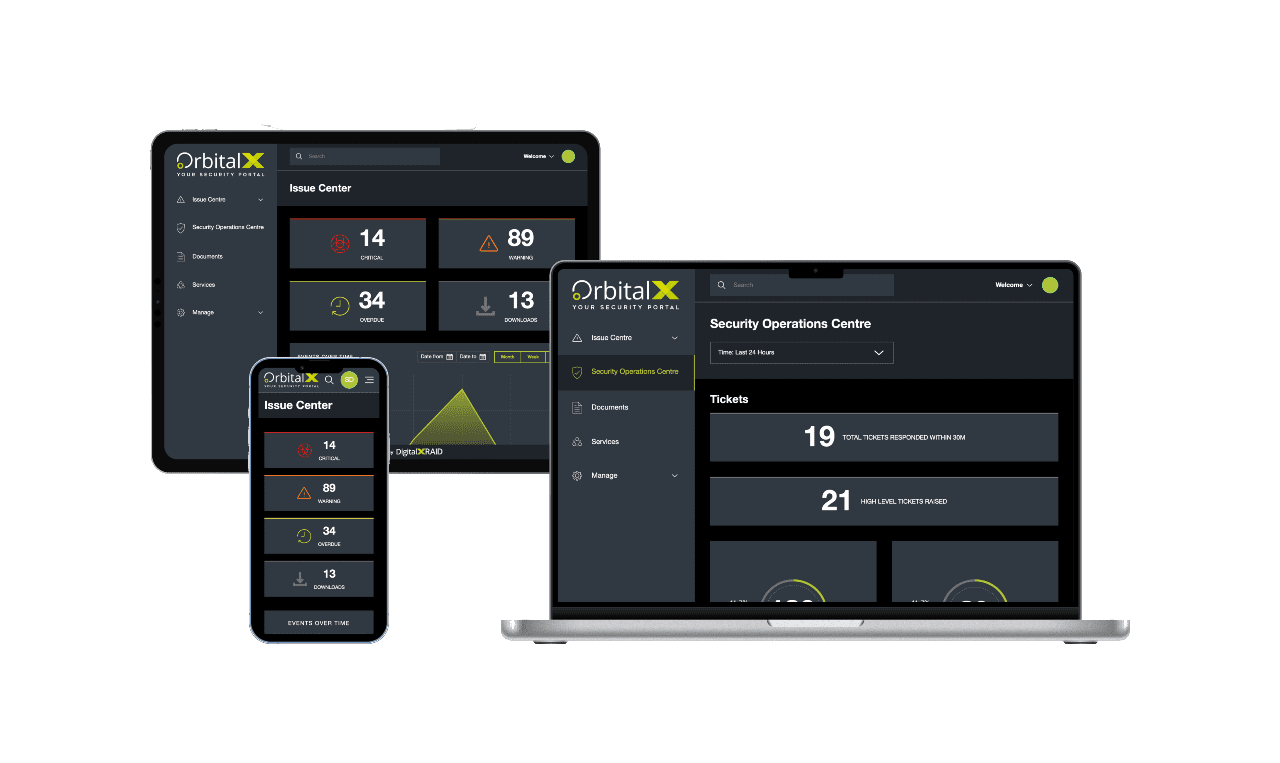
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
“DigitalXRAID’s penetration testing provided valuable assurance that our Canvas iPaaS platform is resilient against cyber threats. Their expert team conducted a thorough and professional assessment, reinforcing our commitment to proactive security measures. Regular penetration testing remains a key part of our cybersecurity strategy to ensure ongoing protection for our customers’ data”
Igor Kostian, CTO, ConnectMyApps
Benefits of Penetration Testing Services
Vulnerabilities don’t just pose technical risks; they’re business risks. Penetration testing gives you the insight, assurance, and evidence to act with confidence.

Prove Your Security Posture
Demonstrate to clients, execs, and auditors that your defences are robust, validated, and proactively tested.
Reduce Cyber Risk Exposure
Uncover vulnerabilities before attackers do and fix them before they cause disruption, downtime, or data loss.
Support Frameworks & Regulatory Compliance
Meet penetration testing requirements for ISO 27001, PCI DSS, Cyber Essentials, DORA, NIS2 and more with CREST accredited reporting.
Avoid the Cost of a Breach
Identify security gaps early and avoid the operational, reputational, and financial fallout of preventable incidents.
Focus Your Security Spend
Get clear, risk-ranked results so your team knows where to invest time, budget, and resources and where not to.
Independent, Expert Insight
Gain an outside perspective from security professionals who think like attackers and speak the language of auditors.
Cyber Security Experts
Our team comprises professionals selected for their industry expertise and outstanding work ethic, allowing us to provide you with market leading cyber security services.
Long term solutions
We deliver long term solutions to ensure your company is protected. A longstanding partnership with the right cyber security provider is invaluable.
Personal touch
Your business is unique. We will listen and work closely with you to understand your challenges, identify the vulnerabilities that are particular to your business, and put in place tailored countermeasures.
Cyber security specialists
Our expertise, experience and knowledge base puts us in the ideal position to deliver industry leading protection against existing and emerging cyber threats.
Managed Penetration Testing Service
No single test or report is ever going to be enough to secure an organisation against the complex cyber threat landscape. As your Managed Security Service Provider (MSSP) we will construct a developed, bespoke and reactive plan to take care of your entire cyber security requirements now and into the future.
- Your trusted partners, we’ll deliver guidance, support and recommendations based on real evidence and genuine assessment of your business needs.
- We’ll continually test your networks with our continuous penetration testing, identify exploitable factors, and upgrade your facilities to meet your evolving needs.
- We’ll make sure your cyber protection remains robust, comprehensive and cutting-edge.
Find out more about our managed service:
Managed cyber security packagesDiscover the Knowledge Base
Frequently Asked Questions About Penetration Testing
Think of penetration testing as a rehearsal for a cyberattack, only this time, the attackers are on your side. It’s a controlled, ethical attempt to uncover weak spots across your systems, applications, and infrastructure. For many organisations, it’s the difference between guessing you’re secure and knowing it.
There’s no one-size-fits-all answer, and that’s the point. At a minimum, and at the recommendation of organisations like CREST, most businesses test once a year. But if you’ve rolled out new systems, onboarded a cloud platform, or need to meet compliance requirements, it’s wise to test more frequently. The more things change, the sooner you should test.
Vulnerability scans are like smoke detectors; they flag issues. Pen tests? They’re the fire drill. Scans spot known risks; pen testers dig deeper, using real-world tactics to see what an attacker could actually exploit. Together, they offer layered insight, but only one gives you a true sense of exposure.
Not all pen tests are created equal; the right approach depends on what you’re securing and why. Here’s a breakdown in plain English:
- External Network Testing: Simulates how a real attacker would approach your public-facing systems, such as firewalls, exposed servers, or VPNs.
- Internal Network Testing: Mimics what happens after a breach or by a malicious insider, testing lateral movement, privilege escalation, and internal access.
- Web Application Testing: Probes login pages, user roles, session handling, and logic flaws that could expose customer data or enable unauthorised actions.
- Mobile Application Testing: Focuses on mobile-specific risks like insecure storage, broken cryptography, or overly permissive permissions in iOS and Android apps.
- Cloud Security Testing: Reviews cloud setups like AWS and Azure for access control issues, misconfigured buckets, or exposed credentials.
- Social Engineering: Assesses how your people respond to deception, from phishing emails to phone-based pretexting or in-person impersonation.
- Red Teaming: A stealthier, full-scope simulation where we act like a real adversary, testing both your technology and your team.
It shouldn’t, and if there’s even a small chance it could, we’ll plan around it. Good pen testing is as much about coordination as it is code. We’ll agree on all boundaries up front. Think of it as a safe, contained risk, with none of the fallout.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Protect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.