DigitalXRAID’s mobile app penetration testing services uncover critical vulnerabilities in Android and iOS applications, so helping you fix risks before attackers find them.
Mobile Apps Are Now Prime Targets for Attackers
Most organisations focus on web or network security, but what about your mobile apps?
From insecure APIs to unencrypted data and flawed authentication, mobile apps expose new paths for attackers.
Whether it’s a customer-facing app or an internal tool, mobile vulnerabilities can compromise sensitive data, user trust, and compliance. And with every release, the risk grows.
Just some of the customers that trust DigitalXRAID to protect their business from cyber threats
Why Choose DigitalXRAID for Mobile Application Pen Testing?
Our mobile app penetration tests are trusted by organisations handling sensitive data, operating in regulated sectors, or delivering high availability user experiences.
Your tests are conducted by expert testers certified by CREST, the gold standard for penetration testing quality and integrity.
We simulate real attack scenarios across Android and iOS to identify risks in authentication, data storage, APIs, and app logic.
Our assessments cover the full OWASP Mobile Top 10, ensuring your app is tested against the most critical mobile security threats.
We go beyond the app itself, evaluating the entire ecosystem, including APIs and back-end services, for end-to-end security.
Every finding is explained with severity ratings, risk context, and remediation steps your team can act on quickly.
Need results for a release deadline? We offer flexible scoping and fast delivery options aligned with your development cycles.
75%
of mobile apps fail basic security tests
2/3
of organisations have been breached via mobile
50bn
is the estimated cost of mobile cyber breaches
How Mobile Application Penetration Testing Works
Our mobile pen testing process follows a structured, standards-based approach, including OWASP Mobile Top 10 and CREST methodologies, to uncover real world vulnerabilities across Android and iOS applications.

Information Gathering
We begin by passively and actively collecting data about the mobile application, including metadata, app permissions, third-party libraries, and exposed services. This sets the foundation for a focused and thorough test.
Interaction with the Mobile Platform
Our testers analyse how the app interacts with the mobile operating system, inspecting the use of device features, file systems, clipboard access, and inter-process communication to identify unsafe behaviours.
Local Data Storage
We assess how sensitive data (like login credentials or personal information) is stored locally. This includes reviewing shared preferences, local databases, cache files, and storage encryption to detect data leakage risks.
Communication with Trusted Endpoints
We inspect how the app communicates with its backend infrastructure, including the use of HTTPS, certificate validation, token management, and potential for man-in-the-middle (MITM) attacks or session hijacking.
Authentication Testing
Our team tests the robustness of login flows and authentication mechanisms. This includes identifying issues like weak credential enforcement, insecure password storage, and poor session management.
Authorisation Testing
We verify whether users can access only what they’re supposed to. This step includes role based access checks, privilege escalation testing, and broken access control vulnerabilities.


Exploit Mitigation Evaluation
We check for the presence (or absence) of mobile security controls such as code obfuscation, root/jailbreak detection, secure coding practices, and OS-level hardening, all vital to protect the app post-deployment.
Anti-Tampering & Anti-Reversing Protections
Using reverse engineering techniques, we evaluate whether your app resists unauthorised modifications. This includes analysis of APK/IPA files, debugger detection, and resistance to runtime manipulation.
Reporting & Walkthrough
Once testing is complete, we provide a comprehensive report tailored for both technical teams and executives. It includes detailed risk descriptions, exploit paths, remediation guidance, and business impact analysis. A full handover session ensures your team understands the findings and can prioritise fixes effectively.
What’s Included in Our Mobile Application Pen Testing Services
Our mobile app penetration tests identify security flaws across iOS and Android platforms, APIs, and supporting infrastructure, helping you protect users, data, and compliance.
Every engagement includes:
- OWASP Mobile Top 10 coverage – Full testing aligned with the latest mobile security risks.
- Static & dynamic analysis – Review of source code (if provided) and app behaviour in runtime.
- API & backend testing – Examination of how the app interacts with connected systems and data.
- Authentication & session management – Assessment of login flows, session handling, and token security.
- Platform-specific testing – iOS and Android tested for OS-specific misconfigurations or exploits.
- Detailed reporting & remediation guidance – Clear vulnerability ratings and recommended actions.
All testing is conducted by CREST and CHECK certified ethical hackers using industry recognised methodologies, ensuring your mobile apps are secure, compliant, and resilient to evolving threats.

What Are The Benefits of Mobile Application Penetration Testing?
Mobile app pen testing helps identify critical vulnerabilities across iOS and Android environments, before attackers can exploit them. It ensures your app is secure, compliant, and trusted by users.

Key benefits include:
- Uncover app-specific vulnerabilities – Detect issues like insecure storage, weak encryption, or broken authentication.
- Protect user data & privacy – Prevent exposure of sensitive information through APIs or app logic flaws.
- Validate secure coding practices – Ensure your development team is following OWASP Mobile Top 10 guidance.
- Meet compliance & regulatory demands – Support ISO 27001, GDPR, and industry-specific security requirements.
- Build user trust – Demonstrate your commitment to security with third-party validation.
- Reduce reputational risk – Prevent breaches that can damage brand credibility and customer loyalty.
Mobile app penetration testing is essential for businesses delivering customer-facing apps, processing sensitive data, or operating in regulated industries.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Is Mobile Application Penetration Testing Right for Your Business?
If your organisation delivers mobile apps to customers, partners, or employees, especially those handling sensitive data, mobile app pen testing is no longer optional. It’s a critical part of securing your wider attack surface.
Public Facing Mobile Applications
Apps available via the App Store or Google Play are prime targets for attackers. Testing helps uncover vulnerabilities before they’re exploited.
Apps Handling Sensitive Data
If your app collects or processes personal, financial, or health-related data, mobile pen testing supports compliance with GDPR, supports ISO 27001 certification, and more.
Custom Built or In-House Apps
Whether customer facing or internal use, bespoke mobile apps often bypass traditional security reviews, increasing risk.


Frequent Release Cycles or CI/CD Pipelines
Agile teams pushing regular app updates need testing baked into the cycle to avoid releasing new vulnerabilities.
Third-Party Integrations & APIs
Integrations with payment systems, CRMs, or other services create new attack paths. Testing helps secure them.
Security Assurance for Stakeholders
Demonstrate proactive risk management to investors, partners, or auditors with a CREST and CHECK certified mobile pen test report.
“DigitalXRAID understood our business and specific needs from the start, and provided a professional service, answering questions if they arose and delivering consistent communication throughout the process. The Application Penetration Testing service has provided us with complete peace of mind that our application is secure and that our users’ data is protected, which is our upmost concern and our pledge to customers. Following on from our initial penetration testing, we look forward to working with DigitalXRAID on further security projects in the future ensuring complete security protection for the business.””
3Fun
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734

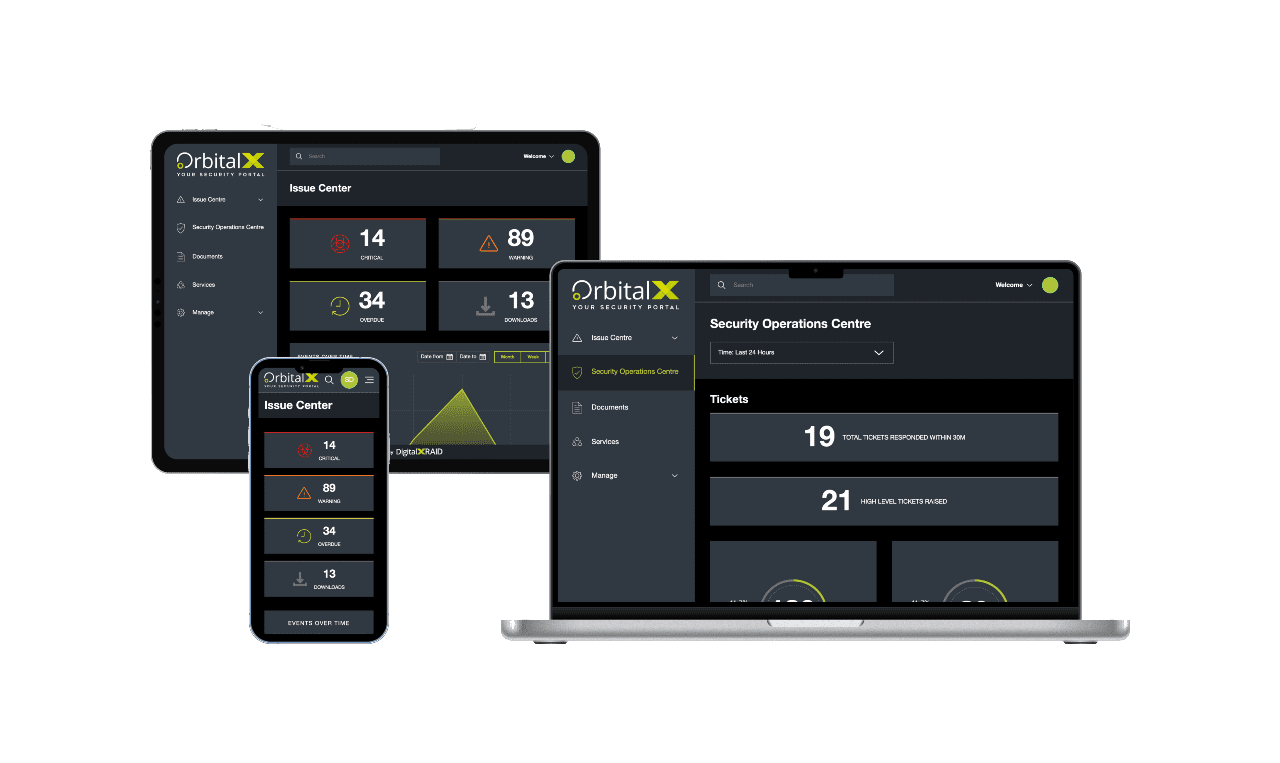
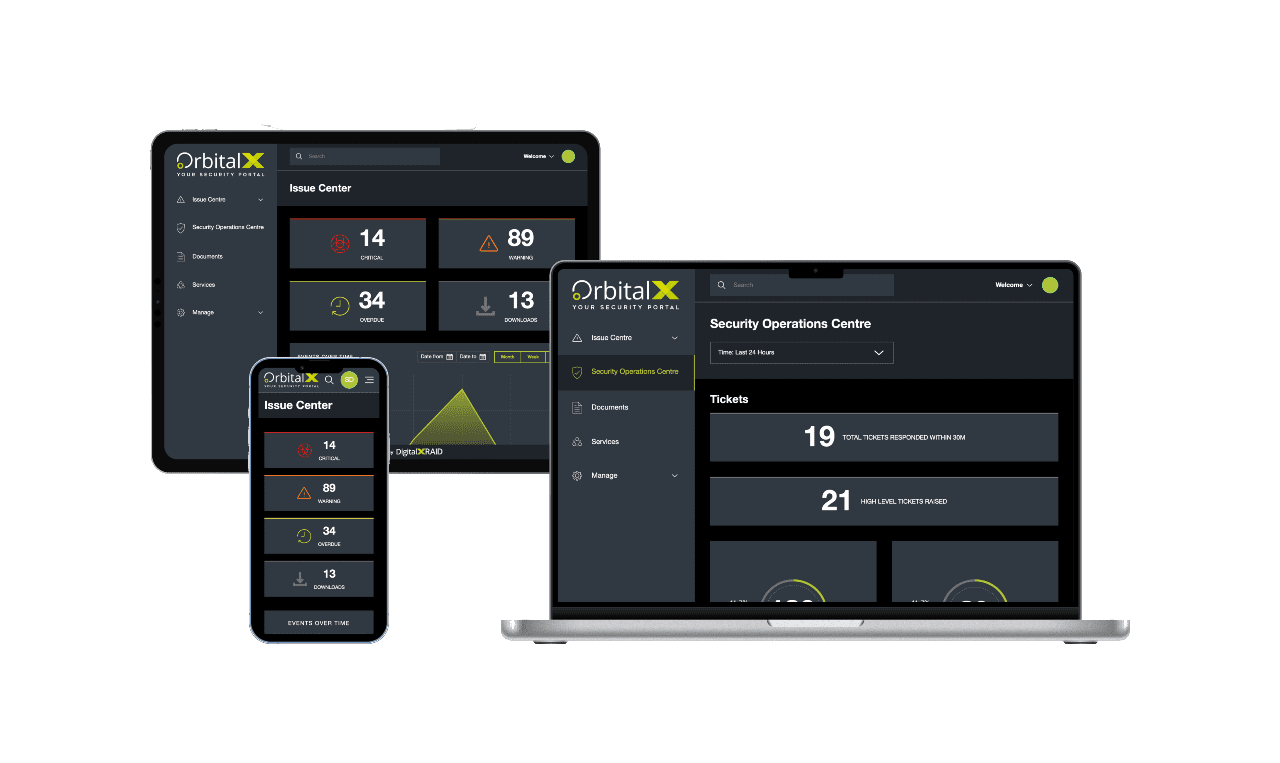
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
Protect your mobile applications
A security partner you can trust
Make sure you’re truly protected by putting your networks, systems and applications to the test. As with all cyber security, external penetration testing forms part of a robust security posture. We’ll work with you to identify and remedy weaknesses in your security before a malicious party exploits them.
Frequently Asked Questions
Most businesses should test their mobile apps annually, or after major code changes, infrastructure updates, or feature releases. High-risk apps (e.g. those handling payments, healthcare data, or corporate access) may need more frequent testing aligned to compliance cycles.
Mobile app testing focuses on platform-specific risks like local storage, device permissions, OS interactions, and communication with mobile APIs. Web app testing primarily targets browser-based behaviours. While both aim to find vulnerabilities, mobile testing requires a different methodology and toolset.
No. Our mobile pen tests are conducted in controlled environments using cloned apps or staging builds. Testing is designed to be non-intrusive and won’t affect live users, production systems, or app store listings.
Yes. Standards like PCI DSS, ISO 27001, and Cyber Essentials Plus often require regular pen testing of mobile apps if they process sensitive data. Our CREST-certified testing helps you meet those obligations and satisfy audit requirements.
Absolutely. We perform platform-specific testing for both Android and iOS environments, including grey-box and white-box scenarios. Our team understands the unique risks and behaviours of each OS.
Typically, we’ll need access to the APK/IPA files, test credentials (if available), details of backend endpoints, and a high-level architecture overview. Our team will guide you through a short scoping phase to ensure everything’s ready before testing begins.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Our other Pen Testing Services
Protect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.