DigitalXRAID will uncover the flaws in your web apps before an attacker can, with expert-led web app penetration testing that finds what scanners miss
Approximately 30,000 websites are infected with malware every day, with more than 60% of all internet-based attacks launched against web applications.
User facing systems, such as a web application, are the first place a hacker will try to access your data. With our state-of-the-art web application penetration testing, we can provide the protection you need to safeguard your sensitive data, defending you against every conceivable online threat and beating the hackers at their own game.
A web application penetration testing service will identify any risks or vulnerabilities and allow you to take action to protect your business before a vulnerability becomes a breach.
By simulating real-world hacking techniques, our team of cyber security experts will use industry leading penetration testing techniques to systematically target your company’s web applications, identifying any security flaws that a remote hacker might seek to exploit.
We’ll identify any weaknesses within your application(s) and recommend important fixes to keep you and your customers data safe from cyberattacks. With our cutting-edge procedures and techniques, we’ll assess the functionality of your website, pinpoint any failings in your systems. We’ll help you eliminate any potential threats to your business.
Why Choose DigitalXRAID for Web Application Pen Testing?

DigitalXRAID has achieved CREST OWASP Verification Standard (OVS) accreditation for Web Application Pen Testing, demonstrating our commitment to delivering industry-leading security testing.
CREST OVS is an internationally recognised gold standard, ensuring our application pen testing services meet the highest quality and consistency benchmarks. The rigorous accreditation process assessed our methodologies, highly skilled security testers, and company certifications, providing customers with assurance that our services align with OWASP’s ASVS and MASVS standards.
Customer benefits include:
- Clear and standardised security testing reports
- Potential reductions in cyber insurance premiums by using apps tested by a CREST OVS-accredited provider
- Guidance on best security practices for app development, aligned with OWASP ASVS and MASVS standards
- Assurance of high-quality, independently verified penetration testing
- Access to expert security testers accredited under CREST’s internationally recognised standards
Our team combines real-world attack insight with CREST, CHECK and NCSC accredited expertise to help you stay secure, compliant, and confident.
CREST, CHECK and NCSC Certified Web App Specialists
Every test is carried out by experienced, certified professionals following industry leading methodologies such as OWASP and CREST guidance.
Custom Testing for Complex Apps
From single sign-on to APIs and third-party integrations, we tailor every test to your tech stack.
Real-World Exploits, Not Just Scans
We go beyond automation, manually simulating how attackers target your app in the wild with custom exploits.
Clear, Prioritised Remediation Guidance
We don’t just list flaws, we show you which ones matter most, and how to fix them.
Support for PCI DSS, ISO 27001 & More
Meet regulatory expectations and information security framework mandates, including PCI DSS and ISO 27001 certification, with audit-ready reports and expert-led compliance advice.
Trusted by Regulated & High-Risk Sectors
Our web app tests help organisations across all sectors, including finance, healthcare, SaaS, and the public sector, to stay secure

20%
of web application tests identify critical vulnerabilities
33%
of users typically engage with internal phishing attempts
180K
machines were hijacked by ransomware in just 12 months
How Our Web App Pen Testing Works
What’s Included in Our Web Application Penetration Testing Services

We cover everything needed to expose and eliminate critical web app vulnerabilities:
- Manual Testing for OWASP Top 10 and Beyond: Identify injection flaws, authentication weaknesses, misconfigurations, and business logic errors.
- Testing of Authentication, Authorisation & Session Handling: Validate the strength of login flows, role-based access, and token management.
- API & Third-Party Integration Assessment: Secure your app’s dependencies, exposed endpoints, and data flows.
- Detailed Reporting for Technical & Executive Audiences: Includes risk ratings, replication steps, and tailored remediation advice.
- Retesting to Validate Fixes: Optional follow-up assessment to confirm vulnerabilities have been resolved
Choosing the Right Web App Pen Test Approach
No two applications are the same, and neither are their risks. Here’s how to find the right fit for your organisation.
Need to meet compliance fast?
Choose a scoped Web App Pen Test aligned to PCI DSS, ISO 27001, or your auditor’s requirements.
Using APIs or Single Sign-On?
Opt for custom test coverage that includes authentication flows, API endpoints, and third-party integrations.
Running a SaaS or cloud-native app?
We adapt testing to your deployment model from containerised platforms to serverless functions.


Launching a new app or update?
Pre-release testing helps you avoid security gaps before they go live.
Already using automated scanners?
Our manual testing uncovers logic flaws and chained exploits that automation often misses.
Need executive-ready proof of security?
You’ll receive board-friendly summaries, business and technical risk scores, and clear reporting to demonstrate control and resilience.
Book a Consultation
What is web application penetration testing?
Web app penetration testing is the process of investigating an organisation’s apps for a thorough assessment of security vulnerabilities.
Web application penetration testing services look at applications, including the gated content, to identify any vulnerabilities that could impact your business.
Once the exploitable security vulnerabilities that could cause a breach are identified, we support organisations to secure them, preventing future cyberattacks.
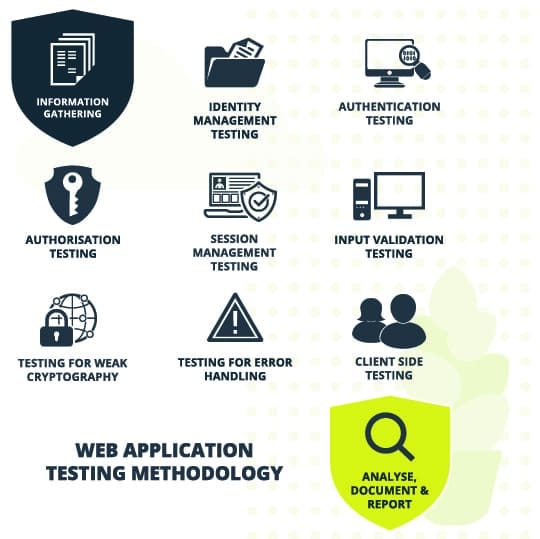
Our web application penetration testing methodology is closely aligned with the OWASP (Open Web Application Security Project®) Top 10.
We have never conducted a security assessment that didn’t detect at least one vulnerability. Read more about our web application penetration testing examples.
We have never conducted a web application penetration test that didn’t detect at least one vulnerability..
Web application penetration testing services will look for a range of potential vulnerabilities
What is involved in web application penetration testing?
Our web application pen test service covers the following
- A01:2021-Broken Access Control
- A02:2021-Cryptographic Failures
- A03:2021-Injection
- A04:2021-Insecure Design
- A05:2021-Security Misconfiguration
- AA06:2021-Vulnerable and Outdated Components
- A07:2021-Identification and Authentication Failures
- A08:2021-Software and Data Integrity Failures
- A09:2021-Security Logging and Monitoring Failures
- A10:2021-Server-Side Request Forgery
Insecure setup or configuration of networks
Through web application penetration tests, we will attempt to breach your system by looking for weak passwords, open ports, unpatched applications and incorrectly set user privileges.
Incorrect encryption and authentication
Can your WiFi and internet communications be intercepted and decrypted? Article 32 of GDPR includes encryption as an example of an appropriate technical measure to secure data. Are you encrypting data to a sufficient standard?
Code and command injection
Throughout the web application penetration test, we check that your web forms are built to protect against SQL injection attacks, and find how they behave when someone tries to interfere with them.
Session management
Cookies and sessions tokens are used to make web applications more user friendly, but they can be exploited for malicious purposes, making you vulnerable to attack.
Make an enquiry
Penetration of an application can cost a business over £2M.
Can your business sustain such a significant cost?
Your customers’ stolen data may be sold on the dark web
Is your brand strong enough to withstand such a blow?
69% of customers said they would never return
Customers are less likely to buy from a breached organisation

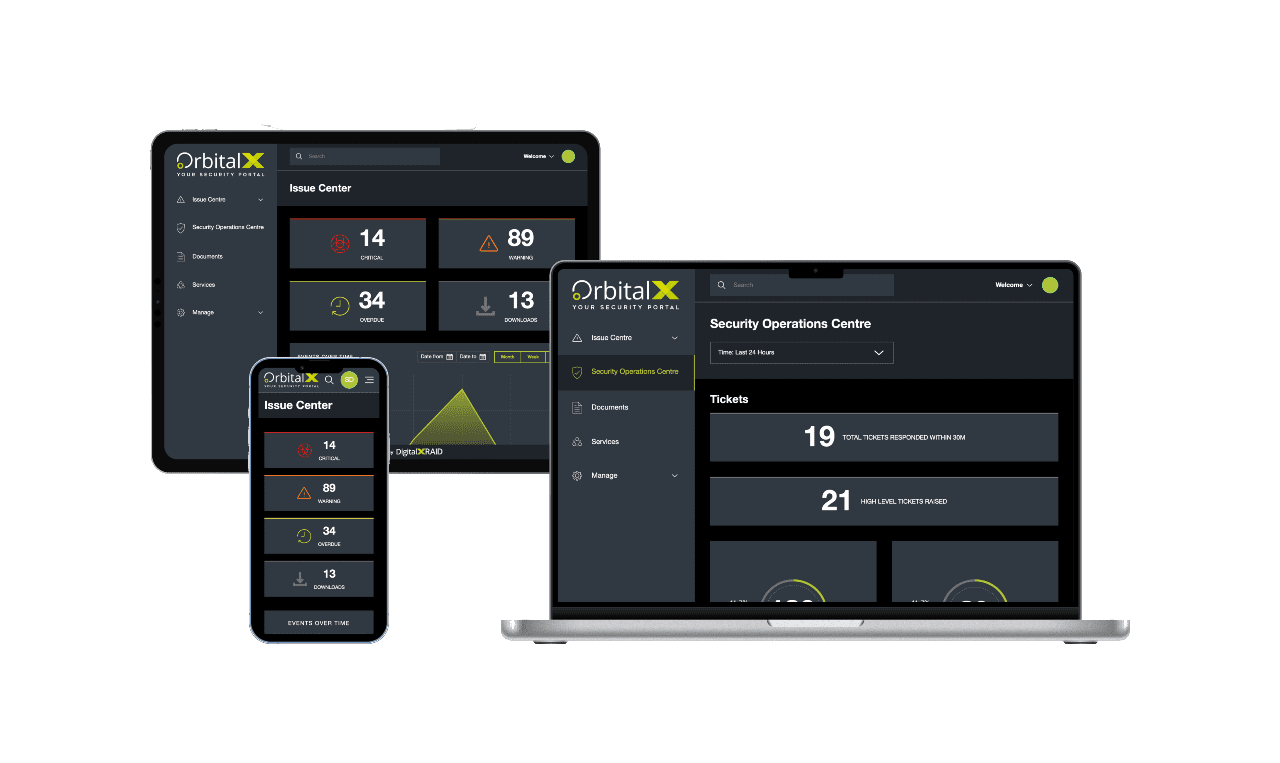
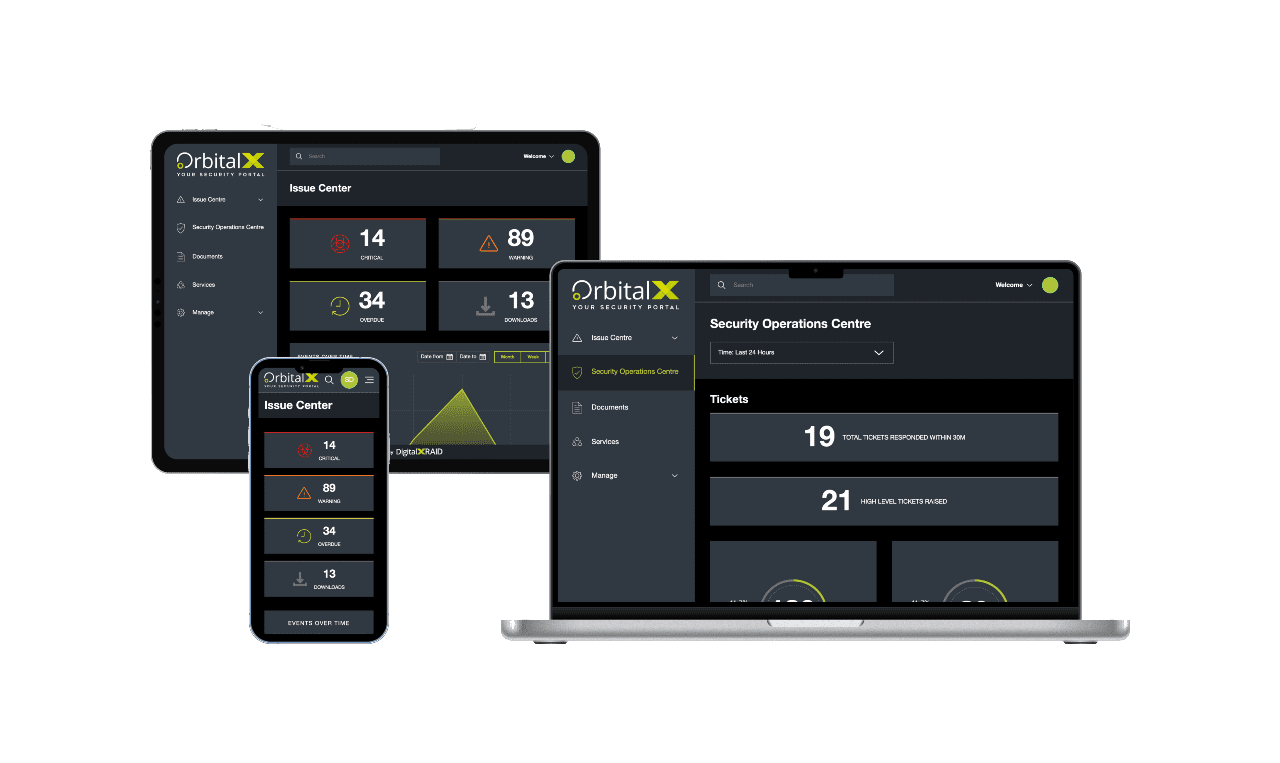
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
Benefits of Web App Pen Testing
Why Web App Pen Testing Matters
Web applications are a prime target, and one overlooked flaw could expose your business. Learn more about the benefits that expert pen testing delivers:

Identify and fix the weaknesses attackers exploit before they become incidents.
Demonstrate trust and transparency with third-party testing and clear reports.
Stay aligned with regulations, including PCI DSS, and more, without scrambling under deadlines
Secure authentication flows, user roles, APIs, and business logic against real-world attack methods.
Actionable insights help developers fix issues fast, without security slowing releases and align with new regulation guidance around secure by design coding.
Testing isn’t just a checkbox; it’s a proactive way to build resilience and reduce long-term risk.
Protect your business with web application penetration testing
A security partner you can trust
Make sure you’re truly protected by putting your networks, systems and web applications to the test. As with all cyber security, web application penetration testing forms part of a robust security posture. We’ll work with you to identify and remedy weaknesses in your security before a malicious party exploits them.
“DigitalXRAID understood our business and specific needs from the start, and provided a professional service, answering questions if they arose and delivering consistent communication throughout the process. The Web Application Penetration Testing service has provided 3Fun with complete peace of mind that our application is secure and that our users’ data is protected, which is our upmost concern and our pledge to customers.”
– 3Fun
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
FAQs: Web Application Penetration Testing
It’s a simulated attack on your web apps using real-world tactics to uncover security flaws before attackers do. This includes issues like broken authentication, injection flaws, and insecure configurations.
No. Automated tools only identify known CVEs and miss logic flaws and complex vulnerabilities. Manual pen testing by certified experts offers deeper insights into real-world attack paths.
It depends on the size and complexity of your application, but most tests take 3–10 days of testing with scoping and reporting on top of that.
Our tests are safe by design. We agree on boundaries up front and use controlled methods to avoid downtime or disruption.
Yes. A WAF helps reduce risk, but can’t guarantee your app is secure. Pen testing uncovers weaknesses in business logic, authentication, and backend integrations that a WAF can’t see.
Our Penetration Testing Services
Cyber Security Experts
Our team comprises professionals selected for their industry expertise and outstanding work ethic, allowing us to provide you with market leading cyber security services.
Long term solutions
We deliver long term solutions to ensure your company is protected. A longstanding partnership with the right cyber security provider is invaluable.
Personal touch
Your business is unique. We will listen and work closely with you to understand your challenges, identify the vulnerabilities that are particular to your business, and put in place tailored countermeasures.
Industry leaders
Our expertise, experience and knowledge base puts us in the ideal position to deliver industry leading protection against existing and emerging cyber threats.
Web Application Penetration Testing Services
No single penetration test or report is ever going to be enough to secure an organisation against the complex and evolving cyber threat landscape. As your Managed Security Service Provider (MSSP) we will construct a bespoke and proactive plan to take care of your entire cyber security requirements now and into the future.
- Your trusted partners: We’ll deliver guidance, support and recommendations based on real evidence and genuine assessment of your business needs.
- We’ll continually test your web applications, identify exploitable factors, and upgrade your facilities to meet your evolving needs.
- We’ll make sure your cyber protection remains robust, comprehensive and cutting-edge.
Find out more about our managed service:
Managed Penetration Testing ServicesProtect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.