Internal Penetration Testing Matters More Than Ever
Most businesses focus on securing their perimeter, but what happens when the
threat is already inside?
Whether it’s a malicious insider, a compromised device, or a poorly segmented network, internal risks are often the most overlooked and most damaging.
DigitalXRAID’s internal penetration testing services simulate insider threats and compromised devices to uncover critical vulnerabilities in your internal infrastructure, before attackers do.
Just some of the customers that trust DigitalXRAID to protect their business from cyber threats
Why Choose DigitalXRAID’s Internal Penetration Testing Services?

Simulate Real Insider Threats
We assess your internal infrastructure from the viewpoint of a rogue employee or compromised endpoint, identifying lateral movement, privilege escalation, and access gaps.
CREST and CHECK Certified Internal Pen Testing Team
All testing is conducted by certified experts under strict methodologies, ensuring compliance and credibility with recognised industry standards.
Full Visibility Into Internal Weaknesses
Our tests reveal unseen risks across workstations, servers, databases, and privileged user paths, not just surface level vulnerabilities.
No Disruption to Your Operations
We conduct internal assessments discreetly with minimal impact, no downtime, no unnecessary alerts, and complete confidentiality.
Post-Test Report with Risk Prioritisation
We don’t just provide a list of issues. We categorise vulnerabilities by severity, business risk, and exploitability, so you know what to fix first.
Expert Guidance to Remediate Gaps
Get more than findings, receive strategic remediation advice from our security consultants to improve your internal defences long term.

75%
organisations report insider attacks are more frequent
100%
assessments found sensitive corporate data transfers
95%
of cyber security breaches are caused by human error
How Our Internal Penetration Testing Works
Our internal penetration testing follows a structured, real-world approach to uncover hidden risks within your internal network.
Every stage of the process is designed to simulate a malicious insider or compromised device, exposing vulnerabilities, privilege escalation paths, and lateral movement opportunities that could be exploited in a real attack.
We start with both passive and active reconnaissance to map your internal environment. This includes identifying devices, services, and potential access points without triggering alerts.
Passive techniques help us understand what can be seen by an attacker already inside the network, while active scanning builds a clearer picture of live hosts, open ports, and exposed internal services. This foundation ensures that subsequent testing is precise and risk-focused.
Once we’ve identified the internal assets, we move to fingerprinting and enumeration.
Here, our team determines system types, operating systems, service banners, and access pathways. We also enumerate user accounts, internal shares, and directory structures to highlight where weaknesses may lie.
This stage mirrors how an attacker would profile your internal infrastructure to find the path of least resistance
With targets and configurations confirmed, we analyse each system for vulnerabilities.
This includes identifying known exploits, insecure configurations, and outdated software that could be leveraged for unauthorised access.
We assess weak or default credentials and look for excessive privileges that could be misused. Where standard tooling isn’t enough, we use custom scripts to uncover risks that off-the-shelf scanners miss.
If vulnerabilities are found, we carefully attempt exploitation under strict, pre-agreed rules of engagement.
Our ethical hackers simulate how a threat actor might exploit these weaknesses to gain internal access. We then test whether access can be escalated, for example, from a standard user to an administrator, exposing the true risk of the vulnerability if left unaddressed.
Next, we evaluate how an attacker might move laterally through your environment.
This involves testing network segmentation, internal controls, and privilege boundaries to see how easily a breach in one area could lead to access elsewhere.
We also simulate persistence techniques, such as creating hidden accounts or services, to assess how well your defences can detect and prevent ongoing compromise.
Finally, we remove all traces of testing to leave your environment in its original
state.
You’ll receive a comprehensive, prioritised report detailing each finding, the associated business risk, and practical steps to remediate them. Every result is mapped to severity and exploitability, giving you clarity on what to fix first.
Our consultants also provide expert guidance to help you resolve issues and strengthen internal defences.

What’s Included in Our Internal Pen Testing Services?
Our internal penetration tests are designed to uncover risks within your organisation’s internal network, before attackers do.
Every engagement includes:
- Insider threat simulation – Mimics attacks from within your network.
- Privilege escalation testing – Identifies weak spots in access control.
- Lateral movement analysis – Reveals how threats spread internally.
- Credential & config checks – Find exposed passwords and misconfigurations.
- Device security review – Assesses risks across laptops, servers, and more.
- Detailed report & remediation – Clear risk ratings with actionable fixes.
All testing is performed by CREST-certified ethical hackers using industry-leading methodologies to support your compliance, reduce internal risk, and strengthen your security posture.
What Are the Benefits of Internal Penetration Testing?
Internal pen testing helps identify and close gaps that external testing can’t reach, protecting your business from inside-out threats.
Internal pen testing helps identify and close gaps that external testing can’t reach, protecting your business from inside-out threats.
Key benefits include:
- Uncover hidden internal risks – Find overlooked vulnerabilities behind your firewall.
- Protect against insider threats – Detect malicious or accidental risks from staff or partners.
- Support compliance readiness – Meet ISO 27001, PCI-DSS, and other audit requirements.
- Test real-world attack paths – Understand how an attacker could move laterally within your network.
- Strengthen internal defences – Improve segmentation, privilege access, and endpoint controls.
- Inform IT & security decisions – Get actionable insights to guide remediation and investment.
Internal pen testing is essential for mid–to-large enterprises managing hybrid infrastructure, regulated data, or complex internal environments.

Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Is Internal Pen Testing Right for Your Business?
Mid-to-large enterprises face growing internal risks, from misconfigurations and privilege escalation to insider threats and hybrid infrastructure gaps. Internal pen testing helps identify and fix these risks before attackers exploit them.

Large or Distributed Internal Networks
The more devices, users, and systems you manage internally, the greater the risk of internal breach or privilege escalation.
Active Directory Exposure
Internal testing uncovers misconfigurations or flaws in AD setups that attackers could exploit.
Compliance Requirements
Frameworks like ISO 27001 and PCI DSS often require internal testing to prove security due diligence.
No Previous Internal Testing
If you’ve only tested external threats, your internal infrastructure could still be wide open.
Hybrid or Remote Working
Dispersed access increases attack surfaces. Internal testing helps validate segmentation and access controls.
Insider Threat Concerns
Simulate what happens if an internal account is compromised and test your ability to detect and contain it.
Critical Internal Applications
Non-public apps often go untested. An internal test ensures they’re not an easy target.
Infrastructure Changes or Mergers
Validate that nothing has been misconfigured or left exposed during internal changes or integrations.
Need for Third-Party Assurance
Get CREST-certified evidence of your internal security posture to share with stakeholders or regulators.


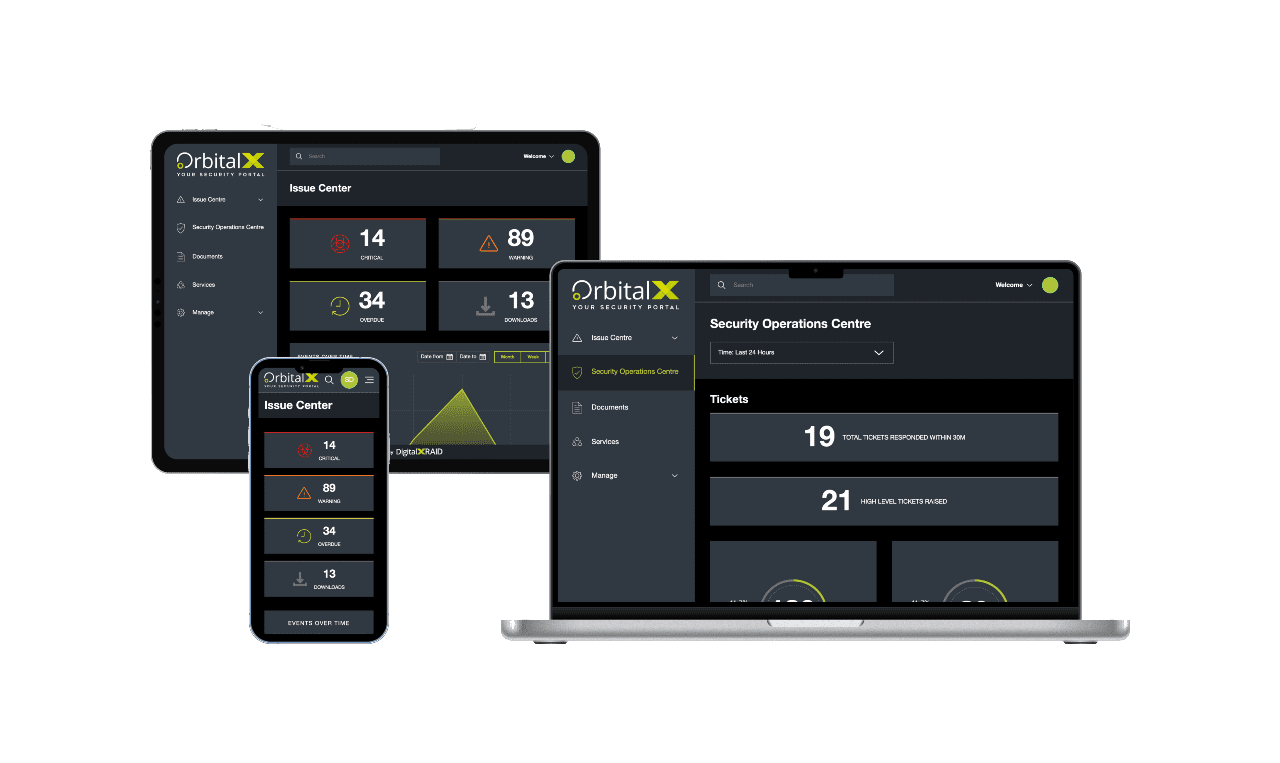
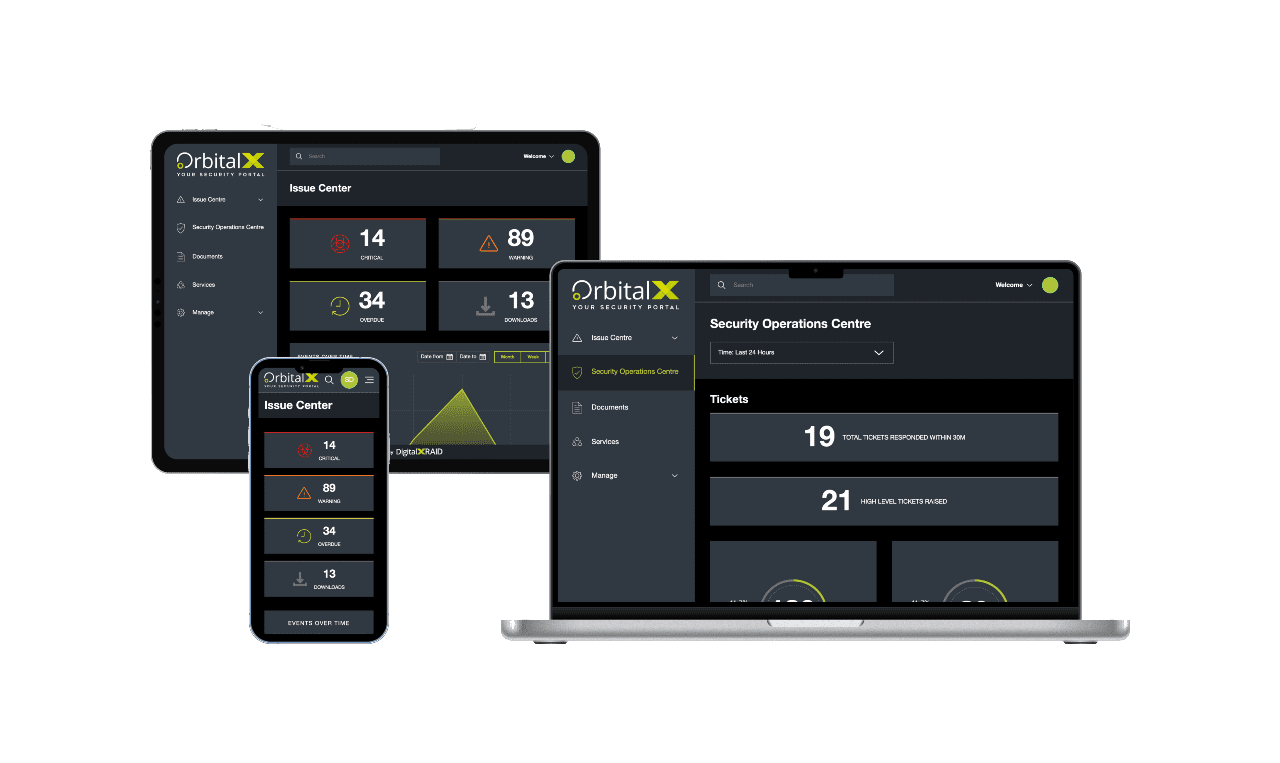
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
“Feedback on the pen test from internal teams here was very positive and communication was responsive. We now have a much deeper visibility on our current security posture. We’re very happy with the reporting, which gave a thorough explanation of the findings and gave us clear solutions for remediation.”
Brigid Macdonald, Head of IT, Breast Cancer Now
FAQs: Internal Penetration Testing
Internal penetration testing simulates an attacker operating inside your organisation’s network, such as a malicious insider or compromised device. It focuses on lateral movement, privilege escalation, and internal misconfigurations. External testing, by contrast, targets publicly accessible systems from outside the firewall (like websites, VPNs, or email servers).
Internal pen tests can reveal a range of overlooked risks, including weak or reused credentials, misconfigured devices, excessive user privileges, vulnerable legacy systems, and insecure internal services. These issues are often invisible to external scans but pose a serious risk if exploited.
At a minimum, internal pen testing should be carried out annually, or after significant infrastructure changes, such as office moves, mergers, or new device rollouts. Organisations in regulated industries or with high insider risk may benefit from more frequent testing (e.g., biannually).
Most internal pen tests take between 3–5 working days, depending on network size, number of endpoints, and the scope of engagement. We’ll work closely with your team to minimise operational disruption and provide timely results.
No, internal penetration testing is designed to be non-disruptive. Our team uses controlled techniques and agrees on test windows to avoid impact on business-critical systems. You’ll be fully briefed on all actions, with rollback options and safe testing parameters in place.
Internal penetration testing helps organisations meet security requirements under frameworks like ISO 27001, PCI-DSS, Cyber Essentials Plus, and NIST. It demonstrates proactive risk management and due diligence, especially around internal infrastructure, user access, and insider threats.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Our other Pen Testing Services
Protect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.