Get peace of mind that your systems and services are secure with external infrastructure penetration testing services.
DigitalXRAID’s external penetration testing services simulate real-world attacks on your public-facing infrastructure, helping you identify and fix vulnerabilities before attackers can exploit them.
Most cyberattacks begin with the same flaw: an unpatched service, a weak firewall, a misconfigured remote access point. External pen testing helps your business stay one step ahead by revealing these weaknesses before they’re exploited.
Just some of the customers that trust DigitalXRAID to protect their business from cyber threats
Why Choose DigitalXRAID’s External Penetration Testing?
DigitalXRAID’s external pen tests are led by CREST-certified experts who simulate real-world attacks to uncover vulnerabilities in your internet-facing infrastructure, before attackers do.
We replicate attacker behaviour using controlled techniques to find weaknesses in firewalls, servers, email gateways, VPNs, and more.
All testing is conducted by our CREST-certified penetration testers, ensuring recognised quality, rigour, and regulatory alignment.
Get a clear view of your internet-facing infrastructure, including vulnerable services, outdated software, and potential entry points.
Our tests are designed to be low impact, non-invasive, and stealthy, providing detailed results without affecting day-to-day operations.
Your report will include actionable risk ratings based on exploitability and business impact, so your team knows where to focus.
We go beyond the scan, providing technical advice, configuration support, and fix validation to close gaps quickly.
92%
of network perimeters are breached during external pen testing
16%
of external pen tests found evidence of a previous cyberattack
4 days
is all it takes on average for successful external network penetration
How Our External Penetration Testing Process Works
At DigitalXRAID, our external penetration tests follow a proven methodology that ensures clarity, rigour, and minimal disruption to your business. Here’s how the process works:

Scoping
Before testing begins, we define the scope of the engagement with you. This includes identifying which external assets (such as IP addresses, domains, or web applications) will be tested, setting access parameters, and ensuring all stakeholders understand the objectives.
Scoping also determines whether testing is black box (no prior knowledge), grey box (limited access), or white box (full access), depending on your needs.
Reconnaissance
Using both passive and active techniques, we gather publicly available information about your organisation and digital infrastructure.
This could include DNS records, open ports, service banners, certificate data, and more, mimicking what an external attacker would see before launching an attack.
Assess
Our CREST-certified testers perform in-depth assessments of your external perimeter to identify known vulnerabilities.
We use commercial-grade tools and manual techniques to identify weaknesses across exposed services, firewalls, APIs, and cloud platforms. This stage helps build a picture of your attack surface and potential weak points.
Probe
We attempt controlled exploitation of identified vulnerabilities to understand their impact.
This includes testing for unauthorised access, remote code execution, data exposure, or lateral movement opportunities. All probing is carefully managed to avoid disruption and follows agreed safety parameters.
Quality Assurance
Before delivering any findings, all results go through a quality assurance phase.
This involves verifying the accuracy of the vulnerabilities, checking for false positives, and validating the evidence gathered. You’ll only receive confirmed, actionable findings, never guesswork.
Retest
Once remediation steps are complete, we offer a retesting phase to verify that previously identified issues have been resolved.
Our team will retest the specific areas in scope to confirm vulnerabilities have been closed and ensure your external defences are now secure. This final step gives you full confidence in the effectiveness of your remediation efforts.

Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734

What’s Included in Our External Pen Testing Services
Our CREST-certified external penetration tests are tailored to your infrastructure and business needs. Each assessment includes:
- Targeted threat simulation – Mimics cybercriminal tactics on your public-facing systems
- External asset mapping – Identifies exposed services and applications
- Exploitation testing – Controlled attacks to verify real-world risk
- Firewall & config review – Assesses network segmentation and access control
- DNS & domain review – Identifies risks related to web presence and records
- Clear, actionable reporting – Prioritised risk ratings with remediation guidance
Every engagement is delivered by CREST-certified experts, with a detailed report and prioritised fixes to strengthen your external-facing defences and support ongoing compliance.
What Are the Benefits of External Penetration Testing?
External pen testing helps uncover vulnerabilities in your internet-facing systems before threat actors can exploit them. Key benefits include:
- Identify exploitable public-facing risks – Detect weak spots in websites, VPNs, email gateways, and cloud services.
- Prevent real-world cyberattacks – Simulate external threat scenarios to uncover how attackers could gain access.
- Demonstrate security to stakeholders – Provide clear evidence of due diligence to clients, insurers, and auditors.
- Support regulatory compliance – Meet PCI-DSS, ISO 27001, Cyber Essentials Plus, and other security requirements.
- Strengthen perimeter defences – Gain clarity on patching gaps, misconfigurations, and access control flaws.
- Prioritise remediation efforts – Receive expert-led guidance based on severity, impact, and business context.
External penetration testing is essential for any business with customer-facing infrastructure, online assets, or compliance requirements, especially as threats continue to evolve.

Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Is External Pen Testing Right for Your Business?
Mid-to-large enterprises face constant threats from exposed public-facing systems, from cloud applications to misconfigured firewalls and third-party access points. External penetration testing helps you find and fix these vulnerabilities before attackers exploit them.

Public-Facing Infrastructure
The more digital services you expose online, like websites, VPNs, or email, the more doors you leave open to attackers.
Compliance Requirements
External testing is often required under frameworks like ISO 27001, PCI DSS, and Cyber Essentials Plus to demonstrate proactive security.
Recent Infrastructure Changes
Migrations, new portals, or cloud deployments may introduce unknown exposures. Testing helps verify that new systems are secure.
Third-Party Access or APIs
Partner systems, vendor integrations, and exposed APIs increase your external attack surface and should be assessed regularly.
Cyber Insurance or Client Demands
Clients, insurers, and auditors increasingly expect proof of penetration testing as part of cyber risk due diligence.
High-Value Brand or Data
If you store sensitive data, serve regulated sectors, or are a recognisable brand, attackers are more likely to target you.

“Feedback on the pen test from internal teams here was very positive and communication was responsive. We now have a much deeper visibility on our current security posture. We’re very happy with the reporting, which gave a thorough explanation of the findings and gave us clear solutions for remediation.”
Brigid Macdonald, Head of IT, Breast Cancer Now

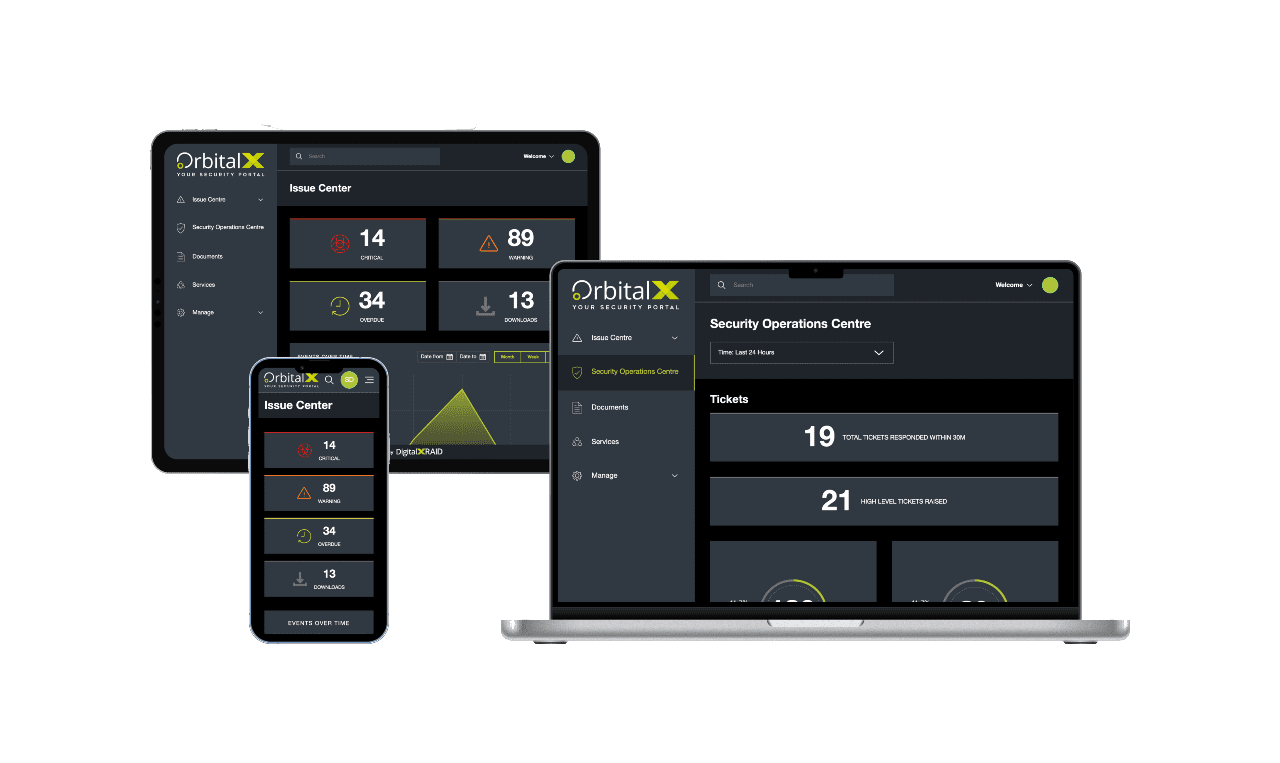
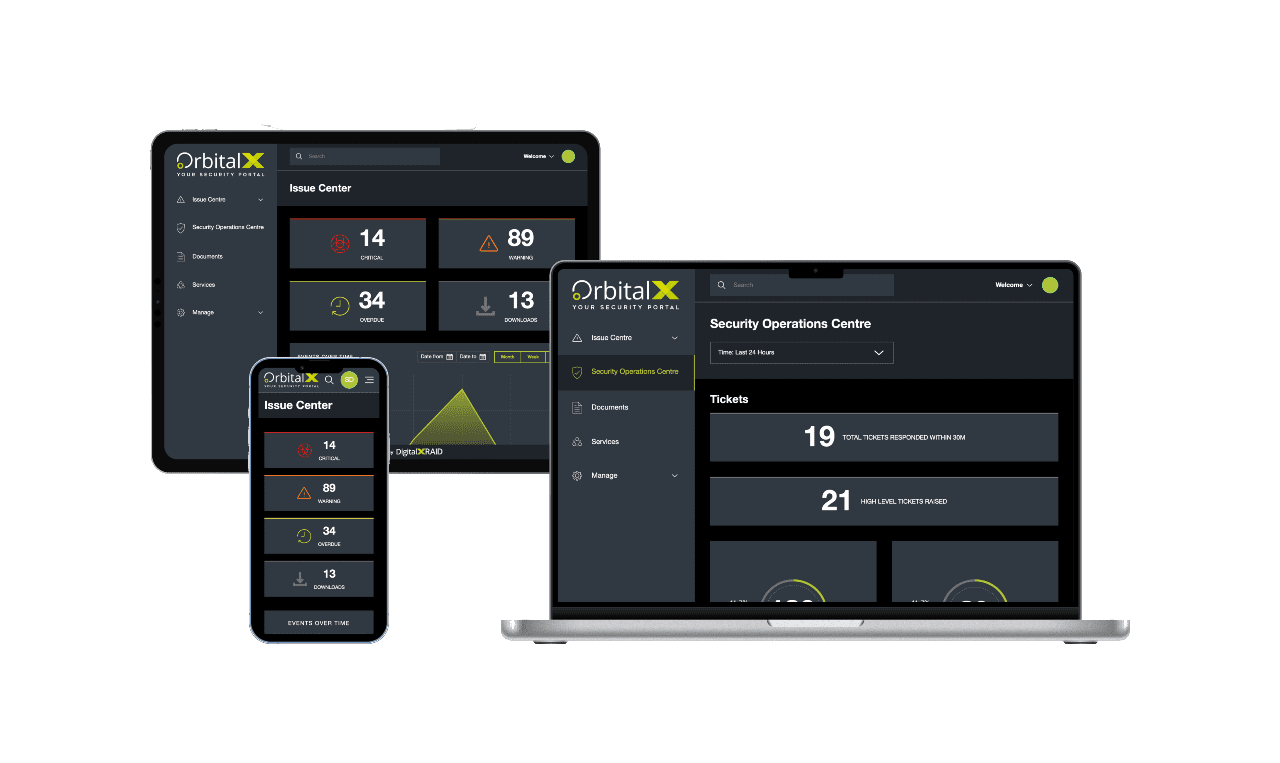
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
Protect your business with external penetration testing
A security partner you can trust
Make sure you’re truly protected. As with all cybersecurity, external penetration testing forms part of a robust security posture. We’ll work with you to identify and remedy weaknesses in your security before a malicious party exploits them and you fall victim to a cyberattack.
Frequently Asked Questions
External penetration testing targets internet-facing systems like web servers, VPNs, and email gateways, simulating how an attacker might breach your organisation from the outside. Internal pen testing simulates threats from within your network, such as a compromised employee account or device.
Most organisations conduct external penetration testing at least once per year, or after significant changes to their infrastructure. However, high-risk or regulated businesses may need more frequent testing to stay compliant and secure.
Yes. Both ISO 27001 and PCI DSS frameworks recommend or mandate regular external testing as part of demonstrating security due diligence and effective risk management.
Absolutely. Our CREST-certified testers follow strict guidelines to ensure that testing is non-disruptive and safe for production environments. Any potentially intrusive actions are discussed and scheduled in advance.
Your report will include a clear summary of findings, risk ratings, detailed descriptions of each vulnerability, how it was discovered, business impact, and remediation guidance. We also provide an executive summary for non-technical stakeholders.
Vulnerability scanning is automated and identifies known issues. Penetration testing goes deeper, using manual techniques to actively exploit vulnerabilities, chain exploits together, and uncover real-world attack paths a scanner might miss.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Our other Pen Testing Services
Protect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.