Pen Testing vs Vulnerability Scanning: The Key Differences & When to Use Each
Penetration testing vs vulnerability scanning are two of the most frequently confused terms in cyber security. They’re both used to assess your security posture, both produce reports on weaknesses, and both are often referenced in the same compliance conversations.
But they’re not interchangeable, and using one when you need the other can leave your networks, systems and applications at risk.
The confusion has a commercial dimension too. Some providers sell vulnerability scans under the label of penetration tests, often at suspiciously low price points, with automated reports delivered fast. If you’re buying what you believe is a penetration test and receiving a vulnerability scan, you’re not getting the assurance your business needs.
In this guide, we’ll explain what each method does, the key differences between a pen test vs vulnerability scan, what compliance frameworks require, how to evaluate cost, and the questions you should ask any provider before you sign off on a security assessment. By the end, you’ll know exactly which approach your organisation needs and why.
Key Takeaways
- A vulnerability scan is an automated process that identifies known weaknesses across your systems. A penetration test is a manual, expert-led assessment that actively attempts to exploit those weaknesses to demonstrate real-world business risk.
- Vulnerability scanning provides breadth: fast, scalable, and suitable for regular monitoring. Penetration testing provides depth: it uncovers complex attack paths, chained vulnerabilities, and business logic flaws that no scanner can find.
- You can’t replace a penetration test with a vulnerability scan. Many organisations need both, used together, as part of a layered security strategy.
- CREST and CHECK (NCSC) are the accreditations that matter for penetration testing in the UK. If a provider can’t evidence these, what they’re offering is unlikely to be a true penetration test.
- Compliance frameworks including PCI DSS, DORA, NIS2, and ISO 27001 each have specific requirements for penetration testing and vulnerability scanning. Understanding which applies to your organisation determines the minimum standard you must meet.
- A suspiciously cheap “pen test” delivered within hours is almost certainly a vulnerability scan. Knowing how to spot the difference protects your budget and your security posture.

Understanding the Two Methods: Penetration Testing vs Vulnerability Scanning
Vulnerability scanning and penetration testing both aim to identify weaknesses in your security, but their approach, depth, and output are fundamentally different. Understanding each on its own terms is the foundation for making the right choice for your organisation.
What is a Vulnerability Scan?
A vulnerability scan is an automated process. Scanning tools check your systems, networks, and applications against databases of known vulnerabilities, collectively referred to as Common Vulnerabilities and Exposures (CVEs).
The scanner matches what it finds in your environment against known security flaws: outdated software, unpatched systems, misconfigured services, weak password policies, and similar issues.
The output is a report listing what the scanner found, typically categorised by severity (Critical, High, Medium, Low), with references to the CVE identifier and general guidance on remediation. Scans are fast, scalable, and can cover large environments quickly.
A scan of an average-sized network can be completed in hours, and results can be acted on immediately through patch management.
What a vulnerability scan doesn’t do is attempt to exploit any of the weaknesses it finds. It identifies that the door lock is loose. But it doesn’t try to break in.
When looking at penetration testing vs vulnerability scanning, this is the critical distinction. A scanner can’t tell you whether a vulnerability is actually exploitable in your specific environment, how it could be combined with other weaknesses to create a serious breach, or what the real world business impact would be if it were attacked.
What is a Penetration Test?
A penetration test is a manual, expert-led security assessment. A qualified tester, working within a defined scope and rules of engagement, actively attempts to exploit vulnerabilities in your systems, applications, and network infrastructure.
The goal is to simulate what a real attacker would do: identify weaknesses, chain them together, escalate access, and demonstrate how far into your environment a threat actor could get and what they could do once there.
Penetration testing goes significantly beyond what any automated tool can achieve. Experienced testers identify business logic flaws that scanners can’t detect, chain low-severity vulnerabilities together to create high-impact attack paths, and use techniques including social engineering, custom exploit development, and manual reconnaissance to uncover threats that have no CVE identifier.
The output is a detailed report that includes proof of exploitation, a narrative of how the attack progressed, the business impact of each finding, and specific, prioritised remediation guidance.
In the UK, the quality standard for penetration testing is CREST accreditation, with CHECK (delivered under NCSC assurance) required for UK government and public sector engagements. DigitalXRAID holds both, and our penetration testing services are built on industry-leading methodologies including OSINT, OWASP, and PTES, tailored to your specific environment and risk profile.
What is a Vulnerability Assessment? Clearing Up the Terminology
When evaluating vulnerability assessment vs penetration testing, one of the most common sources of confusion is terminology itself. You’ll encounter the term “vulnerability assessment” frequently, sometimes as a distinct service, sometimes as a synonym for vulnerability scanning, and occasionally as a way of dressing up an automated scan as something more comprehensive than it is.
In most practical contexts, a vulnerability assessment and a vulnerability scan describe the same thing: an automated process that identifies known weaknesses without attempting to exploit them.
Some providers use “vulnerability assessment” to imply a more thorough process. If a provider uses this term, ask specifically whether the assessment includes manual testing by a qualified tester, whether it produces proof of exploitation, and whether the provider holds CREST or CHECK accreditation for the work. If the answers are no, you’re being provided a vulnerability scan. Understanding this distinction matters just as much when comparing a penetration test vs vulnerability assessment as it does when comparing pen testing to scanning, the label doesn’t always match the service.

Penetration Testing vs Vulnerability Scanning: Key Differences
The two methods serve different purposes and sit at different points in your security strategy. Here’s how they compare across the dimensions that matter most when deciding which you need.
Automation vs Human Expertise
Vulnerability scanning is automated. Once configured and run, the tool does the work without human involvement in the assessment itself. This makes scans fast, repeatable, and scalable: you can scan an entire estate in hours and schedule scans to run on a regular cadence with minimal resource.
Penetration testing depends on human expertise. A CREST certified tester applies technical skill, creativity, and attacker mindset to your environment.
They can adapt their approach based on what they find, chain vulnerabilities in ways no algorithm would predict, and bring the kind of contextual judgement that distinguishes a genuine security assessment from an automated checklist.
This is why accreditation matters. CREST and CHECK certification tells you the tester has been independently assessed against a rigorous professional standard.
Breadth vs Depth
Vulnerability scanning prioritises breadth. It covers a wide attack surface quickly, giving you a comprehensive picture of known weaknesses across your entire environment. This makes it ideal for continuous monitoring, where the goal is to ensure no known vulnerability goes unpatched across a large and changing estate.
Penetration testing takes steps that prioritise depth. It focuses on specific targets, systems, or applications and examines them in detail, exploring how weaknesses interact, how access can be escalated, and what an attacker could ultimately achieve. A penetration test on a single web application may take days and produce findings that a scanner running across the same application would miss entirely.
Output and Actionability
A vulnerability scan produces a list of vulnerabilities found, CVE references, severity scores, and general remediation guidance. This is genuinely useful for patch management and baseline security maintenance, but it doesn’t tell you whether any of the vulnerabilities are exploitable in your specific environment, or what the consequence of exploitation would be.
A penetration test produces evidence. The report includes proof of exploitation (screenshots, data samples, access logs), a narrative of how the tester moved through your environment, and a clear articulation of business risk for each finding.
This is the kind of output you can take to a board, present to an insurer, or use to justify a remediation budget. It’s also what compliance auditors expect when they ask for evidence of penetration testing.
Frequency and Cost
Vulnerability scanning is designed to run frequently. Monthly scans are standard practice for most organisations. Best practice advice says that critical systems should be scanned quarterly at minimum, and after any significant change to your infrastructure.
The cost is relatively low, scans can be conducted for hundreds rather than thousands of pounds per cycle, and managed scanning services make it easy to maintain a continuous, consistent programme.
Penetration testing is conducted less frequently but at greater depth. Annual testing is the recognised minimum for most organisations, with additional tests triggered by significant system changes, major infrastructure migrations, pre-launch of new products or services, post-incident reviews, and compliance requirements.
The cost reflects the expertise involved: a typical infrastructure penetration test for a mid-sized UK organisation might range from £2,000 to £8,000 depending on scope, with web application testing, red team exercises, and complex multi-environment assessments carrying higher fees.
Compliance Requirements
Different regulatory frameworks have specific requirements for penetration testing vs vulnerability scanning, and they don’t treat the two as equivalent. Our detailed guide to pen testing for compliance covers each framework in full, but here’s a summary of what the most commonly applicable standards require:
PCI DSS requires both quarterly external vulnerability scans (conducted by an Approved Scanning Vendor) plus annual penetration testing of internal and external systems. The two are explicitly separate requirements. A vulnerability scan does not satisfy the pen testing obligation under PCI DSS v4.0.1.
ISO 27001 certification doesn’t mandate penetration testing by name, but Annex A controls covering technical vulnerability management and information systems audit (A.8.8 and A.8.34 in the 2022 standard) are most effectively evidenced through regular scanning combined with periodic penetration testing. Many ISO 27001 certification bodies will expect to see evidence of testing as part of the audit.
DORA requires financial sector entities to conduct threat-led penetration testing (TLPT) for their critical functions. This is a specifically defined, advanced form of penetration testing, and a vulnerability scan is not a substitute.
NIS2 takes an outcome-based approach. Operators of essential services must test and audit their security measures and manage vulnerabilities proactively. Penetration testing is the most effective way to evidence this.

What Does a Pen Test Find That a Vulnerability Scan Doesn’t?
This is one of the most important questions to understand, and the answer is what makes the difference between knowing you have a loose door lock and knowing whether a skilled burglar could get through it.
The clearest benefit that pen tests bring is vulnerability chaining.
A penetration tester doesn’t evaluate vulnerabilities in isolation. They look for combinations: a low-severity misconfiguration on a perimeter firewall, combined with an unpatched internal service that’s been deprioritised because it has no direct internet exposure, combined with weak network segmentation. None of these individually might appear critical in a vulnerability scan report but together, they create a complete attack path from outside your network to your most sensitive data.
Consider that an IT manager might know about an open vulnerability on a backend database system and has deprioritised patching it because the system sits on a separate network segment with no direct internet access. A vulnerability scan flags the database vulnerability but rates the risk as manageable given the isolation.
During a penetration test, the ethical hacker identifies a separate vulnerability on the perimeter firewall, unknown to the IT team. By exploiting the firewall weakness, they gain access to the internal network, discover the misconfigured network segmentation, bypass it, and access the backend database directly, without passing through any perimeter security.
They extract sensitive data from the database and document exactly how they did it.
That scenario, from a vulnerability scan perspective, shows a medium-severity finding on a database. From a penetration test perspective, it shows a complete breach of sensitive data with evidence, an articulated business impact, and the board-level justification needed to prioritise and fund remediation.
Penetration testing also identifies business logic flaws, which scanners can’t detect at all. These are vulnerabilities in how your application or system is designed to work, not in the software it runs on. An attacker who understands your business processes might find that they can manipulate a purchase workflow, escalate their account privileges, or access data belonging to another user, none of which will appear in any CVE database.
How to Tell if You’re Being Sold a Vulnerability Scan Instead of a Pen Test
This is one of the most practically useful things any security buyer can know. The market for penetration testing has a well-documented problem: some providers sell vulnerability scans labelled as penetration tests, often at low price points.
The buyer receives an automated report, believes they’ve conducted a penetration test, and makes security decisions based on an assessment that hasn’t actually fully tested their defences.
Here are the signals that what you’re being offered is a vulnerability scan, regardless of what it’s called:
- The price is very low. A genuine penetration test requires days of skilled, certified human effort. If a “penetration test” is priced in the low hundreds of pounds, or is being offered as a quick online purchase, it’s a vulnerability scan.
- There’s no scoping conversation. Before any legitimate penetration test begins, there should be a detailed discussion about scope, rules of engagement, target systems, testing constraints, and what’s in and out of bounds. If a provider is ready to start immediately without this conversation, that should be a red flag for your pen test.
- The report arrives within hours. A genuine penetration test takes days. If your “penetration test” report arrives quickly or even on the same day that you purchased the service, you have a vulnerability scan report.
- No named tester is identified. A penetration test should identify who conducted it and evidence their qualifications. A vulnerability scan report typically lists the tool used, not a person.
- The provider can’t evidence CREST or CHECK accreditation. In the UK, these are the recognised accreditations for penetration testing. CREST certifies both the organisation and individual testers. CHECK is required for government and public sector engagements. If a provider isn’t accredited, they may not be conducting penetration testing to the standard you’re paying for.
- The report lists vulnerabilities with CVSS scores but no proof of exploitation. A penetration test report includes evidence that vulnerabilities were actively exploited including screenshots, data samples, access logs, and a narrative of how the attack progressed. A vulnerability scan report lists findings with severity ratings.
DigitalXRAID is accredited by CREST and holds CHECK (NCSC) assurance status. Our CREST OVS certification also covers application penetration testing. Every test is conducted by named, certified testers following defined methodologies.
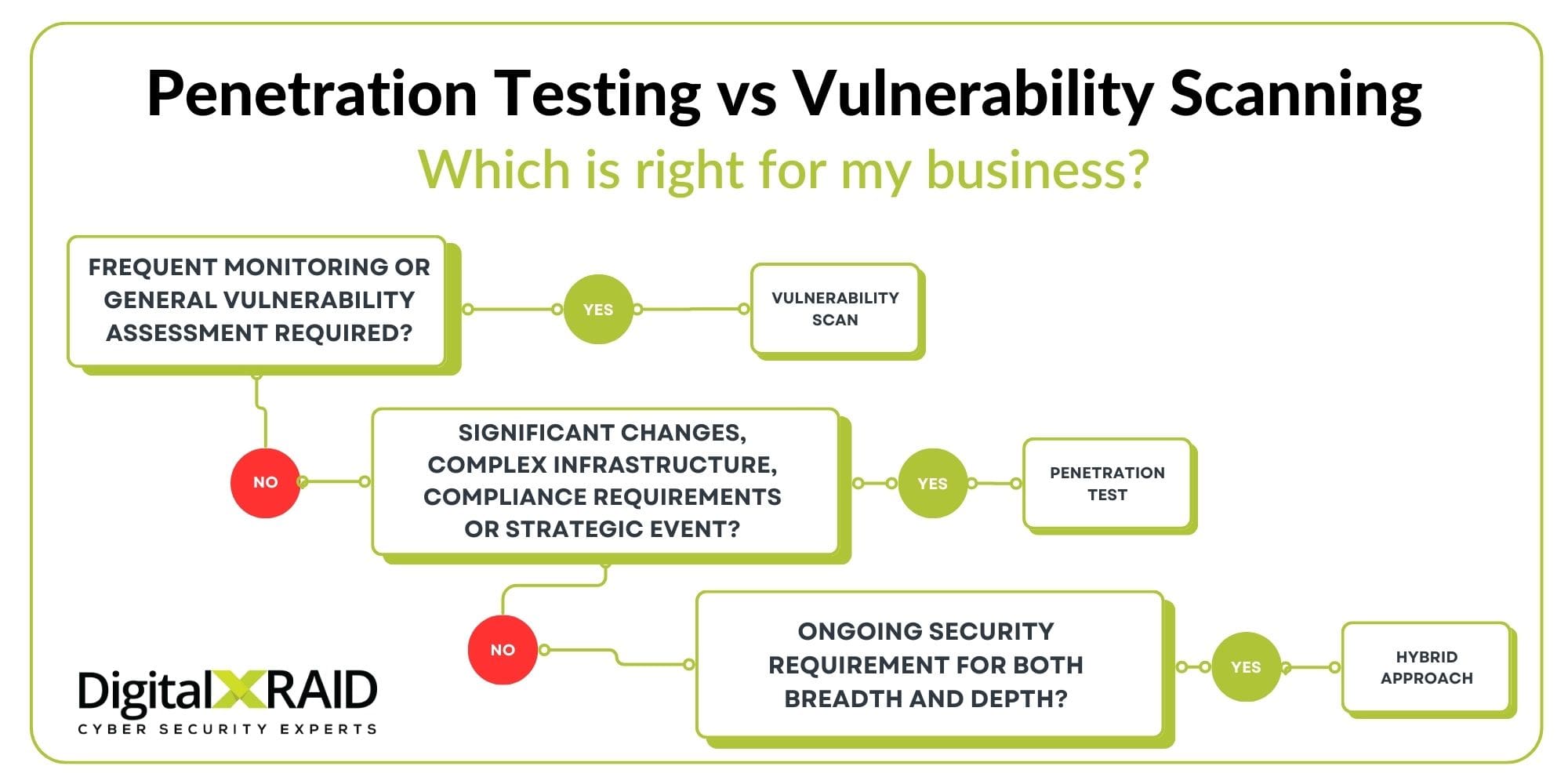
When to Use a Pen Test vs When to Use a Vulnerability Scan
The decision isn’t really about choosing one over the other. Most organisations that take security seriously use both, with scans providing continuous high level coverage and penetration tests providing periodic depth.
But there are circumstances where one is the right starting point, and others where a pen test is non-negotiable.
Use Vulnerability Scanning When…
Vulnerability scanning is right for routine, continuous security monitoring across your estate. Run scans monthly as a baseline, and after any significant change to your infrastructure: new system deployments, software updates, cloud migrations, or changes to network configuration.
Scans are also the right tool for verifying that patches have been applied correctly and that no new vulnerabilities have been introduced by recent changes.
If you’re working within a tight budget and need to maintain a baseline security posture across a broad attack surface, managed vulnerability scanning gives you the most consistent coverage for your investment. It should be viewed as a hygiene practice, not a one-off assessment.
Use Penetration Testing When…
Penetration testing is the right choice when you need to understand how your defences would hold up against a real attacker. This includes annual testing as a minimum best practice, pre-launch of a new system, application, or product, following a significant infrastructure change, merger and acquisition, after a security incident, to understand how the breach occurred and whether further exposure exists, and when compliance requires it.
Penetration testing is also the right choice when you need to communicate security risk to a board or senior leadership.
A vulnerability scan report is a technical document. A penetration test report, with its narrative of how far a tester got and what they could access, is the kind of evidence that makes risk tangible to non-technical stakeholders and justifies security investment.
Why a Combined Approach is Usually the Right Answer
For most organisations, the strongest security testing strategy combines both.
Vulnerability scanning keeps you aware of known weaknesses on a continuous basis, ensuring your patch management is current and your attack surface is understood.
Penetration testing validates your defences against realistic attack scenarios at regular intervals, uncovers what scanning misses, and provides the independently verified evidence that compliance frameworks and insurers require.
Breast Cancer Now works with DigitalXRAID on exactly this basis, combining regular automated vulnerability scanning with manual penetration testing across their infrastructure and web applications. The hybrid approach has strengthened their security posture, and ensured their protection keeps pace with infrastructure changes.
DigitalXRAID’s Penetration Testing and Vulnerability Management Services
DigitalXRAID is CREST-accredited and CHECK-certified (NCSC), with CREST OVS certification for application penetration testing. Our penetration testing services cover infrastructure (internal and external), web applications, mobile applications, cloud environments, social engineering, and red team exercises, all conducted by named, certified testers following structured methodologies aligned to industry leading methodologies including OWASP and OSINT.
Our managed vulnerability scanning service combines industry-leading, CREST-approved tooling with human expert oversight. That oversight matters: automated scanners generate false positives, and without expert verification, your team can spend significant time chasing findings that don’t represent real risk.
Our experts review results, filter noise, and provide clear, prioritised guidance on what needs to be addressed and when.
Both services feed into our OrbitalX portal, giving you real time visibility of your vulnerability status, remediation progress, and testing history in one place, accessible to technical teams and board-level stakeholders with the level of detail appropriate to each.
Final Thoughts: Vulnerability Scan vs Penetration Test
A vulnerability scan tells you where the weaknesses are. A penetration test tells you what an attacker could do with them. Both are valuable, both are necessary, and neither replaces the other.
If you’re making decisions about which to prioritise, start with your compliance obligations and your risk profile. If a framework you operate under requires penetration testing, there’s no alternative.
If you’re building a continuous security programme from scratch, managed vulnerability scanning gives you the broadest coverage for your investment while you work towards annual penetration testing.
What matters most is that you’re getting what you’re paying for. Insist on CREST or CHECK accreditation, ask for named testers, and expect a detailed scoping conversation before any engagement begins.
If you’d like to discuss your security testing requirements and understand what approach makes sense for your organisation, get in touch with the DigitalXRAID team today.
FAQs: Pen Testing vs Vulnerability Scanning
What is the difference between a pen test and a vulnerability scan?
A vulnerability scan is an automated process that checks your systems against databases of known vulnerabilities (CVEs) and produces a prioritised list of weaknesses. A penetration test is a manual, expert-led assessment in which a certified tester actively attempts to exploit vulnerabilities, chain weaknesses together, and demonstrate the real-world business impact of a successful attack. A vulnerability scan identifies that a weakness exists. A penetration test shows whether it can be exploited, how, and what the consequences would be.
Can a vulnerability scan replace a penetration test?
No. A vulnerability scan cannot replace a penetration test. Scans only identify known vulnerabilities from CVE databases. They cannot detect business logic flaws, chain vulnerabilities together, identify unknown attack paths, or produce proof of exploitation. Compliance frameworks including PCI DSS, DORA, and NIS2 treat penetration testing and vulnerability scanning as separate, non-substitutable requirements. Using a scan where a penetration test is required means your organisation is neither compliant nor as secure as it believes itself to be.
How often should I run vulnerability scans?
Monthly vulnerability scans are standard best practice for most organisations. Critical systems and systems handling sensitive data should be scanned at least quarterly, and scans should be triggered by any significant change to your infrastructure, including new system deployments, software updates, cloud migrations, and network configuration changes. The goal is continuous awareness of your known vulnerability exposure across your estate.
How often should I conduct a penetration test?
Annual penetration testing is the recognised minimum for most organisations and aligns with the requirements of ISO 27001, PCI DSS, and other frameworks. Additional tests should be conducted after significant system changes, major infrastructure migrations, before launching new products or services that handle sensitive data, after a security incident, and in response to specific compliance triggers such as DORA or NIS2 requirements. Risk-based organisations may test more frequently for their highest-value systems.
What does CREST accreditation mean for penetration testing?
CREST is an internationally recognised professional body that certifies penetration testing organisations and individual testers against rigorous technical and ethical standards. In the UK, CREST accreditation is the recognised mark of quality for penetration testing. It means the organisation has been independently assessed, its testers hold current certifications, and its methodologies meet a defined professional standard. CHECK certification, delivered under NCSC assurance, is additionally required for penetration testing engagements involving UK government and public sector systems.
Do I need both penetration testing and vulnerability scanning?
For most organisations, yes. Vulnerability scanning provides continuous, broad coverage of known weaknesses at a cost that makes regular assessment feasible. Penetration testing provides periodic, deep validation of your defences against realistic attack scenarios, uncovering what scanning misses. The two work together: scanning keeps your patch management current and your attack surface understood; penetration testing confirms whether your controls hold up under pressure and produces the evidence that compliance frameworks and senior stakeholders require.
How much does a penetration test cost in the UK?
The cost of a penetration test in the UK depends on scope, the type of testing required, the complexity of your environment, and the number of days of tester time involved. A straightforward infrastructure penetration test for a mid-sized organisation typically ranges from £2,000 to £8,000. Web application testing, red team exercises, and multi-environment assessments carry higher fees reflecting the time and expertise involved. If a provider is quoting significantly below this range for a “penetration test,” it is very likely a vulnerability scan. Always ask for a detailed scope and evidence of CREST or CHECK accreditation before committing.


