Cyber Kill Chain: How Security Teams Can Disrupt Attacks Early
Cyberattacks continue to exact a staggering toll on businesses worldwide. Recent global estimates put the annual cost of cybercrime at around $9.5 trillion with the average cost of a data breach reaching an all-time high of $4.45–4.88 million, a figure that has climbed roughly 15% in just the past three years.
Beyond direct financial losses, organisations face severe operational disruption, reputational damage, and legal penalties after a major breach. In just one year, over 8 billion records were exposed in publicly reported incidents, underscoring the massive scale of impacted customers and data at risk.
Many of these breaches might have been mitigated with earlier detection and response, before attackers could fully execute their plans. IBM’s threat report found that when an organisation’s security team caught a breach early, it shortened the incident lifecycle by 61 days and saved nearly $1 million on average.
Unfortunately, most organisations struggle to spot intrusions at the initial stages due to a lack of internal resources and specialist skills. A typical breach can go unnoticed for 200+ days in many cases, giving attackers ample time inside of networks and systems to exfiltrate data and cause damage.
Breaches that begin with stealthy tactics like stolen login credentials are especially slow to be discovered without the correct measures in place, taking an average of nearly 11 months to detect and contain and costing $4.62 million on average.
One of the most effective ways to mitigate attacks early is by leveraging dark web threat intelligence and proactive security monitoring. Many attackers leave digital traces before they strike, ranging from hackers scouting for targets, to stolen credentials or network access being sold on underground forums.
In fact, compromised credentials remain one of the most common entry points, responsible for more than one third of breaches. A growing share of the victims being advertised by these Initial Access Brokers (IABs) are large enterprises. Nearly 33% of access-for-sale listings in the early part of this year targeted organisations with over $1 billion in revenue, up from 27% the year before.
If your organisation can identify that credentials or vulnerabilities are being sold, before a breach occurs, you can respond immediately by disabling exposed accounts, patching systems, or blocking the adversary’s route before the attack progresses to the next stage.
In this article, we’ll share insights into the Cyber Kill Chain framework, and how you can disrupt cyberattacks early to better protect your business.
Key Takeaways
- The Cyber Kill Chain provides a structured model to detect and disrupt attacks early, before adversaries can complete their objectives.
- Early detection can shorten breach lifecycles by 61 days and reduce breach costs by nearly $1 million, according to IBM.
- Compromised credentials account for over a third of breaches, and are often sold on the dark web before attacks begin.
- The seven Kill Chain stages—Reconnaissance to Actions on Objectives—can each be disrupted with proactive security monitoring and threat intelligence.
- Combining the Cyber Kill Chain with frameworks like MITRE ATT&CK enhances detection and defence by offering both high-level and detailed adversary insights.

The Role of the Cyber Kill Chain in Modern Cybersecurity
The Cyber Kill Chain framework provides organisations with a structured model to proactively identify, understand, and disrupt cyberattacks. Developed by Lockheed Martin, this model details the lifecycle of cyberattacks, offering insights into each stage.
Defenders can catch threats earlier in the Cyber Kill Chain using this step by step model, from initial reconnaissance and resource development, through to infiltration, lateral movement, and finally action on objectives like data theft or ransomware. By “shifting left” – intercepting attackers in the earliest Kill Chain phase, such as reconnaissance or weaponisation – security teams can prevent an incident from ever fully materialising.
The Cyber Kill Chain remains highly relevant as cyber threats become more sophisticated. By adopting this proactive security approach, your organisation can effectively mitigate risks before they escalate into full scale incidents.
Understanding the Cyber Kill Chain as a Threat Model
The Cyber Kill Chain consists of seven critical stages:
- Reconnaissance – Attackers gather intelligence to identify vulnerabilities.
- Weaponisation – Creation of malicious payloads.
- Delivery – Payload delivery through email, web, or removable media.
- Exploitation – Compromise of vulnerabilities.
- Installation – Establishment of persistent threats.
- Command & Control (C2) – Remote control of compromised assets.
- Actions on Objectives – Execution of malicious goals, such as data exfiltration.
Mapping these stages helps security teams understand potential threats and enables more effective defence strategies.
Why Security Teams Must Proactively Disrupt Attacks
Proactive disruption of cyberattacks is essential for avoiding severe financial and reputational damage. Organisations adopting a reactive security posture risk greater vulnerability, allowing threats to escalate unchecked.
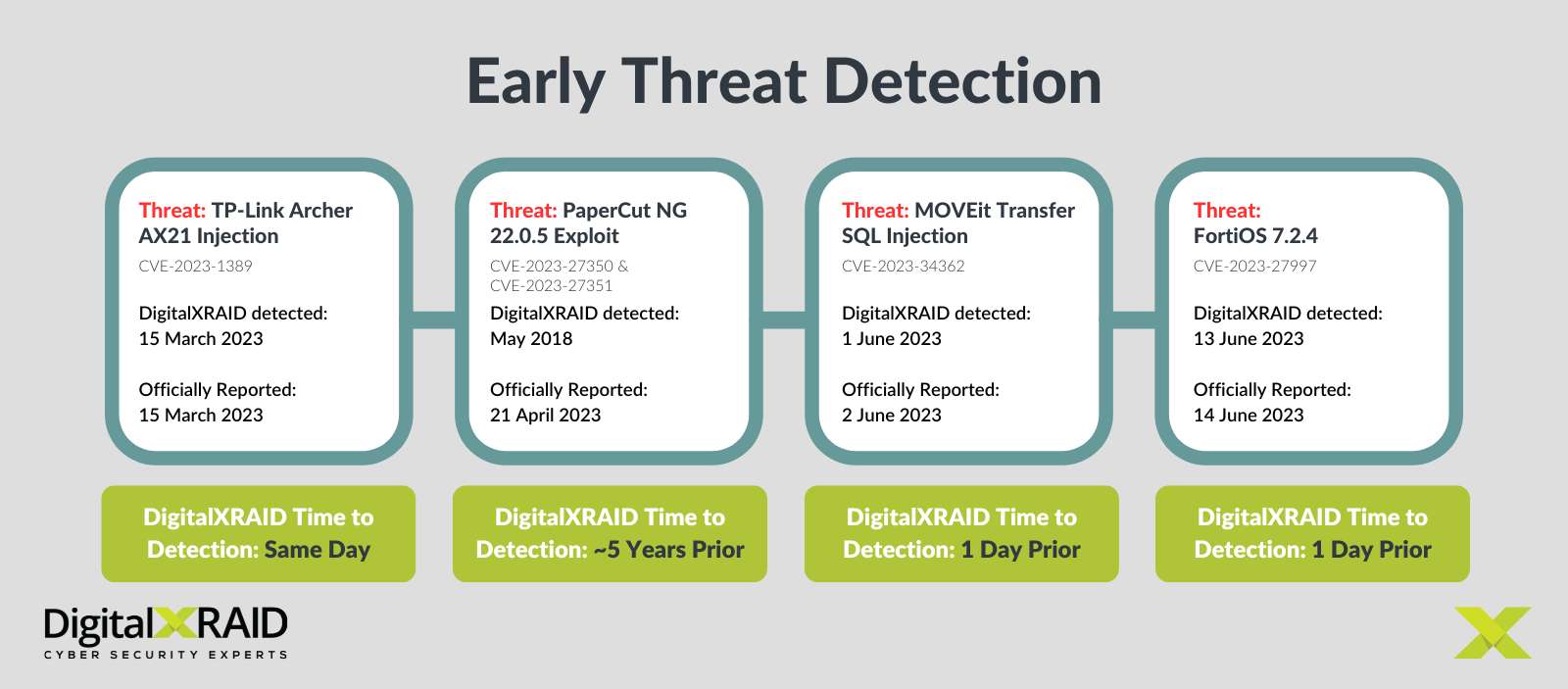
Early disruption at any Cyber Kill Chain stage significantly reduces attack effectiveness. The importance of early detection and dark web intelligence becomes even clearer when examining recent high profile cyberattacks that could have been prevented with early detection.
Snowflake’s data breach in early 2024 is an example of how attackers can exploit available dark web credentials with devastating consequences. Over 165 organisations worldwide were quietly compromised when threat actors logged into their Snowflake accounts using valid usernames and passwords that had been previously stolen via infostealer malware. Attackers accessed numerous companies’ cloud databases – an initial access step in the kill chain that went undetected as it appeared to be legitimate login traffic. Once inside, they conducted reconnaissance and ultimately exfiltrated large data sets from at least nine victim organisations, collectively exposing hundreds of millions of customer records. Had the targeted companies been monitoring dark web markets or infostealer dump sites for their exposed usernames and passwords, they might have detected the threat before intrusion.
In early 2024, UnitedHealth’s Change Healthcare division suffered a devastating ransomware attack. The incident began when attackers gained initial access via a stolen login credential for the company’s Citrix remote access gateway and ultimately deployed BlackCat (ALPHV) ransomware on the infrastructure. The cybercriminals were able to steal 6 terabytes of data prior to encryption and disrupted a range of healthcare services. This attack’s early stages were detectable with the right measures in place. The fact that privileged Citrix account credentials were on the dark web and being used from unusual locations could have been picked up either via dark web monitoring or proactive SOC alerts.
Breaking Down the Cyber Kill Chain Stages
The Cyber Kill Chain is one of the more commonly referenced frameworks in cybersecurity. The framework is a part of the Intelligence Driven Defence model for identification and prevention of cyber intrusion activity, highlighting the different stages of an attack a threat actor must complete in order to achieve their objective.
The seven Cyber Kill Chain steps include:
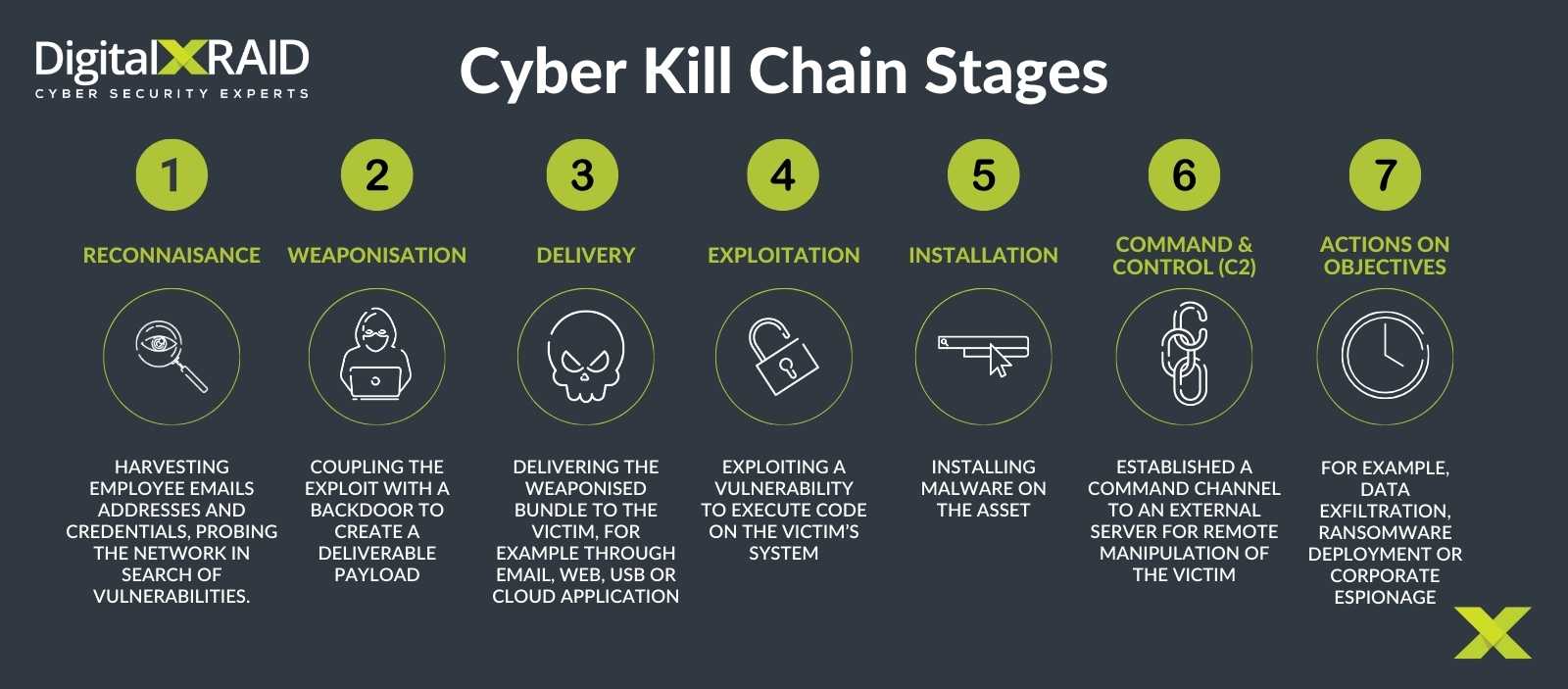
Reconnaissance – How Attackers Identify Vulnerabilities
Reconnaissance involves threat actors collecting data on potential targets through methods such as OSINT, phishing, and dark web forums. Organisations should utilise proactive threat intelligence solutions, enabling early detection and intervention before attackers progress further.
Weaponisation – Turning Exploits into Cyber Weapons
Weaponisation occurs when attackers develop malware to exploit identified vulnerabilities. Security teams must conduct regular vulnerability assessments, apply timely patches, and maintain robust endpoint protection to neutralise these threats before delivery.
Delivery – How Threats Enter an Organisation’s Network
Common delivery methods include phishing emails, malicious websites, and infected USB drives. Robust email security measures, advanced web filtering, and endpoint protection solutions are essential to disrupt malicious payloads effectively.
Exploitation – Taking Advantage of Security Weaknesses
Exploitation involves attackers leveraging unpatched software and weak password security practices. Effective patch management policies and strong password protocols significantly mitigate these risks.
Installation – Gaining Persistence & Establishing Access
During installation, attackers embed malware to maintain network access. Endpoint detection and response (EDR) solutions help detect and neutralise persistent threats, preventing attackers from gaining prolonged access.
Command & Control – How Attackers Move Inside the Network
Command & Control servers manage compromised systems, enabling lateral movement. Network segmentation, intrusion detection systems (IDS), and zero trust architectures effectively disrupt this internal threat movement.
Actions on Objectives – Data Exfiltration & System Compromise
Following the previous Cyber Kill Chain stages. attackers now aim to exfiltrate sensitive data or disrupt systems. Implementing data loss prevention (DLP) tools and encryption ensures data protection and prevents these attackers from achieving their ultimate objectives.
How Security Teams Can Disrupt Attacks at Each Stage
Proactive security measures, continuous monitoring, and rapid response capabilities disrupt threats effectively across all of the Cyber Kill Chain phases.
Partnering with a dedicated cybersecurity provider for managed Security Operations Centre (SOC) services significantly enhances your capability to detect and disrupt threats early. A managed SOC provides continuous vigilance and expert analysis, ensuring rapid identification and response to suspicious activity within minutes, before it escalates into a major incident.
Stopping Reconnaissance with Threat Intelligence & Monitoring
Threat intelligence can provide you with actionable information about attackers, their tools, infrastructure, and the methods to detect threats in the network – and most importantly how to prioritise the response to those threats. Leveraging threat intelligence platforms and SIEM systems enables real time monitoring and early threat detection.
A managed SOC provider will utilise the most advanced tooling and have access to the widest pool of dark web and threat intelligence data. Educating your employees to recognise social engineering attacks is equally critical.
Blocking Malware Delivery with Advanced Email & Endpoint Security
Working with an expert cybersecurity service provider provides next-gen security monitoring solutions to identify attacks before they can cause damage. Antivirus, email filters, and anti-phishing tools also significantly reduce malware risks. Regular endpoint updates and multi-factor authentication (MFA) further enhance organisational security. With the oversight of a managed SOC, these protections can be continuously monitored, quickly responding to emerging threats.
Containing Exploits with Network Segmentation & Zero Trust
Network segmentation and Zero Trust security models limit the attackers’ lateral movement across your infrastructure. Firewalls, VPNs, and micro-segmentation can further contain and neutralise threats. A managed SOC actively manages these strategies, adjusting controls based on evolving threat intelligence.
Detecting Lateral Movement & Preventing Command & Control
Behavioural analytics and network monitoring tools rapidly detect suspicious activity. Quick incident response prevents further threat escalation. Managed SOC analysts provide crucial oversight, detecting subtle indicators of lateral movement or C2 communications and swiftly initiating countermeasures.
Incident Response & Mitigating Damage Before Data is Stolen
Should the inevitable occur, and a successful breach is identified, an effective incident response plan that includes rapid containment and investigation, secure cloud storage, and robust backup systems to mitigate threats, is essential. A managed SOC team expertly coordinates these efforts, identifying any successful breaches early, mitigating threats in minutes, and minimising the impact of breaches by rapidly restoring secure operations.
The Limitations of the Cyber Kill Chain & Evolving Threats
While beneficial, the Cyber Kill Chain alone may not capture the complexity of modern day threats. Attackers increasingly adopt multi-stage approaches, complicating detection and prevention.
Why Attackers Have Adapted Beyond the Traditional Kill Chain Model
Adversaries now exploit more sophisticated tactics such as supply chain attacks, insider threats, ransomware-as-a-service (RaaS), adaptive malware and multi-stage breaches, highlighting the need for advanced, adaptable defences.

Cyber Kill Chain vs MITRE ATT&CK
How MITRE ATT&CK & Other Frameworks Complement the Cyber Kill Chain
The MITRE ATT&CK framework complements the Cyber Kill Chain by providing granular insights into adversary behaviours. Combining these models creates comprehensive security strategies.
Differences between Cyber Kill Chain and MITRE ATT&CK
Aspect |
Cyber Kill Chain |
MITRE ATT&CK |
Scope |
Linear stages | Extensive adversary behaviours |
Detail Level |
High-level framework | Detailed tactical view |
Adaptability |
Fixed stages | Continuously updated |
Practical Utility |
Good for high-level plans | Useful for detailed analysis |
AI & Machine Learning in Cybersecurity – Enhancing Threat Detection
AI and machine learning in cyber security can effectively detect unknown threats by identifying anomalous patterns. DigitalXRAID’s Managed SOC Service utilises advanced AI/ML powered technologies such as Microsoft Sentinel to stay ahead of evolving threats, enhancing detection and response capabilities.
How DigitalXRAID Helps Businesses Disrupt Cyber Attacks
DigitalXRAID provides proactive solutions across all stages of the Cyber Kill Chain, ensuring continuous threat monitoring, real time incident response, and comprehensive threat intelligence.
DigitalXRAID’s Threat Intelligence & 24/7 Monitoring Services
Our dedicated services continuously monitor the dark web, alerting your organisation to emerging threats in real time, allowing for proactive defence measures.
DigitalXRAID’s Threat Intelligence – called The Hive – draws from the most comprehensive picture of the current state of cybersecurity. Our SOC analysts and CTI specialists are fed data from the entire internet, including the dark web, every day, to map out adversaries and their infrastructure. This gives the SOC team greater visibility into the hidden sites where cybercriminals instigate their attacks and enhances proactive threat protection.
The insight that DigitalXRAID’s SOC team gain across various customer environments, as well as the years of experience and industry accreditations held, provide an aggregate value for threat intelligence and monitoring that a single organisation couldn’t achieve alone. Clients benefit from the ‘one affected, all protected’ extended threat detection (XDR) powered SOC service that DigitalXRAID provides.
How Our SOC Analysts Identify & Stop Attacks in Real Time
DigitalXRAID’s SOC analysts monitor our customers’ infrastructure 24/7/365 to expertly identify, monitor, and neutralise threats in just 8 minutes, including P1 incidents. This prevents breaches causing significant damage occurs.
Case Study: How DigitalXRAID Prevented a Ransomware Attack
DigitalXRAID successfully mitigated an attempted account compromise attack on Lambert Smith Hampton. DigitalXRAID’s SOC analysts immediately notified Lambert Smith Hampton that account credentials had been leaked on the dark web following the reconnaissance phase in the Cyber Kill Chain, so investigations could be initiated.
As the credentials were being used in an attempted access breach, DigitalXRAID worked closely with Lambert Smith Hampton to identify the source and ingress point and any further instances of that particular IP address. The attempt was mitigated and neutralised within 10 minutes. Within an hour, a full incident report had been delivered to Lambert Smith Hampton which could be shared with the board, detailing the 6 other accounts which had been attempted but failed due to the MFA enforcement during the incident response that DigitalXRAID had initiated on discovery of the leaked credentials.
DigitalXRAID was also able to provide clarity to a client as part of an acquisition due diligence exercise, where the company being acquired had disclosed that it had suffered a ransomware attack.
DigitalXRAID’s SOC analysts utilised dark web and threat intelligence information to understand what the ransomware attack entailed and were able to analyse the data that had reportedly been exposed. The CTI specialists were able to offer reassurance that the data that had been exfiltrated wasn’t sensitive in nature and had been over-exaggerated by the attacker, so no major risk was present for the acquisition.
Why Organisations Must Evolve Their Security Strategies
Adapting to proactive security strategies continuously ensures organisations stay resilient against evolving cyber threats.
Key Takeaways on Cyber Kill Chain & Attack Prevention
- Proactive threat disruption early in the Cyber Kill Chain is essential
- Continuous monitoring and rapid response are critical
- Combining Cyber Kill Chain and MITRE ATT&CK enhances security effectiveness
Next Steps: Strengthening Your Security with DigitalXRAID’s Expertise
Contact DigitalXRAID today to for expert consultation on how to elevate your cybersecurity strategy and proactively safeguard your organisation against cyber threats, especially early in the Cyber Kill Chain.


