Cyber Incident Response Planning: A Complete Guide for UK Organisations
When a cyberattack hits your organisation, the decisions you make in the first hour will define the outcome. Whether it’s ransomware encrypting your servers at 2am, a phishing campaign that’s handed attackers your credentials, or a data exfiltration that you only discover weeks later, the difference between a managed recovery and a catastrophic breach often comes down to one thing – whether you had a plan in place before the incident began.
Cyber incident response planning is the process of preparing your organisation to detect, contain, and recover from cyberattacks in a structured, coordinated way. It’s no longer a ‘nice to have’.
Regulators, insurers, and boards increasingly expect to see documented, tested plans in place, and the incoming UK Cyber Security and Resilience Bill will extend mandatory incident reporting obligations to a significantly wider set of UK organisations.
In this guide, we’ll cover what cyber incident response planning involves, what your plan needs to include, how to build and test it, and why partnering with an expert managed security service provider can give you a decisive advantage when it matters most.
Key Takeaways
- Cyber incident response planning is the structured preparation that enables your organisation to detect, contain, and recover from cyberattacks quickly and with minimal damage.
- A well-tested plan reduces downtime, limits financial losses, protects your regulatory standing, and preserves customer trust.
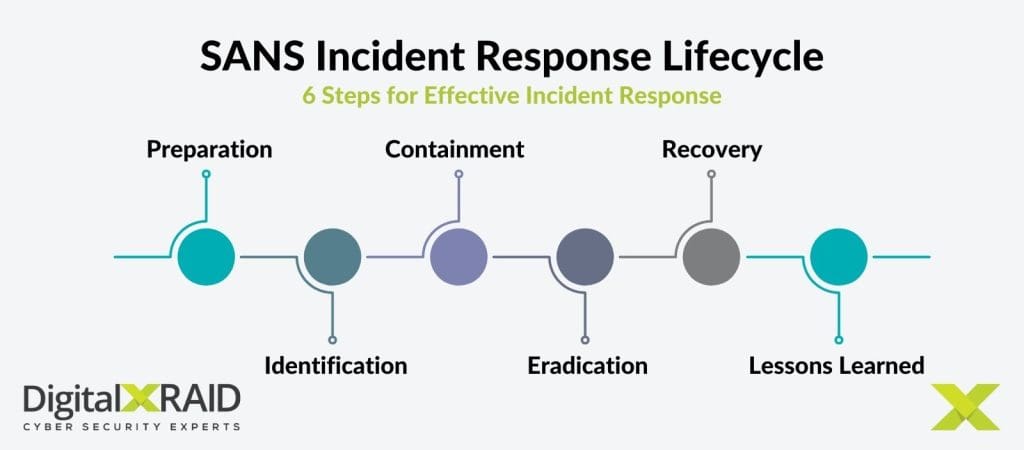
- Effective planning follows a recognised lifecycle: preparation, detection, containment, eradication, recovery, and lessons learned.
- UK organisations face escalating regulatory obligations under GDPR, NIS2, DORA, and the upcoming Cyber Security and Resilience Bill, making a tested incident response plan essential.
- Clear roles, incident-specific playbooks, and regular simulation exercises prepare your teams to act under real attack conditions.
- Partnering with a CREST-accredited and NCSC-assured managed security provider gives you 24/7 expert response capability and government-assessed incident handling.
Why Cyber Incident Response Planning Matters
Cyberattacks are inevitable. According to IBM’s Cost of a Data Breach Report, it takes organisations an average of 241 days to identify and contain a breach. That’s eight months of exposure, and every day of that window carries financial, operational, and reputational cost.
The global average cost of a data breach now stands at $4.44 million, and for UK organisations the regulatory penalties layered on top can dwarf the direct costs of recovery.
In June 2024, NHS pathology provider Synnovis was hit by a ransomware attack that cost an estimated £32.7 million, disrupted services across five NHS trusts, delayed over 11,000 outpatient appointments and elective procedures, and took months before services were fully restored. The attack was reportedly enabled by the absence of two-factor authentication on key systems.
A tested cyber incident response plan doesn’t prevent attacks occurring. It dramatically changes how quickly you can contain them, how well you communicate during the crisis, and how completely you recover.

What is Cyber Incident Response Planning?
Cyber incident response planning is the process of creating, testing, and maintaining a documented framework that guides how your organisation detects, manages, and recovers from a cyber security incident.
The output of that process is an incident response plan (IRP). The plan is a structured document that defines roles and responsibilities, decision-making processes, escalation paths, communication protocols, and step-by-step playbooks for the most likely attack scenarios your organisation faces.
Done well, a plan ensures that when an incident occurs, your technical teams, legal advisors, communications leads, and executive leadership all know what they’re doing and in what order, without having to work it out under pressure.
Why every UK organisation needs an incident response plan
In the UK, both large enterprises and mid-sized organisations face a persistent and growing cyber threat landscape. The ICO records thousands of breach notifications each year.
Sectors including finance, healthcare, energy, and government face mandatory reporting requirements under DORA and NIS2, and the UK’s Cyber Security and Resilience Bill will extend 24-hour incident reporting obligations to a significantly wider set of organisations, including managed service providers and supply chain entities.
If you handle personal data, deliver essential services, or operate in a regulated sector, your incident response plan isn’t just a risk management tool, it’s a legal and governance requirement.
What Are the Stages of the Incident Response Planning Lifecycle?
Most recognised frameworks, including the NIST Cybersecurity Framework, NIST SP 800-61, and the SANS Incident Response Lifecycle, follow the same core stages. Understanding these stages is the foundation of effective cyber incident response planning.
Preparation
Preparation is where your plan is built and your readiness is established. This includes appointing your incident response team, defining roles and decision-making authority, deploying the right technology (SIEM, SOAR, EDR), developing playbooks for your highest-risk incident scenarios, and training your people through regular simulation exercises.
The goal is to ensure that when an incident starts, you’re not figuring out who does what. That’s already decided.
Detection and analysis
Early detection is everything. Monitoring tools, threat intelligence feeds, and your Security Operations Centre (SOC) work together to surface anomalies, including unusual traffic patterns, unauthorised access attempts, endpoint alerts, lateral movement indicators.
Clear alert triage processes let you distinguish genuine incidents from false positives and calibrate the right level of response.
Containment
Containment limits the damage while investigation continues. Depending on the attack type, this means isolating affected systems, revoking compromised credentials, or blocking attacker-controlled infrastructure. Speed matters – the faster you contain, the less an attacker can do.
Eradication
Once contained, you need to remove the threat entirely. Steps taken at this stage should include malware purged, vulnerabilities closed, and backdoors eliminated. You shouldn’t declare eradication complete until you’re confident the attacker has no remaining foothold in your environment.
Recovery
Recovery restores normal operations, typically using clean backups and verified system states. For ransomware attacks in particular, this stage can be lengthy and technically complex.
Clear recovery time objectives, set during the planning phase, give your teams measurable targets to work towards.
Post-Incident review and lessons learned
Every incident is an opportunity to improve. A structured review captures what happened, what worked, what didn’t, and what changes are needed in your plan, your technology, or your processes.
Your incident response plan should be a living document that gets stronger after every exercise and every real event.
What Should a Cyber Incident Response Plan Include?
While the specifics vary by organisation, sector, and risk profile, a well defined incident response plan will always address the following:
- A defined scope and purpose, clarifying what constitutes a security incident for your organisation and what triggers activation of the plan.
- A named incident response team with clearly assigned roles across IT security, IT operations, legal, compliance, communications, and executive leadership, along with deputised cover for each role.
- An incident severity classification framework, so your team can quickly determine the urgency and scale of response required.
- Incident-specific playbooks covering your highest-priority scenarios, including ransomware, business email compromise, data exfiltration, phishing, and insider threat.
- Communication protocols, covering both internal escalation paths and external communications to customers, partners, and regulators.
- A clear process for ICO breach notification, including the 72-hour reporting obligation under UK GDPR, who’s responsible for the assessment, and how the notification will be prepared and submitted.
- A post-incident review process, and a schedule for regular plan reviews and simulation testing.
The NCSC recommends starting with playbooks for your three to five highest-risk incident types and building from there, rather than trying to document every possible scenario from the outset.

What Happens if You Don’t Have a Cyber Incident Response Plan?
Without a tested plan, organisations face a predictable set of consequences when an incident occurs.
Operational disruption and financial losses
The absence of clear roles and decision-making authority creates confusion and delay at exactly the moment when speed is critical. Systems may be offline for days or weeks while teams try to understand the scope of the attack and agree on a course of action.
The Marks & Spencer ransomware attack by Scattered Spider brought their online operations to a standstill, shutting down contactless payments and click-and-collect services for an extended period, with reported losses of up to £300 million.
The Synnovis ransomware attack we mentioned earlier cost £32.7 million and took months to fully recover from. Unfortunately, these aren’t outliers, they’re examples of what unplanned incident response can look like at scale.
Compliance, regulatory, and reputational risks
Without a tested plan, meeting the ICO’s 72-hour breach notification requirement becomes significantly harder. NIS2 and DORA extend similar obligations in critical sectors, and the Cyber Security and Resilience Bill will add mandatory 24-hour reporting requirements for a broader set of UK organisations.
Failure to notify on time exposes you to fines, regulatory enforcement action, and the reputational damage of a poorly managed public disclosure.
How to Build a Cyber Incident Response Plan: A Step-by-Step Approach
Building an effective incident response plan requires combining recognised frameworks with the realities of your organisation’s size, sector, and risk profile. A template is a starting point, not a finished product.
Align with a recognised framework
The NIST Cybersecurity Framework and the SANS Incident Response Lifecycle provide proven structures.
In the UK and EU, NIS2, DORA, and the Cyber Security and Resilience Bill shape what’s expected in regulated sectors.
Tailor the plan to your organisation
A financial institution might prioritise customer data protection and regulatory reporting. A healthcare provider focuses on patient data and service continuity. Smaller organisations need a streamlined, practical plan that’s achievable with the resources available.
Your plan should reflect your actual threat landscape and risk profile, not a generic one.
Build your incident response team before you need it
Preparation lays the foundation for your incident response plan and is an essential starting point. Define who’s in the core team, how they’re contacted out of hours, and who deputises if someone’s unavailable. Extend the team beyond IT to include legal, compliance, communications, and senior leadership.
Regulators and insurers will want to see evidence that incident response is a business-level function, not just an IT one.
Test the plan regularly
The worst moment to discover gaps in your plan is during a live incident. Table-top exercises walk your team through realistic scenarios, testing decision-making and communications in a lower-pressure environment.
DigitalXRAID runs structured cyber incident exercises for clients to help to build genuine confidence in their ability to respond effectively under pressure.
Keep it current
Review your plan at least annually, after every real or simulated incident, and whenever there are significant changes to your IT environment, your organisational structure, or the regulatory landscape. Your adversaries don’t stand still, and neither should your plan.

How Cyber Incident Response Planning Supports Board-Level Governance
Cyber incident response planning should not be left just to your IT teams. Regulators, insurers, and investors increasingly expect boards to demonstrate active oversight of cyber risk management.
The NCSC’s Cyber Governance Code of Practice sets out five pillars for board-level governance, one of which is incident planning. It expects boards to ensure their organisations have tested plans in place, that incident response is linked to business continuity, and that cyber risk is treated as a strategic business issue rather than a purely technical one.
Positioning your incident response plan as a governance priority gives it the visibility, funding, and executive accountability it needs to be genuinely effective. It also demonstrates to customers, partners, and auditors that your organisation takes resilience seriously, which increasingly matters for contract retention and supplier qualification.
How an MSSP Strengthens Your Cyber Incident Response Planning
Many organisations lack the in-house resources to maintain the 24/7 monitoring and response capability that a managed SOC service provides. Building the technology stack and expertise internally is expensive, and the UK cyber skills shortage makes it harder still.
Partnering with a CREST-accredited and NCSC-assured managed security service provider (MSSP) gives you access to tested methodologies, government-assessed response capabilities, and round-the-clock coverage that most organisations can’t replicate on their own.
DigitalXRAID is a CREST-accredited and NCSC Cyber Incident Response Level 2 Assured Service Provider. These recognitions require independent assessment against the NCSC’s technical standards and confirms our capability to handle the full range of common, financially motivated cyberattacks, including ransomware, business email compromise, data exfiltration, and phishing breaches.
Our 24/7 Security Operations Centre operates alongside our incident response capability, meaning the team that responds to your incident is drawing on live threat intelligence and active monitoring data from day one.
We can support you through every stage, from initial triage and containment, through to ICO notification, and to your post-incident report and hardening recommendations.
Want a practical framework to build from? Read the 8 Steps for Effective Incident Response.
Final Thoughts: Build Your Cyber Incident Response Plan
Cyberattacks are not going away. Cyber incident response planning gives you the structure to respond quickly, the clarity to make good decisions under pressure, and the documentation to meet your regulatory obligations. It protects your operations, your customers, and your reputation, and it demonstrates to boards, regulators, and insurers that cyber risk is being managed proactively.
If you want the assurance of expert support behind your plan, DigitalXRAID’s CREST-accredited and NCSC-assured incident response service provides exactly that.
Strengthen your cyber resilience today. Get in touch with the DigitalXRAID team to discover how we can help protect your organisation.
FAQs About Cyber Incident Response Planning
What is cyber incident response planning?
Cyber incident response planning is the process of preparing your organisation to detect, contain, and recover from cyber security incidents in a structured, coordinated way. It results in a documented incident response plan (IRP) that defines roles, responsibilities, escalation paths, communication protocols, and step-by-step playbooks for the most likely attack scenarios your organisation faces.
What should a cyber incident response plan include?
An effective incident response plan includes a defined scope and activation criteria, an incident response team with clearly assigned roles across IT, legal, communications, and leadership, an incident severity classification framework, playbooks for high-priority scenarios such as ransomware and business email compromise, communication protocols for internal and external stakeholders, a process for ICO breach notification under UK GDPR, and a schedule for regular review and simulation testing.
How often should a cyber incident response plan be updated?
You should review your plan at least annually, after every real or simulated incident, and whenever there are significant changes to your IT environment, organisational structure, or regulatory requirements. Cyber threats evolve continuously, and your plan needs to keep pace.
What’s the difference between an incident response plan and a disaster recovery plan?
An incident response plan focuses on detecting, managing, and recovering from cyberattacks and security incidents. A disaster recovery plan is broader, covering recovery from events such as natural disasters, power failures, or major system outages. Both are important components of business continuity planning, and they should be cross-referenced, but they serve different purposes.
What happens if I don’t notify the ICO after a data breach?
Under UK GDPR, organisations must notify the ICO within 72 hours of becoming aware of a personal data breach that poses a risk to individuals’ rights and freedoms. Failure to notify can result in significant fines, regulatory enforcement action, and reputational consequences. A tested incident response plan that includes a clear ICO notification process helps ensure you meet this deadline even under the pressure of an active incident.
How do you test a cyber incident response plan?
Testing methods include tabletop exercises, where your team walks through a realistic attack scenario to test decision-making and communication, and technical simulations or penetration testing exercises that validate your detection and response capabilities. Regular testing builds team confidence, reveals gaps in technology or process, and is increasingly expected by cyber insurers and regulators.
What role does cyber insurance play in incident response planning?
Cyber insurance can help cover the costs of a breach, including forensic investigation, remediation, regulatory notification, and legal fees. However, many insurers require you to have a documented, tested incident response plan in place as a condition of coverage. A strong plan not only improves your insurance eligibility, it also ensures you can meet the insurer’s requirements quickly if you need to make a claim.


