Host-Based Intrusion Detection System: How It Protects Your Business
Cyberattacks are increasing each year. There are now 73 active ransomware groups, compared with 46 last year – a 56% increase in just 12 months despite law enforcement’s best efforts. Which is why advanced security measures, including host-based intrusion detection systems, have become so important.
Most businesses don’t have the resources – both in terms of tooling and specialist skills – to spot attacks early. Without sufficient protection in place, breaches can typically go unnoticed for 200 days or more.
Implementing a host-based intrusion detection system (HIDS) can significantly bolster your security posture by detecting cyber threats early, mitigating risks, and safeguarding your critical assets. But how exactly do HIDS work, and why should your business consider implementing this cyber protection measure?
In this article, we’ll be sharing what IDS is, the difference between host-based and network-based intrusion detection systems and how you can successfully implement HIDS for your business.
Key Takeaways
- Host-Based Intrusion Detection Systems (HIDS) are critical for early threat detection at the endpoint level, monitoring file integrity, user behaviour, and system changes in real time.
- HIDS provides visibility into internal threats and complements antivirus and firewall protections, making it essential for a layered defence-in-depth strategy.
- Unlike network-based solutions, HIDS can inspect encrypted data directly at the endpoint, enhancing detection of hidden or evasive threats.
- HIDS supports compliance with regulations like PCI-DSS through detailed audit logs and File Integrity Monitoring (FIM).
- HIDS alerts security teams to suspicious activity immediately, enabling faster incident response and reducing breach impact.
- DigitalXRAID offers rapid HIDS deployment, 24/7 threat monitoring and expert SOC management, helping businesses protect critical systems without adding internal resource strain.

The Growing Need for Intrusion Detection Systems
Traditional security measures are no longer enough to effectively protect your business. You must be looking at a proactive security strategy to ensure that you stay a step ahead of the evolving methods of cybercriminals.
A defence in depth strategy is needed to protect your business from hackers.
Why Cyber Threats Are More Sophisticated Than Ever
Cybercriminals are leveraging increasingly advanced attack tactics techniques and procedures (TTPs), including ransomware, phishing, and zero day attacks.
Ransomware attacks alone surged by 151% in just one year, as reported by the UK’s National Cyber Security Centre (NCSC). AI-driven tools being utilised by attackers further compounds these threats, enabling criminals to execute attacks at scale and with greater speed and precision.
The shift towards remote working and extensive cloud adoption has also expanded the attack surface, making businesses more vulnerable than ever. Traditional cyber security measures such as antivirus software and firewalls are no longer sufficient.
Types of Intrusion Detection Systems
There are two main types of Intrusion Detection Systems (IDS): Host-Based Intrusion Detection Systems (HIDS) and Network-Based Intrusion Detection Systems (NIDS).
Think of an IDS as the digital equivalent of an alarm system. It’s designed to detect and alert you to potential threats within your IT environment. When suspicious activity is detected, the detection system promptly notifies security or IT personnel, so specialists then investigate and mitigate any potential security breaches or threats.
Intrusion detection systems continuously monitor activities occurring on your network or individual host devices, analysing data to identify indicators of compromise, malicious activity, unauthorised access attempts, and any deviation from your security policies.
The most common threats identified by IDS systems include malware infections, unauthorised user access, attempted privilege escalation, and unauthorised changes to critical system configurations.
Typically IDS works alongside your firewall. While firewalls actively restrict network traffic by allowing only predefined safe connections, IDS systems permit the traffic flow, but constantly scans for signs of threats or anomalous activity that could be a threat.
The Role of HIDS in Modern Cyber Security Strategies
HIDS acts as one of your business’s first line of defence. It continuously monitors your system activities on individual endpoints, including servers, workstations, and IoT devices.

What is a Host-Based Intrusion Detection System (HIDS)?
A Host-Based Intrusion Detection System (HIDS) actively monitors individual host system such as servers, workstations, or endpoint devices and sends alerts if any suspicious activities are detected. HIDS operates through software agents installed directly onto these hosts. The agents monitor network traffic specific to the host, file access or changes, configuration updates, processes, and system and application event logs.
Unlike antivirus software, HIDS provides full visibility into internal security events, detecting unusual activity in real time and complementing your existing firewall and antivirus solutions.
HIDS is often installed on critical infrastructure, particularly servers that store sensitive or publicly accessible data. The flexibility of HIDS means it can be effectively deployed across various hosts within your organisation, ensuring comprehensive endpoint security coverage tailored to your specific operational and security requirements.
Understanding How HIDS Monitors System-Level Threats
HIDS monitors endpoints by tracking file integrity, user logins, and application behaviours. Using anomaly detection, it can identify any suspicious activities or deviations from standard operational patterns. For instance, it can detect unusual file modifications or access, or unusual privilege escalation, that may indicate an insider threat or compromised account.
How HIDS Differs from Antivirus and Firewalls
Antivirus software detects known malware signatures but can struggle with unknown threats or zero day exploits, particularly if they are newly discovered and therefore not added to the software capability.
Firewalls mainly prevent unauthorised network access from outside of the organisation but may not detect breaches occurring internally. HIDS fills this gap by providing deep visibility into internal security events, making it an essential layer of your cybersecurity strategy.
The Difference Between Host-Based IDS and Network-Based IDS (NIDS)
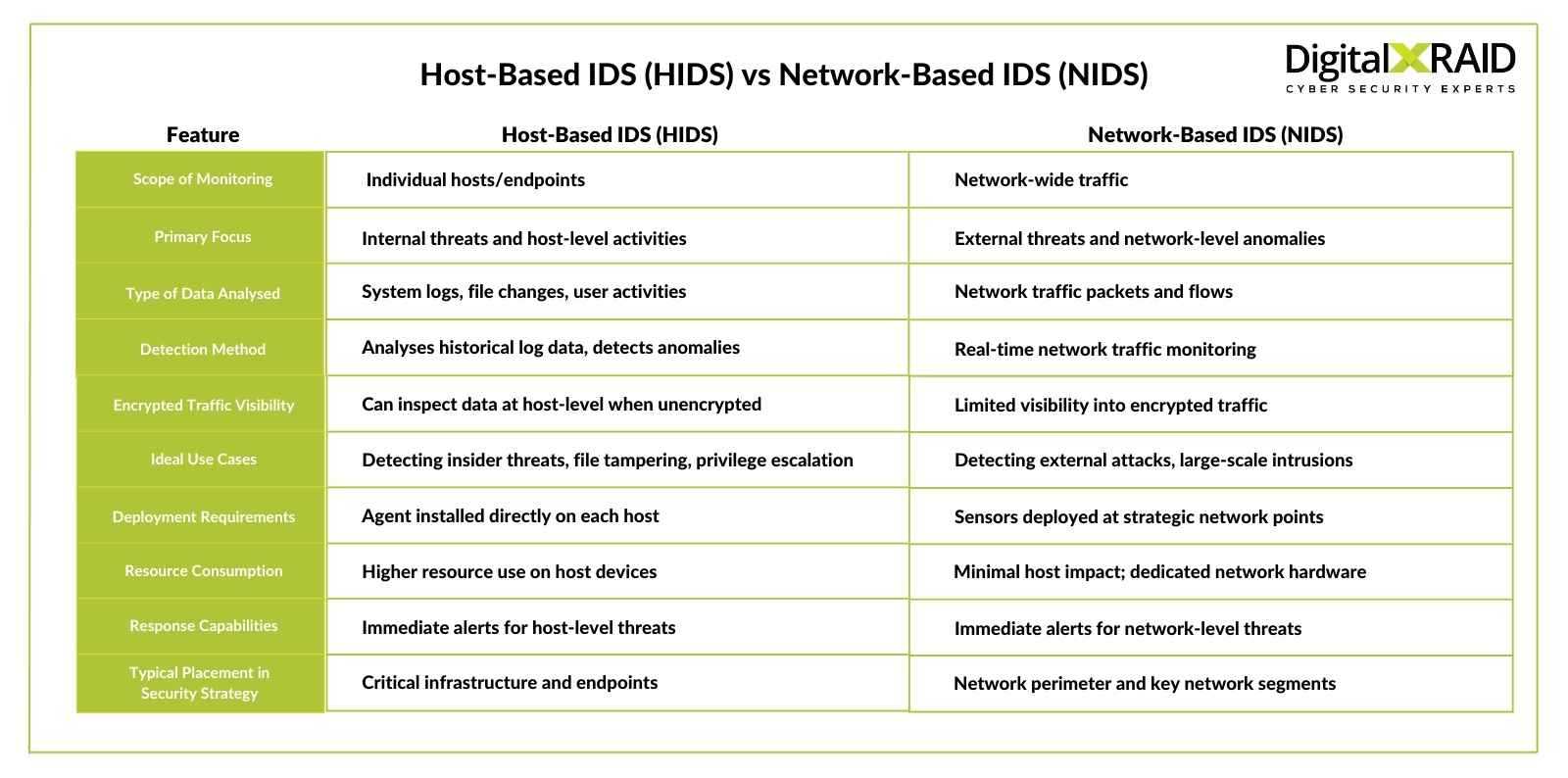
There are some key differences to understand when looking at Host-Based IDS vs Network-Based IDS (NIDS). HIDS protects against attacks at a host level, whereas NIDS protects the network against attacks.
While HIDS focuses on analysing historical log data and internal threats within endpoints, a network-based IDS (NIDS) monitors network traffic to detect external threats in real time.
Both have a place in a modern security strategy, operating in tandem for full protection of your network and your infrastructure. In today’s evolving threat landscape, the chance of intruders bypassing NIDS with new techniques or encryption is always high. This is where HIDS can inspect the data logs and identify the breach before it can cause serious damage.
How Host-Based Intrusion Detection Systems Work
Host-based intrusion detection systems use two methods to identify potential threats.
Monitoring System Logs for Suspicious Activity
HIDS continuously analyses system logs, tracking activities such as file changes, configuration modifications, and unusual user activity, to match it to a database of known threats. This log analysis is crucial for early detection of potential security breaches and provides forensic data essential for incident investigation and response.
Detecting Unauthorised Access & Malicious Processes
HIDS will alert security teams to unexpected login attempts, privilege escalations, and other malicious behaviours often missed by antivirus tools. By monitoring usage patterns, it can detect advanced persistent threats (APTs) and sophisticated malware attacks designed to bypass standard protections.
Responding to Security Incidents in Real-Time
Once any suspicious activity has been detected, HIDS immediately alerts your security team, whether that’s in-house or your managed SOC, enabling rapid real time response.
Automated response tooling can also be integrated, containing threats swiftly to prevent further damage. HIDS works seamlessly with Security Information and Event Management (SIEM) tools, enhancing overall threat visibility and management and log analysis.

Key Benefits of Implementing HIDS for Your Business
Host-Based Intrusion Detection offers a wide range of benefits, improving your security capabilities and posture:
Proactive Threat Detection & Risk Mitigation
Implementing HIDS enables your organisation to proactively detect threats, providing early alerts to suspicious activity and unusual patterns. As we’ve discussed, early detection of threats enables faster responses, which significantly reduces potential damage to your business, including operational disruption, and the financial or reputational impact of a cyber incident.
Strengthening Compliance with Security Regulations
Implementing a HIDS supports regulatory compliance efforts, providing comprehensive audit logs essential for meeting security regulation requirements. This visibility also enhances your business’s overall risk management capabilities.
Enhancing Endpoint Security Without Disrupting Business Operations
HIDS software runs quietly and efficiently in the background, ensuring that critical endpoint security does not compromise your system performance. Customisable alerts reduce false positive notifications, allowing your team or managed security service provider (MSSP) to focus only on genuine security issues.
Enhanced Detection of Insider Threats
One of the strengths of HIDS is its effectiveness in detecting insider threats. By closely monitoring endpoint activities, from file permission changes and unusual data access, to suspicious client-server interactions, HIDS identifies potentially malicious insider behaviours that network-based solutions might not be able to detect.
Ability to Inspect Encrypted Data
As mentioned, unlike network-based solutions that often struggle with encrypted traffic, a host-based IDS system can inspect data directly on the host where it is unencrypted in system memory. This provides visibility into threats hidden within encrypted traffic, enhancing your overall threat detection capabilities.
Comprehensive File Integrity Monitoring (FIM)
File Integrity Monitoring is one of the key strengths HIDS provides. HIDS continuously tracks access and modifications to critical files and alerts your security teams immediately to any unauthorised changes. This capability helps your business to quickly respond to potential tampering or compromise, meeting stringent requirements such as PCI-DSS 11.5 for payment card processing.
Lower Cost and Complexity
Deploying a host-based system typically requires less investment in new hardware or infrastructure compared with network-based systems. This makes HIDS an accessible, cost-effective security solution, lowering the barrier of entry for businesses looking to enhance security without significant budget or resource impacts.

Challenges & Limitations of Host-Based Intrusion Detection Systems
Just like any security software, HIDS alone isn’t a silver bullet solution.
Managing False Positives & Ensuring Accurate Threat Detection
A common challenge with HIDS is managing false positives, which can lead to alert fatigue among security teams. Fine tuning your HIDS configuration through expert management is essential to balance security and operational efficiency. If you don’t have this specialist skill in your internal teams, you can partner with an expert cybersecurity provider to ensure a successful deployment and management of your tooling.
Resource Usage & Performance Impact on Systems
HIDS solutions require adequate resources and regular updates to remain effective. Businesses should ensure systems have the capacity to accommodate HIDS without compromising performance.
The Need for Continuous Monitoring & Expert Management
Continuous monitoring by skilled cybersecurity professionals is critical for effectively managing a HIDS. Expert management of your cyber security measures ensures accurate threat detection and rapid response, maximising the value of your HIDS deployment.
Intrusion detection vs intrusion prevention
So what’s the difference between IDS and IPS? The key difference is that IDS analyses historical data and alerts to any suspicious activity. It doesn’t take action to block actions that have been deemed suspicious.
Intrusion Prevention Systems (IPS) monitor traffic flow and data in real-time and will actively block detected threats. IPS will block IP addresses and modify firewall rules to prevent an attacker from progressing through your infrastructure.
Both IDS and IPS play essential roles in any cybersecurity protection strategy. They are key components in building a defence in depth solution for your business.

How DigitalXRAID Helps Businesses Manage HIDS
DigitalXRAID’s Approach to HIDS Deployment & Configuration
At DigitalXRAID, our expert led approach involves comprehensive deployment strategies customised to your specific business needs. Our CREST accredited SOC analysts will manage the development of your design document, following industry and technical best practices.
At DigitalXRAID, we work on a rapid deployment model. Any systems that hold customer data or were operationally critical are prioritised to be protected immediately. This avoids any unnecessary complications and delays in deployment for your most important assets, preventing any delays to your systems and networks being protected.
How Our SOC Analysts Provide 24/7 Threat Monitoring
Our Security Operations Centre (SOC) service provides 24/7 monitoring, ensuring real time response to any potential threats. Through AI-powered tooling and continuous updates to detection rules, plus seamless integration with your infrastructure, DigitalXRAID provides unparalleled protection against even the most sophisticated attacks.
Case Study: How DigitalXRAID’s HIDS Protected MACS EU from Advanced Threats
DigitalXRAID successfully implemented a Managed SOC Service, including HIDS, for MACS EU, significantly enhancing their cyber security posture. The SOC service from DigitalXRAID has successfully detected and mitigated threats such as phishing attacks and unauthorised logins promptly, preventing potential breaches and protecting sensitive customer data. Learn more about MACS EU’s success story.
Conclusion: Why HIDS is Critical for Business Cyber Security
Implementing a robust Host-Based Intrusion Detection System (HIDS) is essential for businesses wanting to proactively address today’s complex cyber threat landscape.
By offering deep endpoint visibility, supporting rapid response capabilities, and compliance audit trails, HIDS forms a fundamental part of a strong risk management and cybersecurity strategy against attacks and internal threats. Its ability to inspect encrypted data and provide comprehensive file integrity monitoring significantly enhances threat detection capabilities.
By integrating HIDS into your security strategy, you’re actively strengthening your entire cybersecurity posture, safeguarding critical business assets, and significantly reducing the potential impacts of a breach.
HIDS provides you with significant advantages, however to achieve these fully, expert knowledge for deployment and management is required.
Next Steps: Secure Your Business with DigitalXRAID’s HIDS Services
Ready to strengthen your cyber security posture? Get in touch with DigitalXRAID today to discuss your business requirements and how we can take the headache away for your HIDS deployment.


