DigitalXRAID’s CREST certified cloud penetration testing services help to uncover misconfigurations, vulnerabilities, and compliance gaps across AWS, Azure, and GCP.
Cloud Pen Testing: More Than Just Perimeter Security
Migrating to the cloud doesn’t eliminate risk; it changes it. Misconfigured storage buckets, exposed APIs, and insecure identity setups are just some of the ways attackers can exploit cloud platforms.
Overlooking these cloud-specific risks can leave your businesses vulnerable to breaches, data leaks, and compliance violations.
Add multi-cloud environments (AWS, Azure, GCP) and shared responsibility models, and you’ve got a security challenge that demands specialist expertise.
Just some of the customers that trust DigitalXRAID to protect their business from cyber threats
Why Choose DigitalXRAID for Cloud Penetration Testing
When you need to be certain that your cloud infrastructure is secure, you need a partner with deep technical expertise and proven credibility across AWS, Azure, and GCP.

CREST and CHECK Certified Security Specialists
All testing is delivered by certified experts with hands-on experience across AWS, Azure, and GCP environments.
Aligned with OWASP, CIS, and Cloud Provider Standards
We follow globally recognised frameworks like OWASP Cloud Top 10 and CIS Benchmarks for accurate, standards-driven testing.
Threat Intelligence Led Testing for Real World Risk
Simulated attacks reflect the latest cloud threats, from misconfigured storage to exposed APIs.
Clear, Risk-Based Reporting
Get prioritised findings, plain English summaries for business stakeholders, and practical next steps tailored to your business.
Flexible Testing for Any Cloud Setup
We tailor every test to fit your architecture, whether public, private, hybrid, or multi-cloud.
Trusted by Security-Focused Enterprises
Organisations in finance, healthcare, critical infrastructure and beyond trust us to keep their cloud environments secure and compliant.

How Our Cloud Penetration Testing Works
Our CREST certified approach is designed to uncover misconfigurations, vulnerabilities, and weak access controls across your cloud infrastructure, from identity to deployment.

What’s Included in Our Cloud Penetration Testing Services
Our cloud penetration tests are tailored to the unique risks of AWS, Azure, and GCP environments, ensuring full-stack visibility, from misconfigurations to identity flaws.
- Cloud-specific threat modelling – Identify the most likely attack paths and risks across your chosen cloud platforms.
- IAM and privilege review – Assess misconfigured roles, excessive permissions, and privilege escalation risks.
- Storage and database testing – Detect exposed S3 buckets, storage blobs, and data leakage vectors.
- Firewall and segmentation analysis – Evaluate security group rules, VPC architecture, and internal segmentation.
- API and service layer testing – Probe for insecure endpoints, weak authentication, and misused services.
- Compliance-aligned configuration checks – Validate security posture against CIS, ISO 27001, and cloud best practices.
- Clear, actionable reporting – Includes both executive summaries and technical breakdowns for rapid remediation.
Need a Cloud-Specific Review?
Our range of cloud penetration testing services will make sure your cloud environments and apps remain secure
Our Cloud Penetration Testing Services
AWS
Cloud Security
Security Review
- Detect misconfigurations
- Check for vulnerabilities
- Check users and permissions
- Check for suspicious network traffic
- Properly configure any add-ons
- These are often overlooked when first setting up
- Eliminate any threats or issues
Azure
Cloud Security
Security Review
- Security policies on virtual machines
- Identify and access management
- Securely configured storage accounts
- SQL services on any SQL databases or servers
- Networking security groups
- Review of virtual machines
Office
365
Security Review
- Detect misconfigurations and review:
- Account and authentication policies
- Application permissions
- Data management policies
- Email security configurations
- Exchange online configurations
- Storage policies
- Auditing policies
- Mobile device management policies
Is Cloud Penetration Testing Right for Your Business?
Cloud environments come with unique risks, especially for growing businesses navigating compliance, rapid change, and shared responsibility models. Here’s how to know if this service fits your needs:
Using AWS, Azure or GCP: You need to validate the security of your cloud infrastructure.
Preparing for Compliance Audits: Pen testing helps meet ISO 27001, PCI-DSS and other requirements.
Post-Migration to the Cloud: Ensure no misconfigurations or gaps were introduced during migration.
Complex Cloud Access Controls: Test for privilege escalation risks across users and services.
Reliance on APIs or Third Parties: Check for vulnerabilities in cloud-based integrations and services.
Need for CREST Certified Assurance: You want a certified provider with proven cloud security expertise.
Speak to an Expert
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
“Feedback on the pen test from internal teams here was very positive and communication was responsive. We now have a much deeper visibility on our current security posture. We’re very happy with the reporting, which gave a thorough explanation of the findings and gave us clear solutions for remediation.”
Brigid Macdonald, Head of IT, Breast Cancer Now
What Are the Benefits of Cloud Penetration Testing?
Cloud penetration testing helps secure your cloud environment by identifying risks specific to cloud-hosted infrastructure, platforms, and services.

Uncover misconfigurations
Detect insecure storage, open ports, and exposed assets in AWS, Azure, or GCP.
Strengthen identity and access controls
Validate IAM, MFA, and privilege boundaries across cloud users and roles.
Ensure secure API usage
Identify exposed or vulnerable APIs in your cloud applications.
Protect data in transit and at rest
Test encryption practices and potential leakage of sensitive information.
Meet compliance requirements
Support ISO 27001, PCI-DSS, and cloud-specific frameworks with clear audit evidence.
Get actionable cloud security insights
Prioritised recommendations to reduce risk and guide secure cloud growth.

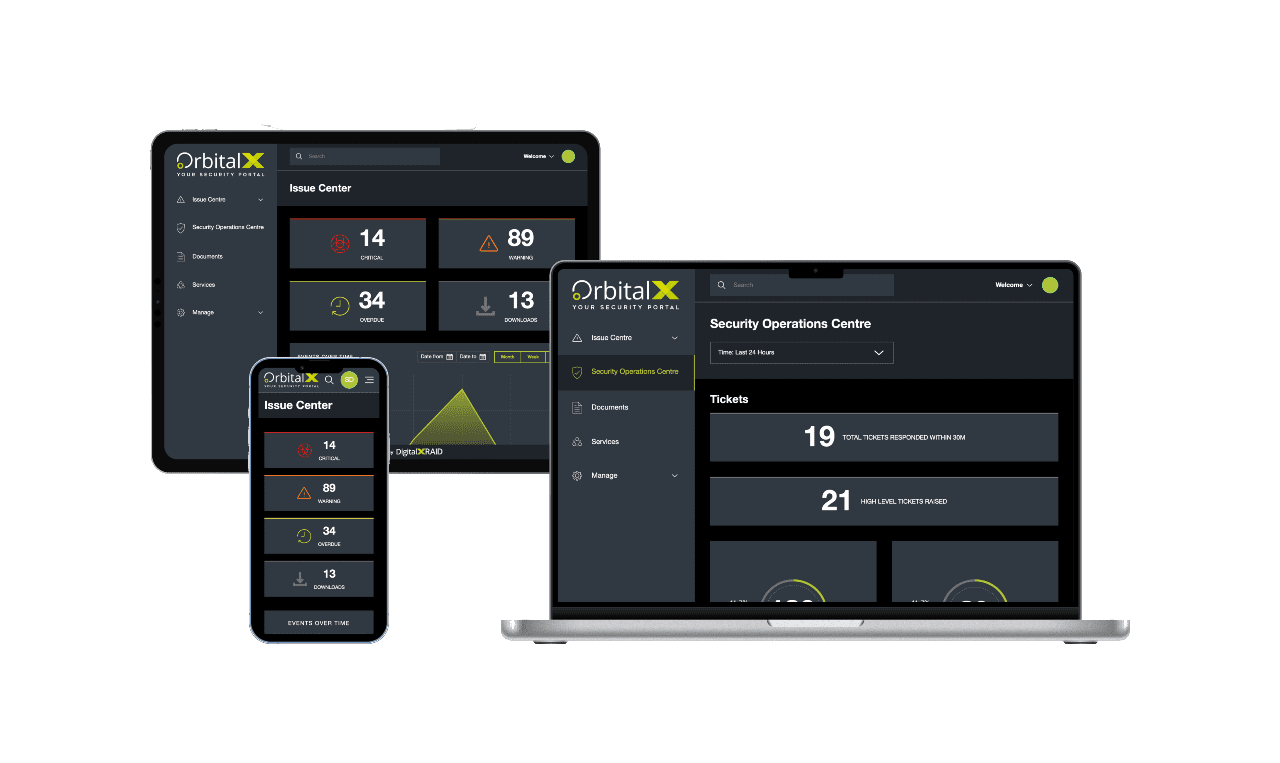
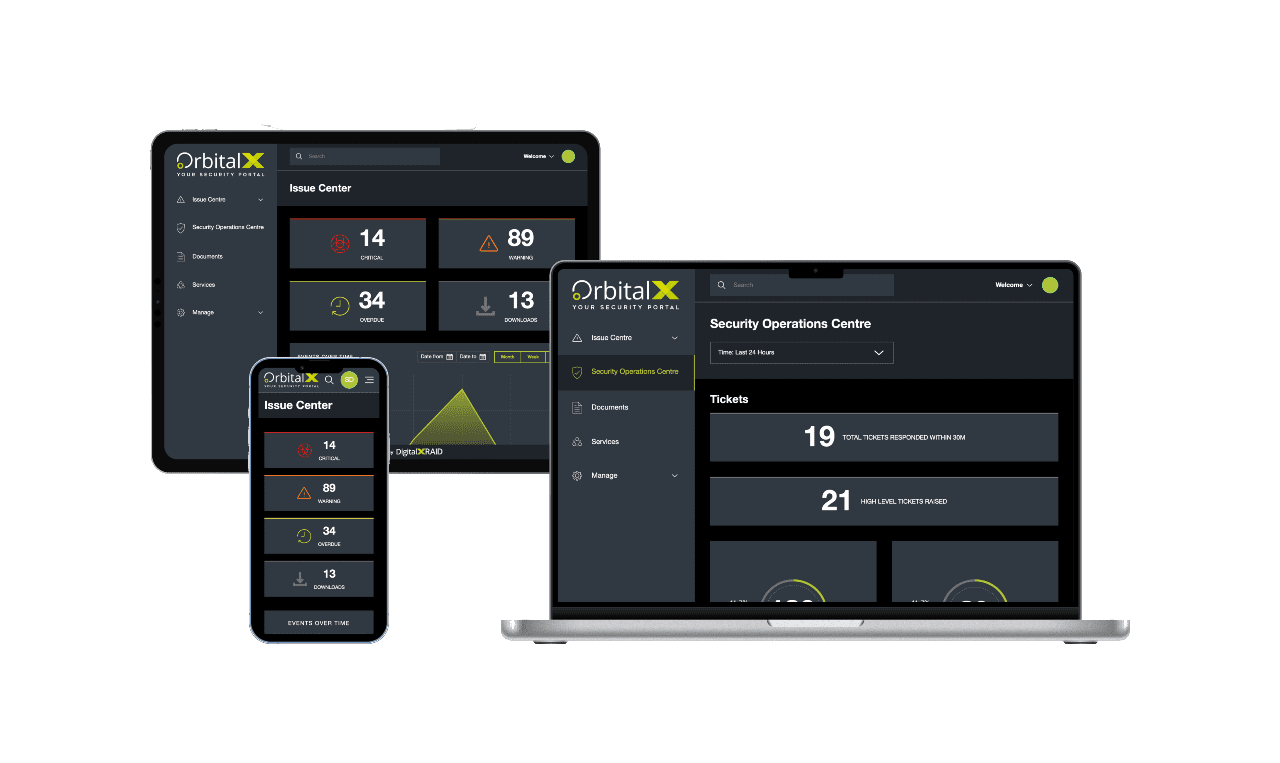
YOUR SECURITY PORTAL
Get full visibility of your cyber Security anytime, anywhere
OrbitalX – Your Security Portal
- Bridge the gap between vulnerability identification and issue remediation with timely, actionable insights
- Report the value of security programs to senior management with concise, specific reports, enhancing awareness and aiding in securing future budgets
- Build a comprehensive roadmap to full protection, incorporating defence in depth as your cyber security needs grow
Prevent Vulnerabilities
OrbitalX prevents vulnerabilities and other security issues from being overlooked, ensuring timely resolution and clear reporting on any missed issues or resource constraints.
Manage & Mitigate Risks Faster
- Gain greater visibility into your vulnerability status with your real-time vulnerability dashboard updates, categorised into Critical, High, Medium, and Low status.
- Prioritise and assign remediation tasks effortlessly based on the vulnerability type, ensuring prompt action and risk mitigation.
- Reduce your risk by tracking vulnerability resolution over time
Stay Ahead of Cyber Threat
- Take immediate action to remediate vulnerabilities before they can be exploited, keeping you one step ahead of hackers
- Communicate vulnerability status clearly across all business departments to ensure everyone is informed and risks are understood.
- Track and report vulnerability identification and remediation progress over time for a clear audit trail and live resolution status.
Enhanced Visibility
- OrbitalX provides enhanced visibility for a comprehensive view of your security and risk landscape
- Make informed business decisions based on real-time risk data to better protect your business from threats
- Move to a fully digital format for added value through linear granularity of your entire managed security service, with easy access to digital reports instead of cumbersome PDFs
Streamline Reporting
- Streamline cyber security reporting, moving away from outdated PDFs and emails to a dynamic, digital format.
- Quickly and accurately report on vulnerability resolution status, customising reports with relevant data for business stakeholders.
- Customise charts and diagrams for detailed and stakeholder-specific reporting.
Protect your business with cloud penetration testing
A security partner you can trust
Make sure you’re truly protected. As with all cybersecurity, penetration testing forms part of a robust security posture. We’ll work with you to identify and remedy weaknesses in your security before a malicious party exploits them and you fall victim to a cyberattack.
Discuss your cyber security options
Get in touch today to speak to an expert and secure your business, or call us on 0800 090 3734
Our other Pen Testing Services
FAQs: Cloud Penetration Testing
Yes, cloud providers secure the infrastructure, but you’re responsible for securing how it’s configured and used. Cloud pen testing helps validate your security posture and highlight risks you’re still accountable for.
Both standards expect regular security testing, and for cloud environments, that includes specific testing of cloud configurations, access controls, and hosted assets.
Traditional pen tests focus on on-premise assets, while cloud testing assesses misconfigurations, exposed APIs, identity management, and storage issues specific to AWS, Azure, GCP, and other platforms.
Yes, all testing is scoped carefully to avoid operational impact. We’ll work with you to define safe testing parameters and timings that align with your risk appetite.
At a minimum, annually or after any major configuration change. For businesses in regulated industries or those handling sensitive data, more frequent testing is recommended.
Protect Your Business & Your Reputation.
With a continued focus on security, you can rest assured that breaches and exploits won't be holding you back.