SIEM vs SOAR: What’s the Difference and Which One Does Your Business Need?
There is a constant pressure for organisations to detect and respond to attacks quickly, efficiently and in compliance with relevant industry regulations.
And we know it’s not easier said than done, with multiple acronyms all purporting to be the silver bullet tool against cyberattacks.
Your IT and security teams are likely already overwhelmed with alerts, understaffed, and faced with a dizzying amount of disparate tooling.
We’re looking at SIEM and SOAR, two of the most prominent acronyms in cyber security. We’ll analyse both SIEM vs SOAR, break down their key differences, and show you how the right combination can drastically reduce your risk, improve response times, and free your internal teams to focus on what really matters to grow your business.
Key Takeaways
- SIEM focuses on detecting cyber threats through log aggregation and analysis, while SOAR automates and orchestrates incident response workflows.
- SIEM offers real-time visibility across systems; SOAR acts on alerts to reduce response times and manual workloads.
- Together, SIEM and SOAR provide comprehensive threat detection and automated remediation—essential for modern, scalable cyber defence.
- Businesses with alert fatigue, limited internal resources, or compliance pressures benefit most from combining both technologies.
- DigitalXRAID’s Managed SOC integrates SIEM and SOAR with 24/7 expert monitoring, bespoke playbooks, and proactive threat intelligence for maximum protection.

What Is SIEM?
Security Information and Event Management (SIEM) is the central foundation of many companies’ security monitoring strategies.
If your business needs to understand what’s happening across its digital estate in real-time or comply with industry regulations around resilience and cyber security, SIEM should be a central part of its security protection measures.
Definition and Core Functionality
SIEMs collect, aggregate, and analyse log data from a wide variety of systems, such as firewalls, servers, cloud platforms, applications, endpoints, and more.
The data is then normalised and correlated to uncover patterns that might indicate malicious activity within your infrastructure.
At its core, SIEM combines:
Security Information Management (SIM): Long-term storage and analysis of security logs
Security Event Management (SEM): Real-time monitoring, alerting, and dashboarding
SIEM is your security telemetry platform that surfaces issues that might otherwise go undetected if logs and events were viewed in isolation.
How SIEM Supports Security Operations
SIEM helps IT and security teams to identify threats, such as brute force attacks, unauthorised account access, data exfiltration, and malware, by:
- Providing unified visibility across your environment
- Correlating disparate events to reveal hidden threats
- Delivering alerts in real-time, enabling fast response
- Supporting compliance with regulations such as DORA, NIS2 and the Cyber Resilience Act (CRA)
Common Limitations of SIEM Tools
While SIEM is an essential tool in many scenarios, it’s not a silver bullet for all cyber protection and does have a few limitations in certain use cases:
High False Positives: Without expert deployment and tuning, your SIEM could overwhelm your teams with false alerts noise
Manual Analysis: SIEM has limited capabilities around real-time time response. Analysts still have to manually investigate, validate, and act on all alerts flagged by the tool
Resource Intensive: Managing, updating, and scaling a SIEM takes time, money, and specialist expertise

What Is SOAR?
Security Orchestration, Automation and Response (SOAR) extends the value of foundational SIEM by enabling security teams to respond faster and smarter.
Core Capabilities and Benefits
SOAR platforms are designed to streamline and automate key aspects of incident response. They combine:
Automation: SOAR functionality will execute predefined incident response playbooks for common threats, such as isolating a device or disabling an account
Orchestration: SOAR can integrate with other advanced tools and technology to enable seamless workflows and additional functionality
Case Management: You can track, assign, and collaborate across teams on your cyber incident investigations from a single interface
SOAR essentially takes the alerts generated by your SIEM and takes action on them according to predefined workflows at speed and scale.
How SOAR Works with SIEM
SOAR and SIEM serve different but complementary purposes. Think of SOAR as picking up where your SIEM ends to act as a response engine. While a SIEM managed service detects and alerts on suspicious activity, SOAR then picks up the baton.
SOAR capabilities will:
- Enrich alerts with context, for example, pulling in threat intelligence, user behaviour data and analytics, or asset value
- Automate initial incident investigation steps for faster triage
- Execute response actions such as quarantining a host or opening a ticket for security analysts to investigate
SOAR ultimately reduces the time that security analysts spend responding to incidents, jumping between tools and performing repetitive tasks manually.
Automation in Threat Response
Common tasks SOAR can automate include:
- Phishing email analysis and user notification
- Malware triage and isolation
- User behaviour anomaly follow-up
- Vulnerability remediation workflows
By automating a significant portion of the manual response workload, SOAR enables your security analysts to focus on higher-value tasks and decision-making.

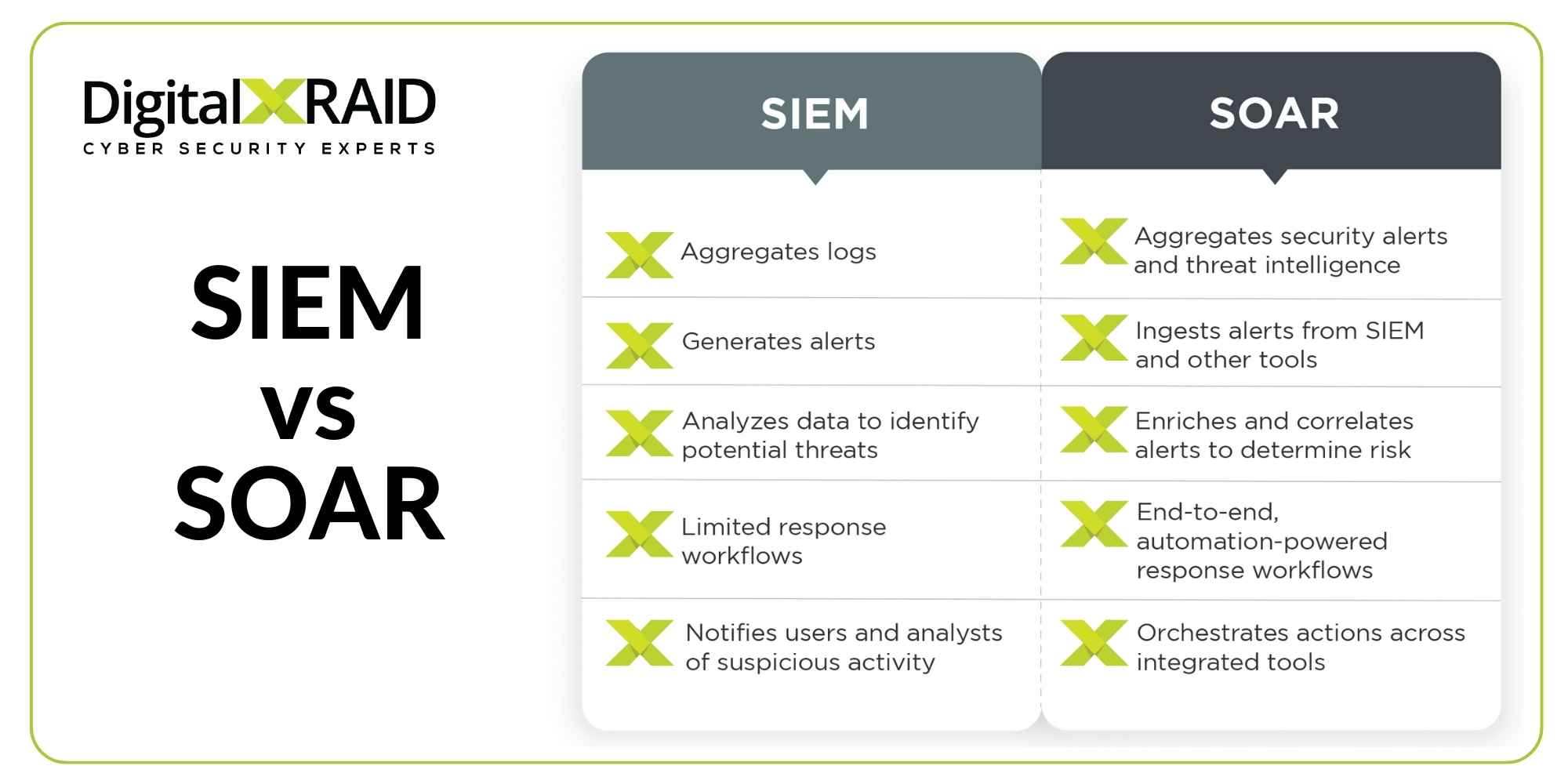
SIEM vs SOAR: Key Differences Explained
While SIEM and SOAR are complementary, they serve distinct purposes in modern cyber security strategies.
| Feature | SIEM | SOAR |
| Purpose | Threat detection | Incident response |
| Focus | Log aggregation, correlation, alerting | Workflow automation, orchestration, response |
| Primary User | Security analysts (monitoring) | Incident responders (action) |
| Dependency | Needs manual response | Automates responses |
| Data Sources | Firewalls, servers, cloud, apps | SIEM, EDR, threat intel, ticketing systems |
Purpose
At a high level, SIEM is about identifying potentially malicious events by sifting through data logs and events to highlight potential threats.
SOAR then takes those alerts and, through automation, will manage the response. That could also include being guided by human oversight.
SIEM spots the needles in the haystacks. SOAR helps you to know what to do once they’ve been found, and automatically actions much of it for you.
Focus
SIEM platforms are built around visibility and data centralisation. They gather vast amounts of information, correlate it, and try to spot signs of suspicious behaviour.
SOAR platforms focus on process optimisation and how quickly, consistently, and effectively they enable your team to act once an alert is raised.
Primary User
SIEM is often used by security operations monitoring teams and SOC analysts to detect potential issues.
These are frequently called your frontline defenders. SOAR then supports your responders, from analysts and incident managers to SOC engineers responsible for taking action.
Dependency
One of the main differences is how the tools function within a real-world Security Operations Centre (SOC).
SIEM still heavily relies on human analysis and manual processes. If your analysts are overloaded or inexperienced, cyber threats can slip through and cause damage.
SOAR reduces this burden on analysts by automatically handling repetitive tasks, ensuring consistency in response and speeding up Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) times.
Data Sources
SIEM focuses on ingesting and analysing data logs from across your network, applications and systems.
SOAR takes in alerts generated from systems like SIEM, EDR (Endpoint Detection and Response), and threat intelligence feeds, and then acts on that data. The integration layer is crucial here. If your tools aren’t properly deployed and integrated, automation becomes impossible.
For example, a SIEM might detect multiple failed logins followed by a successful one from an unusual location, sending an alert flagging this as suspicious. Without SOAR, your security analysts have to investigate and take manual action.
With SOAR capabilities, that alert could automatically trigger a preprogrammed playbook to enrich the data, such as confirming device and user details, notifying the security team, and even disabling the account or isolating the device if necessary.
In a threat landscape where seconds matter and security teams are overstretched, automating the right response, at the right time, can be the difference between an incident and a successful breach.
Detection vs Orchestration
SIEM is the radar that tells you something is wrong. SOAR becomes your automated analyst, taking the alert and acting on it to prevent a breach.
Data Aggregation vs Response Automation
SIEM pulls together vast volumes of data to identify potential threats. SOAR takes those outputs and provides automated and consistent workflow responses.
Tools vs Workflow Optimisation
SIEM gives you visibility of data and anomalies and provides alerts. SOAR gives you structured cyber incident playbooks that make your response process repeatable, efficient, and measurable.
Analyst Dependency vs Analyst Enablement
SIEM often increases workload for your security analysts through false positive alert generation. SOAR reduces strain on security teams by automating routine tasks, and helping teams to stay focused on real threats rather than reacting to the noise.
Do You Need SIEM, SOAR or Both?
This is the crux of the conversation. While SIEM and SOAR are different tools and are often discussed as separate solutions, the reality is they’re most powerful when deployed together, especially when operated by a highly skilled team with the expertise to maximise their potential.
Use Cases Where SIEM Alone Falls Short
- Analysts overwhelmed by daily alert volumes
- Threats detected too late to contain effectively
- Delayed compliance reporting or missed SLA response times
SIEM delivers broad visibility across your environment, allowing your security team to monitor logs, correlate events, and detect potentially malicious activity.
But without SOAR, you’re left with a high volume of alerts that may be false positives, and limited resources to act on them.
SIEM in isolation could present challenges such as:
Analyst overload: Large organisations are dealing with thousands of security alerts every day and night. Even a well-tuned SIEM can generate noise when first deployed and needs constant management and updates. Without automation, alert triage can become a bottleneck.
Late-stage detection: SIEMs can detect suspicious patterns, but if an alert sits in a queue or requires manual validation, response delays could mean a breach could go unchecked and become more serious. Every second counts in detection and response times.
Compliance overheads: Demonstrating audit-ready incident response reports can be difficult with SIEM alone. Manual tracking and inconsistent processes increase the risk of gaps, especially under standards such as DORA and NIS2 that now mandate the details and timeframes for incident response.
When SOAR Adds Strategic Value
SOAR is ideal for:
- Security teams struggling with manual triage
- Smaller teams managing growing environments
- Organisations looking to reduce MTTR and scale their response
SOAR becomes a must-have if you’re trying to scale your incident detection into an effective response. Its value is most obvious in organisations where:
Teams are thinly stretched: This is most common in SMEs and mid-market firms that don’t have the resources to operate a 24/7 SOC in-house.
Alerts are piling up: If your team can see the list of alerts, knows what needs to be done, but can’t triage them fast enough, then SOAR is essential.
Repeatable tasks dominate your day: Whether it’s triaging, phishing emails, host isolation, or credential resets, SOAR automates these workflows to improve both the consistency and speed of response.
From a technical angle, SOAR ingests alerts from your SIEM, validates them using threat intelligence platforms (TIPs), enriches the context, and then triggers structured playbooks across EDR, firewalls, and ticketing systems, all without any manual analyst intervention.
How Combining Both Improves Efficiency
Together, SIEM and SOAR provide:
- Real-time detection (SIEM)
- Automated response (SOAR)
- Operational efficiency
- Improved compliance evidence trails
- Fewer missed alerts and faster containment
The real value of SIEM vs SOAR is really looking at SIEM and SOAR together. Deploying and managing both SIEM and SOAR internally is by no means a trivial task, and many companies won’t have the internal resources to manage this.
SIEM and SOAR deployments require:
- Deep technical expertise across multiple platforms
- Constant tuning of detection logic and automation rules
- 24/7 coverage for alerts, response, and escalation
- Integration with threat intel, vulnerability scanners, and ticketing tools
That’s where a Managed SOC Service provider like DigitalXRAID can deliver you efficiency and the maximum value for your solution. We’ll operate your SOC service intelligently, as an extension of your team and part of your broader cyber defence strategy.
At DigitalXRAID, we provide you with a tailored service that includes:
- Proven incident response playbooks tailored and built according to your specific industry and threat landscape
- Highly skilled and certified analysts who will advise you on the best tools for your requirements and adapt that tooling to your specific environment
- Ongoing tuning to reduce false positives and increase the speed and precision of your security monitoring and response
- Threat intelligence integration that draws from the most comprehensive threat data in the world, mapping intelligence to your industry-specific risks and geographical risks

The Business Impact of SIEM and SOAR
Let’s move beyond the technology and look at the capabilities and benefits of these technologies working together. Here’s why these tools matter to your business:
Reducing Alert Fatigue and Manual Work
By automating investigation steps and enriching alerts, SOAR helps you to eliminate the noise of false positive alerts, prioritise the threats that really matter for investigation, and reduce the time that your teams waste on following up on false alerts.
Improving Incident Response Time
Faster response directly equals fewer successful breaches and damaging outcomes. Automating tasks such as isolating devices, notifying users, or gathering evidence means that security teams can act quickly and decisively.
Enabling Proactive Cyber Security
With both SIEM and SOAR tools in place, your teams or SOC service can hunt for threats using historical data for context and predictability.
SOAR will enable you to automate tasks such as workflows for patching, which will avoid any missed updates, creating vulnerabilities. Your cyber resilience will also be improved through repeatable and tested responses.
These capabilities aren’t just beneficial for your team or your SOC service, they make sure you’re always audit-ready and have the most cost-effective solution for your risk mitigation.

Managed SOC with SIEM and SOAR: A Smarter Approach
The reality for many organisations? You simply don’t have the time or team size to manage SIEM and SOAR effectively in-house.
This is where a Managed SOC provider like DigitalXRAID becomes essential.
Why Outsourcing Beats Building In-House
Outsourcing provides:
- 24/7 coverage without hiring an in-house shift team
- Access to threat intelligence, response playbooks, and expertise
- Faster time to value (deployment, tuning, response)
- Simplified compliance audits
It’s not just a cost decision. It’s a performance and peace-of-mind decision.
DigitalXRAID’s 24/7 SOC and Threat Intelligence Integration
Our UK-based fully managed SOC service operates around the clock, working with leading technology providers such as Microsoft to provide:
- Managed SIEM for real-time visibility
- SOAR automation to accelerate response
- Endpoint Detection & Response (EDR)
- IDS and IPS
- Extended Detection & Response (XDR)
- Threat intelligence feeds to detect emerging attacks
- Dark Web Monitoring
- A dedicated team of cyber analysts who investigate, triage, and respond to threats
We don’t just give you the tools. We provide a bespoke service to protect your business now and into the future.
Certifications, Compliance, and UK-Specific Expertise
DigitalXRAID is one of the first providers globally to be both CREST and NCSC accredited for its Security Operations Centre (SOC) service, ISO 27001, 20000 and 9001 certified, and fully aligned to UK compliance frameworks.
We understand your industry’s threat landscape, and we speak your language, whether at a technical level or to convey the ROI of your cyber programmes to senior stakeholders.
Final Thoughts: Making the Right Choice for Your Organisation
SIEM and SOAR aren’t competitors, they’re allies in the fight against cybercriminals. When combined, these tools will provide you with unparalleled visibility, faster incident response, and improved resilience.
But the best results don’t come from technology alone. They come from expert management, 24/7 operations, and actionable insights. That’s what DigitalXRAID’s Managed SOC Service can deliver you: the protection you need.
Ready to strengthen your security operations with an expert-led and proactive managed service? Get in touch with the team today.


