GDPR Breach Definition, Examples and How to Respond
Understanding when and how a GDPR breach occurs is absolutely critical for you as an IT Director, CISO or senior security decision maker in this increasing cyber threat landscape. The UK Cyber Security Breaches Survey 2025 found that 67% of mid-size organisations experienced a cyber security breach or attack in the past 12 months. This figure is similar to the previous year’s survey, which showed 70% of medium sized businesses were affected.
A single cyber security incident can ripple through your organisation and wider supply chain, as we saw with notorious attacks on businesses such as M&S, Co-op, Harrods and Jaguar Land Rover. These attacks bring with them regulatory scrutiny, reputational damage, financial loss, and eroded customer trust.
In this guide, we’ll define exactly what constitutes a GDPR breach, walk you through the common causes and types of breaches, outline your reporting obligations, and show how partnering with a cyber security service provider can significantly reduce your risk exposure. By the end, you’ll have a clear roadmap of the practical steps you should be taking towards a more secure future.
Key Takeaways
- The definition of a personal data breach under UK GDPR is a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to personal data.
- Not all security incidents trigger a breach-reporting obligation; the key test is whether there is a risk to individuals’ rights and freedoms.
- When there is a reporting obligation, you must notify the Information Commissioner’s Office (ICO) without undue delay, and at the latest 72 hours after you become aware of a notifiable breach.
- You must also assess whether affected individuals should be told and document all of your actions, regardless of whether you notify the ICO.
- Preventative and monitoring controls (such as staff training, pen testing and a managed SOC) make a real difference and may reduce regulatory and financial exposure.
- You must ensure that your organisation’s preparedness for a breach is not just an IT issue. It involves people, process and technology, aligned with a wider compliance and risk management framework.

What Constitutes a Data Breach When it Comes to GDPR?
The EU’s General Data Protection Regulation (GDPR) is built around seven key data protection principles.
These seven principles guide how personal data must be handled:
- Lawfulness, fairness, and transparency: Data processing needs a legal basis, should align with data subjects’ expectations, and be clearly communicated.
- Purpose limitation: Data must be collected for specific, legitimate purposes and not used in incompatible ways.
- Data minimisation: Only necessary data for the intended purpose should be collected.
- Accuracy: Personal data must be accurate and updated, with inaccurate data corrected or erased promptly.
- Storage limitation: Data should not be kept longer than needed to identify data subjects for the specified purposes.
- Integrity and confidentiality (security): Requires secure processing to protect against unauthorised or unlawful use, and accidental loss or damage.
- Accountability: Data controllers must be able to show compliance with these principles.
So, what constitutes a data breach, and what are the most common types of breaches you’re likely to face? And what does the ICO expect when evaluating whether a breach is reportable?
Definition of a personal data breach under GDPR
As defined by the ICO: “A personal data breach means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to personal data.”
In other words, if personal data has been lost, corrupted, accessed, or made unavailable when it ought to have been available, you may have a breach.
“Accidental or unlawful” covers a wide spectrum of scenarios. For example: a mis-addressed email, a lost USB drive, an unauthorised third-party login, or a configuration error on a cloud storage bucket. The key is not the scenario but the impact on the personal data’s confidentiality, integrity or availability, the three core principles of information security.
Common types of GDPR breaches
From our experience working with UK organisations and protecting mid-to-large enterprise environments, the most frequent causes of GDPR breaches you’ll want to guard against include:
- Mis-addressed or incorrectly forwarded emails containing personal data.
- Misconfigured cloud storage buckets or file shares that expose data publicly.
- Loss or theft of portable devices (laptops, USB sticks, smartphones) containing unprotected personal data.
- Internal human error, which can include printing sensitive data and failing to secure it, or accidental deletion with no recovery control.
- Credential compromise (an external attacker gaining unauthorised access) and exfiltration of personal data.
- Denial or loss of access to personal data (availability loss) that has a material adverse effect on individuals.
For regulated sectors such as financial services, healthcare and the public sector, the consequences of GDPR data breaches are much higher and tend to escalate more quickly because there is higher sensitivity data, increased regulatory scrutiny, and contractual and third-party dependencies that they must adhere to.

GDPR Breach vs Non-Breach Scenarios
| Scenario | GDPR Breach? | Why / Why Not? | Reporting Requirement |
| An email containing personal data was sent to the wrong external recipient | Yes (usually) | Unauthorised disclosure of personal data. Risk depends on sensitivity and the recipient. | Must assess risk. If likely to cause harm, report to the ICO within 72 hours and potentially notify individuals. |
| Internal email sent to the wrong colleague inside the organisation | Sometimes | If the colleague has appropriate access or confidentiality obligations, the risk may be low. | Generally, no ICO notification, but must record internally. |
| Lost laptop with unencrypted personal data | Yes | Loss of confidentiality and potentially high risk to individuals’ rights. | Often reportable to ICO and affected individuals. |
| Lost laptop fully encrypted to current standards | No (in most cases) | Encryption reduces risk. No meaningful access to personal data. | No ICO notification, but record the incident internally. |
| Misconfigured cloud bucket exposing personal data publicly | Yes | Unauthorised access is possible even if you have no evidence of misuse. | Reportable to ICO if risk to individuals exists. |
| Temporary outage where personal data is inaccessible for an hour | Sometimes | GDPR includes loss of availability. If service disruption could impact individuals significantly, it may be a breach. | Usually recorded internally unless high risk. |
| Ransomware attack encrypting personal data without evidence of exfiltration | Yes (usually) | Encryption by an attacker constitutes a loss of availability and control. ICO typically treats ransomware as a personal data breach. | Assess and likely report to ICO within 72 hours. |
| Ransomware attack on systems holding only anonymised data | No | If data is fully anonymised and cannot identify individuals, GDPR does not apply. | No reporting requirements. |
| Staff member viewing personal data they are authorised to access | No | No breach. Data processed within expected permissions. | No action required. |
| Staff member accessing personal data out of curiosity (no business need) | Yes | Unauthorised internal access breaches integrity and confidentiality, even if data does not leave the organisation. | Assess and may need to report depending on risk. |
| Third-party supplier suffers a cyberattack affecting your customers’ personal data | Yes | Controller remains responsible for personal data processed by suppliers. | Notify ICO if high risk, and investigate contractual obligations. |
| Personal data was accidentally deleted but quickly restored from backup | Sometimes | If data is restored with no impact on individuals, it may be low-risk. | Usually not reportable, but record internally. |
| Personal data changed or corrupted due to a system error | Yes | GDPR includes alteration of personal data as a breach if it affects rights or accurate processing. | Report if individuals could be harmed (e.g. medical or financial data). |
What the ICO says about reportable breaches
According to ICO guidance, you must assess each incident to decide whether or not you need to notify.
Key points to consider:
- You become ‘aware of a breach’ when you have enough information to know a breach has occurred or when you ought to have known a breach has occurred. Reporting is required at the latest 72 hours after you become aware.
- You must notify if the breach is likely to result in a risk to the rights and freedoms of natural persons, not just if there is a corporate inconvenience. Examples of risk include identity theft, fraud, discrimination, reputational damage, financial loss, or other significant negative outcomes.
- Even if you decide not to notify the ICO because the risk is minimal, you must document your reasoning and keep records of the breach’s nature, impact and mitigation steps.
Having a process and toolkit for rapid assessment is vital. Aligning with ISO 27001 can guide your operational policies for a breach of data protection and security measures. If you delay and can’t justify your reasoning for the delay, you risk regulatory enforcement, such as fines.

What’s the Difference Between a GDPR Breach and a Data Protection Breach?
There is frequent confusion between phrases such as “GDPR breach”, “data protection breach” and “personal data breach”.
Let’s clear that up here by explaining what a GDPR breach is, what a data protection breach is, and the differences between them.
Legal terminology vs real world use
In strict terms:
- A “GDPR breach” refers to the legal definition of a data protection breach under the rules of GDPR.
- “Data protection breach” is a broader, more informal term used in real world business or media, and may include incidents that do not strictly meet the GDPR breach test such as non-personal data or policy violations.
- “Personal data breach” is a legal term used in multiple data-protection laws, not just the GDPR. While the GDPR popularised the definition, many other privacy or data-protection frameworks use the same or a very similar term.
Implications for businesses and breach reporting
If you treat every minor policy slip up as a GDPR breach, you risk over reporting, resigning your organisation to notification fatigue and regulatory noise.
Conversely, if you under-report because you misunderstand the definition of a data protection breach, you risk failing to notify when you should. The fines and reputational impact of failing to notify can be serious.
The language you use around data breaches and protection, both internally and externally, matters. Your processes should map to legal definitions, and your internal communications should align with how the regulator interprets those definitions.
Examples of GDPR Breaches
Real world examples of GDPR breaches can help you and your team to recognise common risks and patterns. In this section, we’ll walk through some high profile examples and the consequences and lessons learned from these well-publicised breaches.
Real world examples
Example 1: Police Service of Northern Ireland (PSNI) – Disclosure via FOI and significant fine
How the breach occurred
The Police Service of Northern Ireland (PSNI) accidentally published personal data of around 9,500 officers and staff in response to a freedom of information (FOI) request.
The exposed data included names, initials, ranks, work locations and departmental details. The ICO found that the PSNI had failed to implement appropriate technical and organisational measures under the UK GDPR.
Outcome
The regulator initially calculated a £5.6 million fine, but after taking into account the PSNI’s public sector context, the actual fine was set at £750,000.
The ICO’s findings emphasised that this was not a “minor” disclosure. Given the security risk in Northern Ireland, the consequences for officers and their families could have been “the most severe imaginable”.
Lessons learned
- Even responses to Freedom of Information (FOI) requests can trigger serious breach events.
- The root cause was organisational: inadequate processes and controls for handling sensitive staff data.
- Senior decision makers should ensure that the full data lifecycle, even public request responses, are covered by data protection risk assessments and monitoring.
- Ask yourself and your teams: If someone requested data lists from us, could we inadvertently send sensitive staff data without guardrails?
Example 2: British Airways (BA) – Customer data theft via third-party breach & inadequate security controls
How the breach occurred
BA’s website systems were compromised via a third-party supplier’s credentials, then malicious code redirected customers to a fraudulent website, collecting payment card data and personal details, including names and addresses of around 400,000 customers.
The attacker exploited weak security controls such as unpatched scripts, administrator privileges, and insufficient oversight of third-party access.
Outcome
The Information Commissioner’s Office (ICO) originally proposed a fine of ~£183 m, which equalled around 1.5% of BA’s global turnover, but ultimately the fine was reduced to £20 million in 2020.
The event also triggered the largest ever UK group action claim of its kind, with compensation claims from thousands of BA customers.
Lessons learned
- Third-party access is a major vector for personal data breaches. Your vendor/supplier security and access management must be robust.
- Attack vectors often exploit weak points in your supply chain rather than direct hacking by outside attackers.
- Detection and response delay increases risk and regulatory exposure. Review your vendor risk, patching regimes, logging of privileged administrative access, and triage of third-party audits.
- When you can show you had “appropriate technical and organisational measures” in place, regulators may be more lenient, so you should start to build evidence of this proactively.

Example 3: Blackbaud (affecting UK Universities) – Ransomware/third-party compromise in the education sector
How the breach occurred
Blackbaud, an international cloud services provider to universities, charities, and non-profits, was hit by a ransomware attack. The attackers stole data, and unfortunately, Blackbaud paid a ransom to attempt to recover the lost data and operations.
UK universities were among those most affected. Although Blackbaud is US-based, the breach impacted UK organisations’ personal data by virtue of the supplier relationship.
Outcome
While individual UK fines or regulatory outcomes for each institution were not publicly as significant as others, the breach resulted in legal claims and reputational damage.
The broader lesson for UK organisations was that they’re exposed whenever they have a supplier that is compromised, and they may bear regulatory and contractual responsibilities.
Lessons learned
- Supplier-side incidents are just as dangerous as your own infrastructure breaches. You must treat your third parties as potential breach vectors when considering your cyber security posture.
- The education sector, and any sector with large personal data volumes, must assume a breach will occur and have response and monitoring layered accordingly.
- Ensure your supplier contracts demand prompt notification, audit rights, breach response collaboration, and logging/monitoring visibility.
In each case, the incident aligns with the definition of “accidental or unlawful access/disclosure/availability loss” and triggered a regulatory or reputational consequence.
From your perspective, you should ask yourself: If this happened to us, would we detect it? Could we contain it in time? Do our processes trigger appropriately?
Real world potential scenarios
- According to the ICO’s “Personal data breach examples”, mis-sending data to an incorrect recipient is explicitly cited as one of the key scenarios to mitigate against.
- Another typical scenario is when cloud services are misconfigured and left publicly accessible, resulting in unauthorised access or disclosure of personal data.
Consequences: fines, reputation, legal action
Consequences for a GDPR breach in the UK can include:
- Regulatory fines – the ICO can impose significant financial penalties under the UK GDPR regime.
- Legal claims and compensation by individuals (data subject claims).
- Reputational damage and loss of trust from customers and partners.
- The operational cost of investigation, remediation, PR, and incident management.
- Contractual and liability issues with third parties who relied on your security assurances.
Navigating the commercial impact is very much a board-level concern and should be proactively addressed. For example, if you can’t provide evidence that you had technical controls, training, monitoring, and incident response in place, the regulatory outcome is likely to be heavier.
Lessons learned from past incidents
From the cases above and our work with clients, we can highlight a few practical takeaways you can implement immediately:
- Don’t assume a small incident is low risk without a documented assessment. The ICO will expect you to have performed this.
- Ensure you have mechanisms for detection, containment and investigation, not just prevention. Breaches are now inevitable for most organisations, so readiness matters more than ever.
- Staff awareness and process maturity are just as important as your technical controls. Many breaches begin as human error or misconfiguration.
- If regulators ask how you detected and responded to an attack, you need to be able to show your policy, logs, decision making, and audit trail.
- Use third-party risk controls, as many breaches stem from a supplier or service provider. Your vendor contracts, monitoring, and assurance must be strong and well documented.

When Must You Report a GDPR Breach – and to Whom?
Let’s look at your obligations clearly: when you must report, who you report to, and the timelines you must meet.
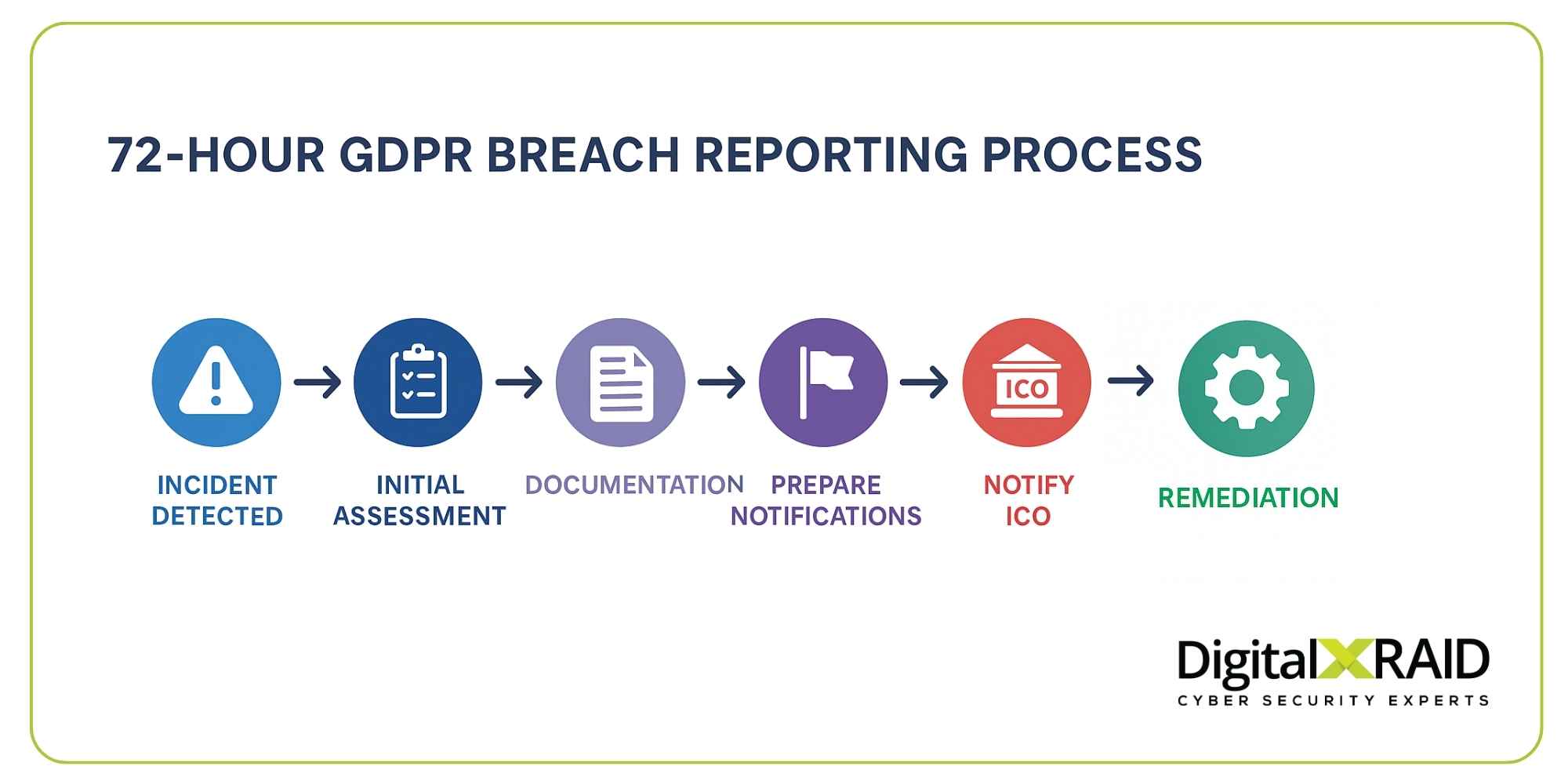
72 hour rule and ICO notification
If your assessment determines that a personal data breach is likely to result in a risk to individuals’ rights and freedoms, then you must notify the ICO without delay, and at the latest 72 hours after you become aware of the breach.
If you miss the 72 hour deadline, you must still notify the ICO and provide reasons for the delay.
The “become aware” point can be ambiguous, so trigger your incident response plan as soon as there is a reasonable indication of a breach.
When to notify data subjects
Not only must you notify the ICO, but in some cases you must also notify the affected individuals (data subjects).
You must do this where the breach is likely to result in a high risk to their rights and freedoms, for example, a breach of special category data, large numbers of individuals, or significant potential harm such as identity theft or fraud.
When notifying individuals, you must explain in clear language: The nature of the breach, what you are doing about it, and what they can do themselves. Failure to do so can increase your regulatory and reputational consequences.
Who is responsible – controller vs processor?
In GDPR terms:
- The “data controller” determines the purposes and means of processing personal data.
- The “data processor” processes personal data on behalf of the controller.
In a breach scenario, the controller remains primarily responsible for breach assessment and, where applicable, notification, although processors have key obligations too, for example, to notify the controller without undue delay.
Contracts with your processors must include clear breach notification clauses, evidence of monitoring, and assurance that processors meet your security expectations.
How to Respond to a GDPR Breach Effectively
Once a breach has occurred, the speed and completeness of your response matters, not just to mitigate regulatory action but also to protect your reputation. Here’s a practical breakdown of how you should respond to a GDPR breach:
Immediate steps to take after a breach
When you detect (or reasonably suspect) a breach, you should act immediately to contain and assess the damage.
The initial steps you should follow include:
- Isolate the incident and stop further unauthorised access/disclosure.
- Assess the scope of the breach, including what personal data is affected, which individuals, and what systems.
- Evaluate the risk to individuals (refer to ICO guidance).
- Decide whether notification is required, whether to governing bodies or data subjects, and document the decision making.
- Begin remediation immediately. Secure affected systems, recover/restore data if needed, and remove the root cause.
- Log and record all actions, communications, and timelines.
Each of these steps must be embedded in your incident response plan and exercised regularly.
Internal breach response roles and responsibilities
An effective response is not just IT led. There are important actions for senior leadership teams to get involved in and prepare for, making sure that:
- The entire executive team is aware and engaged.
- Legal and compliance teams are involved for notification obligations and contract liability assessments.
- The communications team is ready for stakeholder, media, and customer notifications where needed.
- Your IT and security teams handle the investigation, containment, forensics and remediation.
- Your data protection officer (DPO) or equivalent is involved in reporting and liaison with the ICO. Clear escalation pathways and defined responsibilities are essential.
Building a response plan: policy, people, process
Your incident response framework should cover:
- Policies that define what constitutes a breach, how it is reported internally, roles and responsibilities, and the escalation chain.
- People-centric controls, including staff training, awareness of phishing and social engineering, and clear lines of accountability.
- Process and technology for incident detection and monitoring, forensics, evidence gathering, vendor management, testing and simulations.
If you identify any internal gaps, for example, lacking 24/7 monitoring or forensic capability, it may make sense to outsource part or all of these functions to a trusted MSSP partner.

How DigitalXRAID Helps Prevent and Manage GDPR Breaches
This is how we at DigitalXRAID can support you as your strategic cyber partner, with CREST-, CHECK-, and NCSC-accredited services:
Phishing and social engineering exercises
We help train your workforce to recognise malicious emails, spoofed calls or texts, and business email compromise attacks. These are common precursors to GDPR-related breaches, and reducing this human risk layer is essential.
Managed SOC and breach detection
Our 24/7 managed SOC services provide early detection of unusual behaviour, unauthorised access and data-exfiltration attempts. We monitor, alert and support containment faster than many in-house teams can, which is crucial as time is of the essence when it comes to breach prevention.
Incident response and remediation support
In the event of a breach, we provide rapid specialist incident response support, including investigation, containment, root cause analysis, and remediation. Speed and expertise dramatically reduce your risk, your remediation costs, and your exposure.
Penetration testing and vulnerability reduction
We deliver CREST- and CHECK-accredited penetration testing services, simulating the real world attack paths that cybercriminals use to trigger personal data breaches. When you can demonstrate to the ICO that you had appropriate preventive measures in place, the regulatory outcome is often less severe.
Compliance support services
We support your ISO 27001 certification, helping you to build the ISMS and policies that underpin data protection excellence. The better your policies, training, and technical controls, the stronger your position when a breach occurs, and the more confidently you can demonstrate to regulators and stakeholders that you were breach prevention ready.
Prevent GDPR Breaches in Your Business
Now you have a thorough understanding of what a GDPR breach is, when you must act, how serious the consequences can be, and how your team should respond. But prevention is always better than a cure.
With DigitalXRAID as your cyber security service partner, you gain ongoing support across the full lifecycle of detection, review, incident response, recovery and compliance.
If you’d like to review your current security posture and exposure risk, build your incident response capability or strengthen your monitoring and prevention, speak with one of DigitalXRAID’s experts.
Get in touch with the team today and let us help you secure your data, protect your reputation, and reduce your risk.
FAQs About GDPR Breaches
What is considered a personal data breach under GDPR?
A personal data breach GDPR is when there is a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to personal data.
Is every data breach a GDPR breach?
No. If no personal data is involved, or the incident does not pose a risk to the rights and freedoms of individuals, it may not be a notifiable GDPR breach, but you must still record and assess it.
How long do you have to report a GDPR breach?
You must notify the ICO without delay, at the latest 72 hours after you become aware that a breach is notifiable.
Who do you report GDPR breaches to in the UK?
You report to the UK Information Commissioner’s Office (ICO) as the supervisory authority under UK GDPR.
What are the penalties for a GDPR breach?
Penalties can be significant. If you fail to comply with UK GDPR, you may face financial penalties, investigations, reputational harm, or legal claims.
Do you always have to tell the ICO about a breach?
Only if the breach is likely to result in a risk to the rights and freedoms of individuals. However, you must record all incidents and your rationale for reporting or not reporting.
How can managed services help prevent data breaches?
Managed services give you proactive monitoring, expert detection, and rapid response capability, reducing the chance that a breach goes undetected or spreads uncontrollably. Outsourcing to a specialist team gives you access to scale, depth of expertise, and regulatory alignment.
What sectors are most at risk of GDPR breaches?
Highly regulated sectors such as financial services, healthcare, public sector and those handling special-category personal data are at higher risk due to the volume and sensitivity of the data, regulatory scrutiny, and the complexity of third-party ecosystems.


