Microsoft Sentinel Data Lake: What IT Leaders Need to Know
IT and Security teams are under pressure from the growing volume of telemetry data, threats becoming more sophisticated, and regulatory requirements tightening. Yet budgets rarely scale at the same pace. As an IT and security leader, you need better visibility and forensic capability without adding spiralling costs. Microsoft’s latest update to its security ecosystem introduces a significant new feature that addresses these very challenges: the Microsoft Sentinel Data Lake.
Released in July 2025, this innovation enables long term storage of security logs within a dedicated data lake architecture, tightly integrated with Microsoft Sentinel and Microsoft Defender XDR. It allows your organisation to retain logs for up to 12 years, run queries across vast datasets, and power advanced detection and AI workloads – all while reducing storage and analytics costs.
In this guide, you’ll learn what the Microsoft Sentinel Data Lake is, how it works, the strategic advantages for your security operations, and how a cyber security service provider like DigitalXRAID can help you implement and optimise it.
Key Takeaways
- Microsoft Sentinel Data Lake provides cost-effective, long-term log storage
- It enables up to 12 years’ retention for threat hunting and compliance
- Cold tier data can be queried via KQL and promoted to the analytics tier
- Integrated with Defender Threat Intelligence and Microsoft Copilot for AI
- DigitalXRAID offers implementation and advisory support tailored to specific business requirements

What is Microsoft Sentinel Data Lake?
The Evolution of Microsoft Sentinel
Microsoft Sentinel has been at the forefront of cloud native Security Information and Event Management (SIEM) since its launch. It integrates across Microsoft 365, Azure, Microsoft Defender XDR, and hundreds of third party systems.
Its strength lies in its scalability, detection capabilities, and integration with Microsoft’s broader security suite.
Until recently, Microsoft Sentinel’s log storage capabilities were bound to its analytics tier. While this offered optimal results with a high degree of efficiency and speed, this tier can become expensive if you’re storing high volume or long retention datasets.
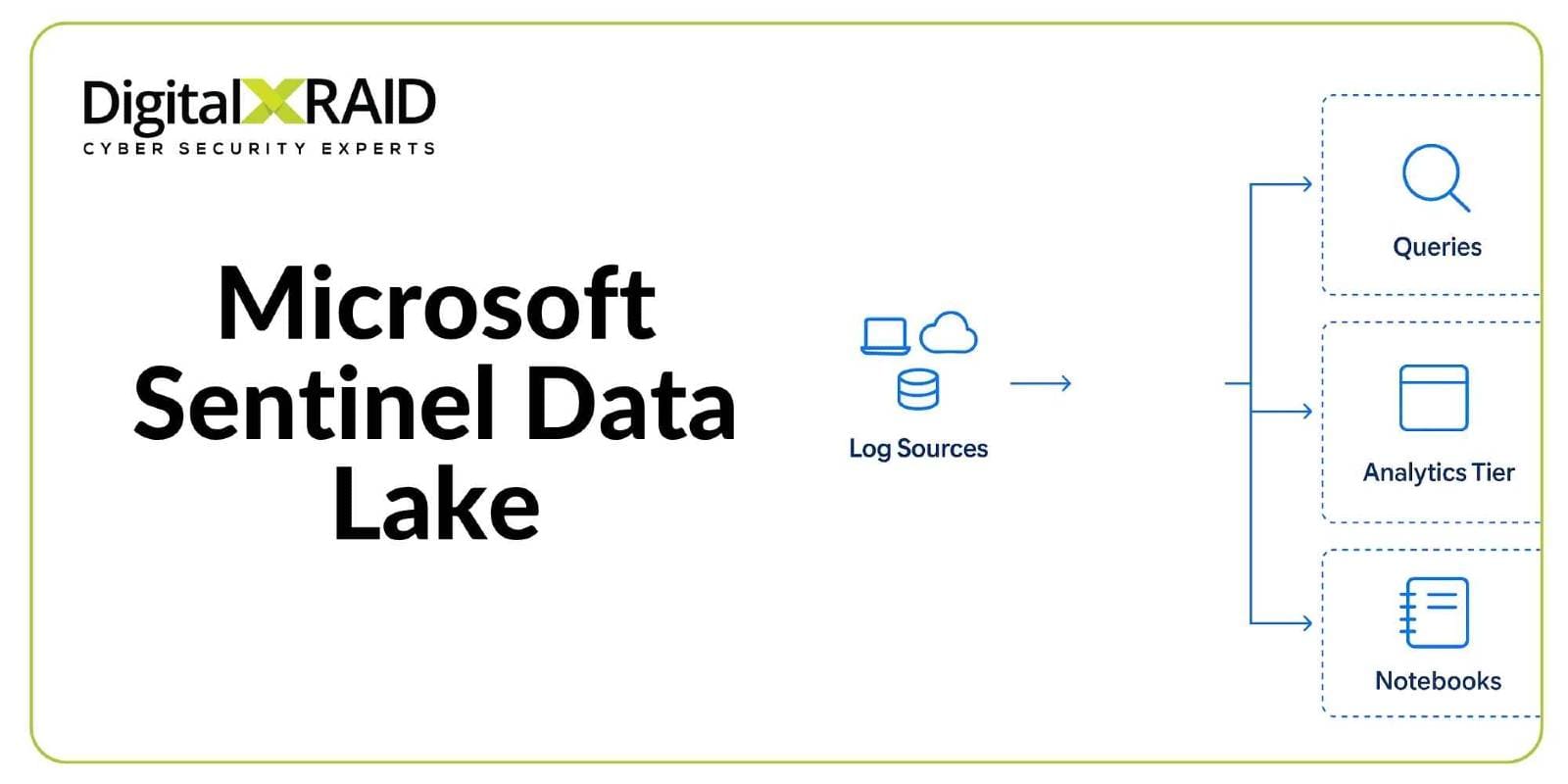
How the Data Lake Fits into the Microsoft Security Ecosystem
The Microsoft Sentinel Data Lake introduces a separate, cold storage tier that’s optimised for long term retention and cost efficiency. It lives within the Microsoft Defender portal and provides seamless integration with existing Sentinel connectors, table structures, and role based access controls.
This cold tier is ideal for any of your logs that are rarely accessed but must be stored for compliance or forensics. It also provides you with the ability to query historical data using Kusto Query Language (KQL) or promote relevant records back into the hot analytics tier for real time detection.
What’s New in the July 2025 Update?
Microsoft’s July 2025 release brought the following core features to its Security Suite:
- Public preview of Microsoft Sentinel Data Lake
- Native support for up to 12 years’ log retention
- Integration with Defender Threat Intelligence
- Built-in Jupyter notebook support for advanced analysis
- Visual Studio Code extensions for KQL and Spark
- New cost models separating analytics and cold tier data
These features provide a foundation for future enhancements, including AI-augmented detection and unified case management across Microsoft Sentinel and Defender XDR.
How Sentinel Data Lake Works – A Technical Breakdown
Analytics Tier vs. Data Lake Tier
Microsoft Sentinel now operates on a dual tier model:
- The analytics tier is designed for real time detection, dashboards, and alerting.
- The data lake tier is cold storage optimised for cost and scale, best suited to logs that require occasional access or long retention.
You can define custom policies to control which log types are ingested into each tier. Data in the cold tier can still be queried using scheduled KQL jobs or notebooks, or promoted to the analytics tier for deeper analysis.
Log Types and Tiering Strategies
A tiering strategy is essential. For example:
- High-fidelity logs like endpoint detection and response (EDR) telemetry may stay in the analytics tier for rapid correlation
- Low-fidelity, high volume logs like DNS requests, firewall traffic, and flow logs can be directed to the data lake
DigitalXRAID can help you to map your log sources to the appropriate tier based on your use cases, retention requirements, and detection relevance.
Querying Data with KQL and Jupyter Notebooks
You can explore data within the cold tier using familiar Kusto Query Language. For more advanced workloads, Microsoft now supports Jupyter notebooks, Python-based analysis, and Spark jobs, enabling statistical detection, enrichment, and pattern analysis across massive datasets.
This opens the door for proactive threat hunting over long timeframes, something previously cost prohibitive in traditional SIEM environments.
Retention, Compliance & Data Sovereignty
With up to 12 years’ data retention available, the Microsoft Sentinel Data Lake supports regulatory and industry specific obligations across multiple sectors.
For EU and UK based organisations, this includes:
- Financial services: Compliance with DORA and FCA guidance
- Critical infrastructure: Long term log storage for NIS2 compliance
- Data protection: GDPR and UK Data Protection Act alignment and sovereignty via UK region deployment
- Information security: Supporting ISO 27001 controls related to log review, monitoring, and retention
Benefits of Sentinel Data Lake for Cyber Security Operations
Cost Efficient Storage for Long Term Visibility
Storing every log in the analytics tier can quickly become very expensive. The new data lake offers you a cost efficient way to store less frequently used data, without losing visibility. In some use cases, cost reductions of 60-85% have been reported when offloading appropriate logs to the cold tier.
Retrospective Threat Hunting at Scale
Advanced persistent threats (APTs) often remain undetected for months. The Microsoft Sentinel Data Lake allows analysts to review logs beyond typical 90 day retention windows, enabling deeper investigations into long dwell time attacks.
Supporting Compliance
Security leaders operating under ISO 27001 certification will recognise the alignment with clause 12.4 (event logging) and clause 16.1 (incident management). Sentinel Data Lake allows you to retain evidence quality logs and demonstrate due diligence over extended periods.
For organisations operating in regulated sectors, this supports:
- DORA (Digital Operational Resilience Act) requirements for logging and operational continuity
- NIS2 directive obligations for incident detection and response
- The EU Cyber Resilience Act (CRA), particularly around maintaining traceability and accountability for incidents
Enabling AI and Automation in the SOC
Long term structured log storage is the backbone of AI-enhanced security operations. The Sentinel Data Lake powers Microsoft Copilot and other AI tooling with historical context, enabling better correlation, detection, and root cause analysis.

Common Use Cases for Sentinel Data Lake
Forensic Investigations & Incident Response
Retaining months or years of log data allows SOC teams to reconstruct incidents in detail. With proper tagging and indexing, analysts can pivot across logs with precision, accelerating containment and recovery.
Threat Detection Across Long Dwell Time Attacks
Nation-state or financially motivated attackers often dwell inside environments for extended periods. Cold tier access allows for threat hunting that can look back at 6 to 12 months of data, enabling early stage detection of lateral movement, privilege escalation, or beaconing behaviour.
Compliance Driven Log Retention
If you’re a UK based organisation, you’re required to retain logs for 1 to 6 years, particularly if you’re operating under FCA, NHS, or CNI frameworks. Sentinel Data Lake provides an efficient way to meet those mandates without impacting analytics performance.
Storing High-Volume, Low-Fidelity Logs (e.g. DNS, Flow)
These logs may not offer immediate detection value, but they’re vital for attribution, enrichment, and context during incident review. Offloading them to the cold tier ensures you maintain a full picture of network activity.
Checklist: Is your organisation ready for Sentinel Data Lake?
- Do you retain logs for more than 90 days?
- Are you concerned about SIEM cost growth?
- Do you need to support ISO 27001, or regulations such as NIS2 or DORA?
- Do you store large volumes of DNS, firewall or flow data?
- Are you investing in AI or Copilot-style automation?
If you answered yes to two or more, a move to Microsoft Sentinel Data Lake is worth serious consideration.
How to Enable Microsoft Sentinel Data Lake
To enable Microsoft Sentinel Data Lake, navigate to the Microsoft Defender portal and select System > Microsoft Sentinel > Data Lake. From there, initiate the onboarding wizard, configure the target Azure subscription and resource group, and enable data lake ingestion. Log tables can then be tiered using the new data management interface, allowing you to assign specific connectors or data types to either the analytics or cold-tier storage.
Initial provisioning typically completes within 30 to 60 minutes. Role based access and retention policies can be configured post deployment to align with your organisation’s governance model.
Why Work with a Cyber Security Service Provider?
DigitalXRAID’s Role in Helping You Design and Deploy Microsoft Sentinel
Implementing Microsoft Sentinel Data Lake isn’t just about turning on a feature. You need to evaluate log sources, configure ingestion rules, secure access, and develop detection and retention strategies.
DigitalXRAID’s analysts provide:
- Guidance on tiering strategies aligned to your risks and regulations
- KQL and data lake query support to get real value from cold data
- Assistance aligning logging with requirements from ISO 27001, DORA, and other industry specific obligations, where relevant
Real-World Support vs. Software Licensing
You’re not just buying a platform, you’re gaining an expert partner. Many vendors will help you enable a feature; DigitalXRAID ensures you derive outcomes. With CREST and CHECK accredited analysts and years of experience running Managed SOC Services, our support extends beyond configuration into actionable threat detection.
Planning Your Implementation: A Strategic Checklist
- Review current log volumes and data sources
- Define your compliance and retention goals
- Segment logs by fidelity, volume, and business impact
- Evaluate readiness of your SOC team for KQL and notebooks
- Build a migration plan or POC for cold-tier integration
- Engage a partner like DigitalXRAID to validate, test and deploy
Rate your maturity across log strategy, tooling, compliance, and team capability. Use this scorecard to prioritise your roadmap and justify budget internally.
Final Thoughts: Is Microsoft Sentinel Data Lake Right for Your Organisation?
If you’re struggling with ballooning SIEM costs, compliance pressures, or limited threat visibility, the Microsoft Sentinel Data Lake offers a compelling way forward. It brings scale, retention, and AI-readiness into the core of your operations.
But it’s not a silver bullet. Real success depends on the strength of your tiering strategy, the quality of your queries, and how well your team adapts. That’s where working with a cyber security service provider adds value.
Get Expert Support to Maximise Microsoft Sentinel Data Lake
DigitalXRAID is here to help you unlock the full value of Microsoft Sentinel’s latest capabilities.
Whether you’re evaluating your options, or you’re ready to deploy, our analysts are on hand to support you every step of the way. Get in touch with DigitalXRAID today.
FAQs
How to reduce Sentinel SIEM costs with Data Lake tier?
You can reduce costs by storing high-volume, low-fidelity logs (like DNS and firewall traffic) in the Data Lake tier instead of the analytics tier, significantly lowering ingestion and retention costs without sacrificing access to the data.
Can I query historical logs using Sentinel Data Lake?
Yes, you can run Kusto Query Language (KQL) searches or Jupyter notebooks directly against cold-tier data, enabling retrospective threat hunting and forensic investigations across extended timeframes.
Differences between Sentinel analytics vs. data lake tiers
The analytics tier is used for real-time detection and alerting, while the data lake tier is optimised for long-term storage and batch querying. The data lake is more cost-effective but not designed for immediate alerting.
How long can I retain logs in Sentinel Data Lake?
You can retain logs in the Microsoft Sentinel Data Lake for up to 12 years, supporting regulatory compliance and long-term forensic analysis.
What is Microsoft Sentinel Data Lake preview?
The Microsoft Sentinel Data Lake preview is the early access release of Microsoft’s new cold tier log storage capability, allowing UK organisations to retain large volumes of data cost-effectively while testing its features before general availability.
Enabling Defender Threat Intelligence within Sentinel Data Lake
Defender Threat Intelligence integrates natively with Sentinel, enriching logs and alerts with IOCs and context. This integration is automatically enabled and available at no extra cost from October 2025.
Using Jupyter notebooks with Microsoft Sentinel Data Lake
Jupyter notebooks are supported within the Sentinel environment and can be used to run advanced analytics, automate batch queries, and conduct machine learning-based threat detection on cold-tier data.
Sentinel data lake audit logs for compliance UK
Audit logs stored in the Sentinel Data Lake can help UK organisations meet compliance requirements for frameworks like ISO 27001, NIS2, and GDPR by enabling secure, long-term access to log data.
Is Sentinel Data Lake supported in UK West region?
Yes, Microsoft Sentinel Data Lake is supported in UK-based Azure regions, including UK West, making it suitable for organisations with data sovereignty and residency requirements.
How to tier DNS and firewall logs into Sentinel Data Lake
You can configure data connectors to direct DNS and firewall logs to the cold tier using custom ingestion policies, which DigitalXRAID can help you implement as part of your logging strategy.


