Threat Pulse – January 2026
Each month, DigitalXRAID’s Security Operations Centre (SOC) analysts share the top threats affecting businesses globally. Take action to protect your organisation against these prolific threats.
If you’ve been affected by any of these threats, we’re here to help. You can call our Cyber Emergency line any time of the day or night for help with active cyberattacks.
DigitalXRAID’s SOC analysts constantly monitor for zero-day threats and update our signature databases using the most comprehensive Threat Intelligence and Open Threat Exchange databases available worldwide.
Cyber Incidents in January
APT28’s “Operation Neusploit”
In late January 2026, the Russian state linked advanced persistent threat group called APT28 (also known as Fancy Bear, UAC-0001, Sofacy or STRONTIUM) launched a sophisticated espionage operation, now tracked as Operation Neusploit.
This campaign centred on exploiting a newly disclosed Microsoft Office zero-day vulnerability (CVE-2026-21509) in RTF document parsing. Attackers embedded specially crafted malicious RTF files in spear phishing emails that automatically triggered the flaw without macros, allowing arbitrary code execution when opened by targeted users.
Within days of Microsoft issuing an emergency patch at the end of January, APT28 was seen delivering multi-stage malware – ranging from backdoors like MiniDoor and CovenantGrunt to email-stealing components – against government, military and transport entities across Central and Eastern Europe.
The operation demonstrated refined TTPs including cloud based command and control (abusing legitimate file services to mask malicious traffic), in-memory execution, encrypted payload delivery sequences, and geo-localised social engineering attacks, enabling long term access while minimising detection.
Mustang Panda’s Updated CoolClient Backdoor Campaign
In January 2026, the China aligned espionage group often tracked as Mustang Panda (also referred to by some researchers as HoneyMyte or Bronze President) significantly updated its CoolClient backdoor framework and deployed it in active campaigns targeting governments and officials worldwide.
The revamped CoolClient consists of a modular, multi-stage execution chain that uses DLL sideloading of legitimate signed binaries to bootstrap malicious components. Once resident, the backdoor is capable of credential harvesting, clipboard interception, browser data theft, and covert telemetry exfiltration, which has enabled the group to retrieve sensitive credentials, system and network information, and potentially confidential files from infected endpoints.
Analysts reported that Mustang Panda’s more recent variants also integrate enhanced process hollowing techniques and expanded plugin modules to conduct surveillance, keylogging, and remote shell access, reflecting broader TTP sophistication consistent with state level espionage objectives.
China Aligned Hackers Deploy PeckBirdy JavaScript Framework in Multi Target Cyber Campaigns
China-aligned APT actors have used a JavaScript based command and control framework called PeckBirdy since 2023 to target gambling sites, Asian government entities, and private organisations.
The framework abuses living-off-the-land binaries to run across multiple environments (browsers, MSHTA, WScript, .NET, Node.js) and is delivered through injected websites that serve fake Google Chrome update pages or credential harvesting scripts.
Two campaigns, SHADOW-VOID-044 and SHADOW-EARTH-045, deployed PeckBirdy to distribute modular backdoors (HOLODONUT and MKDOOR), steal cookies, exploit known Chrome flaws, and enable lateral movement.
Infrastructure links and tool overlaps suggest ties to multiple China-aligned threat groups, highlighting how flexible, script based frameworks can evade traditional security controls.
Google Presentations Abused for Phishing
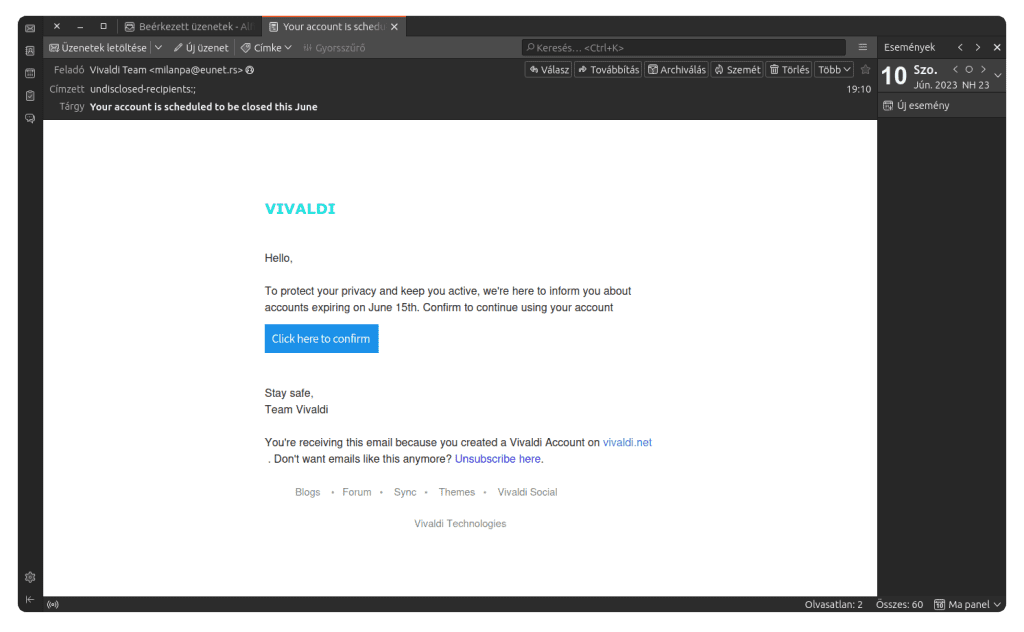
A phishing email was identified that targeted users of the Vivaldi webmail service. While the message itself wasn’t particularly convincing, it was likely good enough to deceive some users.
The attack became more interesting after clicking the link in the email. Instead of immediately leading to a phishing page, the link opened a Google Slides presentation hosted on Google Docs. Normally, Google Docs displays clear warnings and reporting options when content is suspected of phishing. In this case, those warnings were absent, not due to a bug, but because of how the document was shared.
By publishing the slides rather than sharing them in edit or preview mode, the attackers removed the Google Docs footer that would normally reveal the content as a presentation and display safety warnings. Since the slideshow consisted of only one slide, the auto-advance behaviour introduced by publishing didn’t raise suspicion. Additional settings were used to prevent looping and delay slide changes, making the page appear static and legitimate.
From the Google Slides page, victims were redirected to a traditional phishing login form built using Square and hosted on a simple website builder platform. At the time of reporting, the phishing page was still active.
Microsoft Office Zero-Day CVE-2026-21509 – Emergency Patch Issued for Active Exploitation
Microsoft on Monday issued out-of-band security patches for a high-severity Microsoft Office zero-day vulnerability exploited in attacks.
The vulnerability, tracked as CVE-2026-21509, carries a CVSS score of 7.8 out of 10.0. It has been described as a security feature bypass in Microsoft Office.
“Reliance on untrusted inputs in a security decision in Microsoft Office allows an unauthorised attacker to bypass a security feature locally,” the tech giant said in an advisory.
“This update addresses a vulnerability that bypasses OLE mitigations in Microsoft 365 and Microsoft Office, which protect users from vulnerable COM/OLE controls.”
Successful exploitation of the flaw relies on an attacker sending a specially crafted Office file and convincing recipients to open it. It also noted that the Preview Pane is not an attack vector.
The Windows maker said customers running Office 2021 and later will be automatically protected via a service side change, but will be required to restart their Office applications for this to take effect.
Microsoft hasn’t shared any details about the nature and the scope of attacks exploiting CVE-2026-21509. It credited the Microsoft Threat Intelligence Center (MSTIC), Microsoft Security Response Center (MSRC), and Office Product Group Security Team for discovering the issue.
The development has prompted the US Cybersecurity and Infrastructure Security Agency (CISA) to add the flaw to its Known Exploited Vulnerabilities (KEV) catalogue, requiring Federal Civilian Executive Branch (FCEB) agencies to apply the patches by 16 February 2026.
Voice Phishing Okta Customers: ShinyHunters Claims Credit
Okta warned customers that cybercriminals are using subscription based vishing toolkits to socially engineer victims into approving MFA requests or sharing one time passwords, often armed with knowledge of a company’s IT helpdesk and authentication apps.
According to Hudson Rock CTO Alon Gal, the extortion group ShinyHunters claimed responsibility, targeting organisations using Okta SSO and accessing data in cloud services like Salesforce.
Reported victims include Betterment, Crunchbase, and SoundCloud, with leaked data allegedly containing personal and corporate information such as signed contracts. ShinyHunters is linked to the loosely organized cybercrime collective known as The Com, which frequently uses IT staff impersonation in phone-based attacks.
New PyRAT Malware Spotted
A new Python-based remote access trojan (RAT) called PyRAT has been found to demonstrate cross platform capabilities, persistent infection methods, and extensive remote access features. It supports features like system command execution, file system operations, file enumeration, file upload/download, and archive creation to facilitate bulk exfiltration of stolen data.
The malware also comes fitted with self-cleanup capabilities to uninstall itself from the victim machine and wipe all persistence components. “This Python‑based RAT poses a notable risk to organizations because of its cross‑platform capability, broad functionality, and ease of deployment,” K7 Security Labs said. “Even though it is not associated with highly sophisticated threat actors, its effectiveness in real‑world attacks and observed detection rates indicate that it is actively used by cybercriminals and deserves attention.”
It’s currently not known how it’s distributed.
Potential Data Breach Impacting Major Sportswear Company Nike
Nike confirmed it is investigating a major cybersecurity incident in January 2026 after the hacker group WorldLeaks claimed to have stolen around 1.4 TB of internal company data, including product design, internal documents, and manufacturing details.
The breach has not been conclusively verified by Nike officials, and it’s not clear whether customer or athlete related information was exposed, but the incident highlights heightened cyber risk to companies tightly connected to professional sports through sponsorship, equipment, and brand partnerships.
Zoom
On 20 January 2026, Zoom published a security bulletin for CVE-2026-22844, a critical command injection vulnerability affecting Zoom Node Multimedia Routers (MMRs) in Zoom Node deployments.
The issue could potentially enable remote code execution against affected MMR versions prior to the fixed release.
Ransomware and Malware Activity Affecting Manufacturing Sector Threat Landscape
Throughout January 2026, threat intelligence reports highlighted ongoing ransomware and malware activity involving manufacturing organisations.
Security researchers observed ransomware strains such as Karma (MedusaLocker) being discussed and leveraged on underground forums in campaigns targeting multiple sectors, including manufacturing. This reflects broader adversary interest in exploiting vulnerabilities in industrial environments and IT networks that support manufacturing operations.
Kensington and Chelsea Council Cyberattack (UK)
In mid-January 2026, Royal Borough of Kensington and Chelsea Council confirmed a cyberattack that exposed sensitive personal data and disrupted internal systems, underscoring vulnerabilities in local government IT environments.
Experts pointed to shared infrastructure risks and gaps in security practises that public sector bodies must urgently address.
TridentLocker Ransomware Breach at Government-Focused Contractor
On 4 January 2026, claims administration provider Sedgwick acknowledged a data breach at its government servicing subsidiary tied to the TridentLocker ransomware gang, which said it exfiltrated about 3.4 GB of sensitive government-related data.
The incident highlights ongoing risks to public services from supply chain and third-party cybersecurity failures.
UK National Cyber Security Centre Warns of Hacktivist Activity
In January, the National Cyber Security Centre (NCSC) and other UK authorities issued warnings that pro-Russia hacktivist groups are actively targeting UK infrastructure and public services with disruptive cyber operations.
These alerts noted increased attempts to impact operational technology, utilities, transport, and essential services, signalling rising geopolitical cyber tensions affecting national resilience.
Industry Reports Highlight Broad Utility Cyber Threat Risks
Surveys and government data released in January indicated that a substantial proportion of utilities firms face cybersecurity challenges, with many reporting breaches in the past 12 months, reflecting an ongoing high risk environment for essential services.
National regulators also emphasised the importance of enhanced cyber resilience and compliance as attacks on critical infrastructure continue to escalate.
Supply Chain and Infrastructure Attacks
Beyond specific threat actors, January 2026 also exhibited broader infrastructure level exploitation trends, including attacks on enterprise mobility management platforms and breaches of IT administrative services.
Critical vulnerabilities in platforms like Ivanti’s EPMM and outdated endpoint management tools were actively targeted, enabling attackers to gain initial footholds in enterprise networks.
Additionally, incidents such as intrusions into government mobile device management infrastructure underscored the increasing attractiveness of supply chain and administrative systems for lateral expansion and data harvesting.
These patterns align with a larger shift towards combining low level service exploitation with sophisticated social engineering, to maximise access persistence and evade traditional defences.
Rising Social Engineering and AI-Driven Threats to the Tech Industry
January 2026 also saw heightened warnings about advanced social engineering and AI-assisted phishing threats aimed at technology companies. Security firms reported attackers using detailed knowledge of corporate IT processes and authentication methods to trick employees into approving malicious access requests.
These evolving tactics underscored how identity systems and cloud-based services had become primary targets for cybercriminal activity during the month.
DigitalXRAID exists to ensure that the bad guys don’t win. We’re driven and motivated to protect customers. Our expertise and unrivalled service means we can take care of your security, while you take care of business.
Talk to the team to see how you can start protecting your business against cyberattacks today.

